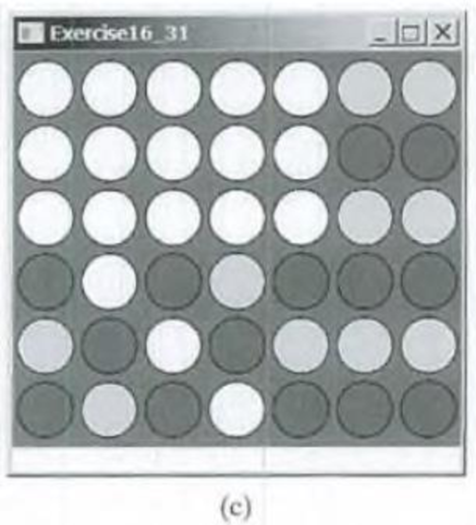
(Game: connect four)
Want to see the full answer?
Check out a sample textbook solution
Chapter 16 Solutions
Introduction to Java Programming and Data Structures: Brief Version (11th Global Edition)
Additional Engineering Textbook Solutions
Web Development and Design Foundations with HTML5 (9th Edition) (What's New in Computer Science)
Computer Systems: A Programmer's Perspective (3rd Edition)
Software Engineering (10th Edition)
Starting Out with Python (3rd Edition)
Starting out with Visual C# (4th Edition)
Starting Out with Java: From Control Structures through Objects (6th Edition)
- • Use a while loop • Use multiple loop controlling conditions • Use a boolean method • Use the increment operator • Extra credit: Reuse earlier code and call two methods from main Details: This assignment will be completed using the Eclipse IDE. Cut and paste your code from Eclipse into the Assignment text window. This is another password program. In this case, your code is simply going to ask for a username and password, and then check the input against four users. The program will give the user three tries to input the correct username-password combination. There will be four acceptable user-password combinations: • alpha-alpha1 • beta-beta1 • gamma-gamma1 • delta - delta1 If the user types in one of the correct username-password combinations, then the program will output: "Login successful." Here are a couple of example runs (but your code needs to work for all four user-password combinations): Username: beta Type your current password: beta1 Login successful. Username: delta Type…arrow_forwardHow many times does the inner loop execute during BubbleSort's first pass through the array?arrow_forwardThis test can only be taken once. Force Completion This test can be saved and resumed at any point until time has expired. The timer will continue to run if you leave the test. Your answers are saved automatically. • Show Timer ¥ Question Completion Status: QUESTION 1 What is the difference between a while loop and a do-while loop? O while loop checks the condition before the loop begins, whereas the do-while loop executes the body at least once before checking the condition. O while loop is used for counter-controlled and do-while, is used for a sentinel loop. O while loop is used for selection controlled and do-while is used for an infinite loop. O while loop is used for endless controlled control and do-while, is used for counter-controlled loop. Save All Ans Click Save and Submit to save and submit. Click Save All Answers to save all answers. DELLarrow_forward
- createDatabaseOfProfiles(String filename) This method creates and populates the database array with the profiles from the input file (profile.txt) filename parameter. Each profile includes a persons' name and two DNA sequences. 1. Reads the number of profiles from the input file AND create the database array to hold that number profiles. 2. Reads the profiles from the input file. 3. For each person in the file 1. creates a Profile object with the information from file (see input file format below). 2. insert the newly created profile into the next position in the database array (instance variable).arrow_forwardPHONE DIRECTORYDescription: Create a phonebook directory that will store the contact numbers of N persons. Your program should allow the user to add, view, delete, and update the contacts in the phonebook. Note that one person can have multiple contact numbers. The program will stop when the user command is ‘X’. Program command and entry should not be case-sensitive. That means commands ‘I’ or ‘i’ and the name “Jacky” or “JACKY” are the same. Each contact number can be 7 digits or 11 digits only. The user should input a string containing the command, name, and contact number(s) (Limit the contact number of each person to three). This string should be broken down into fields in order to separate the different values and store them in their appropriate variables. Use linked list in the implementation. Your node must declare at least four instance variables. Program flow: Command> I Jacky 09211234567 Remarks: New contact has been added. Command> V Jacky Contact…arrow_forwardgetRandomLib.h: // This library provides a few helpful functions to return random values// * getRandomInt() - returns a random integer between min and max values// * getRandomFraction() - returns a random float between 0 and 1// * getRandomFloat() - returns a random float between min and max values// * getRandomDouble() - returns a random double between min and max values// * getRandomBool() - returns a random bool value (true or false)// * getRandomUpper() - returns a random char between 'A' and 'Z', or between min/max values// * getRandomLower() - returns a random char between 'a' and 'z', or between min/max values// * getRandomAlpha() - returns a random char between 'A' and 'Z' or 'a' and 'z'// * getRandomDigit() - returns a random char between '0' and '9', or between min/max values// * getRandomChar() - returns a random printable char//// Trey Herschede, 7/31/2019 #ifndef GET_RANDOM_LIB_H#define GET_RANDOM_LIB_H #include <cstdlib>#include <random>#include…arrow_forward
