
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
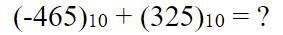
Transcribed Image Text:(-465)10 + (325)10 = ?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- def main(): # Find the least number among three numbers L = [] num1 = eval(input("Enter the first number:")) L.append(num1) num2 = eval(input("Enter the second number:")) L.append(num2) num3 = eval(input("Enter the third number:")) L.append(num3) print("The smallest number among the three is:",str(min(L))) main() Convert the above TUI Python program to a GUI form. You may use any of the widgets that support Tkinter module.arrow_forward01 == 0000 0001 What does this do???????arrow_forwardSum of two squares def sum_of_two_squares(n): Some positive integers can be expressed as a sum of two squares of some positive integers greater than zero. For example, 74 = 49 + 25 = 7^2 + 5^2. This function should find and return a tuple of two positive integers whose squares together add up to n, or return None if the parameter n cannot be broken into a sum of two squares.To facilitate the automated testing, the returned tuple must present the larger of its two numbers first. Furthermore, if some integer can be broken down to a sum of squares in several ways, return the breakdown that maximizes the larger number. For example, the number 85 allows two such representations 7^2 + 6^2 and 9^2 + 2^2 , of which this function must return (9, 2).The technique of two approaching indices that start from the beginning and end of a sequence, respectively, and approach each other until they meet somewhere is directly applicable to this problem. In this problem, these indices crawl towards each…arrow_forward
- Health application: BMI) Revise Listing 3.4, ComputeAndInterpretBMI.java, to let the user enter weight, feet, and inches. For example, if a person is 5 feet and 10 inches, you will enter 5 for feet and 10 for inches. Here is a sample run: Enter weight in pounds: 140 Enter feet: 5 Enter inches: 10 BMI is 20.087702275404553arrow_forwardINT_MIN = -32767 def cut_rod(price): """ Returns the best obtainable price for a rod of length n and price[] as prices of different pieces """ n = len(price) val = [0]*(n+1) # Build the table val[] in bottom up manner and return # the last entry from the table for i in range(1, n+1): max_val = INT_MIN for j in range(i): max_val = max(max_val, price[j] + val[i-j-1]) val[i] = max_val return val[n] # Driver program to test above functionsarr = [1, 5, 8, 9, 10, 17, 17, 20].arrow_forward2184=9100(.03*t)arrow_forward
- def is_balanced(root): return __is_balanced_recursive(root) def __is_balanced_recursive(root): """ O(N) solution """ return -1 != __get_depth(root) def __get_depth(root): """ return 0 if unbalanced else depth + 1 """ if root is None: return 0 left = __get_depth(root.left) right = __get_depth(root.right) if abs(left-right) > 1 or -1 in [left, right]: return -1 return 1 + max(left, right) # def is_balanced(root):# """# O(N^2) solution# """# left = max_height(root.left)# right = max_height(root.right)# return abs(left-right) <= 1 and is_balanced(root.left) and# is_balanced(root.right) # def max_height(root):# if root is None:.arrow_forwardI need the answer quicklyarrow_forwardCaesars Cypher in C programming language How do you program an encryption and decryption for a Caesars Cypher that covers all the possible ASCII characters? In this there should be a shift over K = 5 but the example below is K = 3. This should result in actual character and not the control ASCII represenations. For example: >>> $ encrypt(I have a key)N%mf{j%f%pj~>>> $ encrypt(see me at 3)xjj%rj%fy%8>>> $ decrpyt(|jfw%ns%gqzj)wear in blue Assume that the text parsing method has been succesful and it's the encryption/decryption of the char array that needs to be factored. Formula Encryption -> C = E(k, P) = (P + k) (mod 26) Decryption -> P = D(k, C) = (C - k) (mod 26) Where k = 5arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education