
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
How would the table look like if we used separate chaining (open hashing)
Transcribed Image Text:### Problem Statement
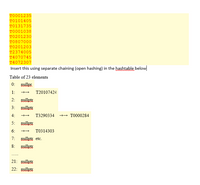
Insert the following keys using separate chaining (open hashing) in the hash table below:
- T0001235
- T0101405
- T0131735
- T0001038
- T0201230
- T0807000
- T0201203
- T2374005
- T4070745
- T4072307
### Hash Table Structure
#### Table of 23 Elements
- **Index 0:** `nullptr`
- **Index 1:** `nullptr` → T20107424
- **Index 2:** `nullptr`
- **Index 3:** `nullptr`
- **Index 4:** `nullptr` → T3290334 → T0000284
- **Index 5:** `nullptr`
- **Index 6:** `nullptr` → T0314303
- **Index 7:** `nullptr`
- **Index 8:** and so on (`etc.`)
- **Index 21:** `nullptr`
- **Index 22:** `nullptr`
### Diagram Explanation
The diagram illustrates a hash table using separate chaining, where collisions are handled by linking elements in a list. Each index in the table has either `nullptr` for empty slots or a linked structure showing the keys stored at that index. For example, at index 4, two keys are chained: T3290334 and T0000284. Using open hashing, multiple keys can be stored at the same index without overwriting.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Why do Rainbow Tables use a different reduction function for each step in the hash chain?arrow_forwardCan m-linked-lists be used to create a hash table? Why do we need a hash function, exactly? Provide an illustration.arrow_forwardWith Hash tables we have chaining and open addressing. What are the algorithms for both?how you would insert or search a hash table under either approach? Please give me examples of how I would code these algorithmsarrow_forward
- How many linked lists does a chaining hash table of size T have in total? To what extent does Separate Chaining's hash table accommodate primitive data types?arrow_forwardFind any two practical applications of hashing, investigate them exhaustively, and then describe them in detail. a. Do you also include references from your own research?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education