- Implement a program to achieve the rotation of an n x n image clockwise OR counter-clockwise by 90 degrees. The resolution of the image, n, is entered by the user. You can safely assume that n is no more than 10. The image will be simulated using an n x n 2D matrix, also entered by the user. The input format is as follows an integer n, representing the image resolution matrix, representing the 2D image 0 or 1, representing the clockwise or counter-clockwise rotation EX1: if the user enters 3 1 2 3 456 780 0 After rotating the matrix in the clockwise orientation by 90 degrees, the output matrix is 741 852 063 EX2: if the user enters 4 5 1 9 11arrow_forwardwrite the code to lookup, add and remove phoneentries from the phonebook text file . These are the code we use for the lookup, add and remove in the case statement.(Lookup)# Look someone up in the phone bookgrep $1 phonebook (add)echo "$1 $2" >> phonebooksort -o phonebook phonebook (Remove)grep -v "$1" phonebook > /tmp/phonebookmv /tmp/phonebook phonebook Write a complete Bash script which will accept up to three command-line arguments: the first one is either (lookup, add or remove), the second one is a name enclosed in single quotes and the third one (if doing an add) is a phone number enclosed in single quotes. Using a case statement to match on either lookup, add or remove, the script should then perform the requested operation. Again here, you should first check for null arguments before continuing with the rest of the script or requested operation. In addition, the person may not be in the phonebook for lookup or remove so, you need to account for this.arrow_forwardAttached Files: getRandomLib.h: // This library provides a few helpful functions to return random values // * getRandomInt() - returns a random integer between min and max values // * getRandomFraction() - returns a random float between 0 and 1 // * getRandomFloat() - returns a random float between min and max values // * getRandomDouble() - returns a random double between min and max values // * getRandomBool() - returns a random bool value (true or false) // * getRandomUpper() - returns a random char between 'A' and 'Z', or between min/max values // * getRandomLower() - returns a random char between 'a' and 'z', or between min/max values // * getRandomAlpha() - returns a random char between 'A' and 'Z' or 'a' and 'z' // * getRandomDigit() - returns a random char between '0' and '9', or between min/max values // * getRandomChar() - returns a random printable char // // #define GET_RANDOM_LIB_H #include <cstdlib> #include <random> #include <ctime> using namespace…arrow_forward
- Virus DNA files As a future doctor, Jojo works in a laboratory that analyzes viral DNA. Due to the pandemic During the virus outbreak, Jojo received many requests to analyze whether there was any viral DNA in the patient. This number of requests made Jojo's job even more difficult. Therefore, Jojo ask Lili who is a programmer for help to make a program that can read the file containing the patient's DNA data and viral DNA and then match them. If on the patient's DNA found the exact same string pattern, then write to the index screen the found DNA. Data contained in the file testdata.in Input Format The first line of input is the number of test cases TThe second row and so on as many as T rows are the S1 string of patient DNA and the S2 string of viral DNA separated by spaces Output Format The array index found the same string pattern. Constraints 1 ≤ T ≤ 1003 ≤ |S2| ≤ |S1| ≤ 100|S| is the length of the string.S will only consist of lowercase letters [a-z] Sample Input (testdata.in)…arrow_forwardWrite an application that stores the following nine integers in an array: 10, 15, 19, 23, 26, 29, 31, 34, 38. Display the integers from first to last, and then display the integers from last to first.arrow_forwardGameAA.java This program allows a user to play “Rock, paper, scissors” against the computer. Use a random number generator to generate the computer’s selection. Your code should ask the user what they choose and then report the computer’s choice and who wins. This code should run in a loop and should end when the user chooses to end. (Make sure your random number generator chooses a new number each time the loop runs.) ALSO, your code should keep track of the number of times you win, the number of times you lose, and the number of ties. When the user exits, these statistics should be displayed. (Consider using a different counter variable to keep track of each value.) Make sure your code accounts for inputs that are out of the acceptable range. For example, if you ask the user to type 0 to end, 1 for Rock, 2 for Paper, and 3 for Scissors, your code should tell the user that they entered an invalid choice if they select 4. (You do not have to account for users who crash the…arrow_forward
 EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
