
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Transcribed Image Text:1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
A
B
End Function
C
JTAN
KANT
KCLI
JPAO
WCHA
RALV
CKNI
RRIV
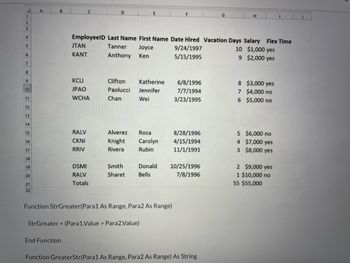
EmployeelD Last Name First Name Date Hired Vacation Days Salary Flex Time
Tanner
9/24/1997
10 $1,000 yes
Joyce
Ken
Anthony
5/15/1995
9 $2,000 yes
D
DSMI
RALV
Totals
Clifton
Katherine
Paolucci Jennifer
Chan
Wei
Alverez
Rosa
Knight Carolyn
Rivera
Rubin
Smith
Sharet
Function StrGreater (Para1 As Range, Para2 As Range)
StrGreater = (Para 1.Value > Para2.Value)
6/8/1996
7/7/1994
3/23/1995
8/28/1996
4/15/1994
11/1/1991
Donald 10/25/1996
Bells
7/8/1996
H
Function GreaterStr(Para1 As Range, Para2 As Range) As String
8 $3,000 yes
7 $4,000 no
6
$5,000 no
5 $6,000 no
4 $7,000 yes
3 $8,000 yes
2 $9,000 yes
1 $10,000 no
I
55 $55,000
J
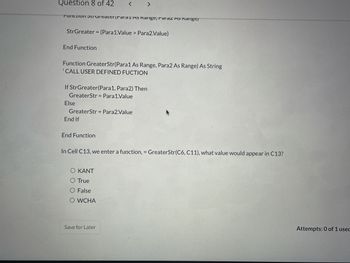
Transcribed Image Text:Question 8 of 42
Function StrGreaterrdi di AS Rarige, Faldz AS Range/
StrGreater = (Para1.Value> Para2.Value)
End Function
Function GreaterStr(Para1 As Range, Para2 As Range) As String
'CALL USER DEFINED FUCTION
If StrGreater(Para1, Para2) Then
GreaterStr Para1.Value
Else
< >
GreaterStr = Para2.Value
End If
Function
In Cell C13, we enter a function, GreaterStr(C6, C11), what value would appear in C13?
Ο ΚΑΝΤ
O True
O False
O WCHA
Save for Later
Attempts: 0 of 1 used
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Please help me in this fast. I have to write a C++ function to which a vector is passed as argument and it returns the maximal difference between any two adjacent elements of the vector. Function prototype is given below. int maximalDiff(vector<int>&);arrow_forwardPlease help I need help making this function bool power_of_two( unsigned n) and I dont understand itarrow_forwardJupyter Notebook Fixed Income - Certicificate of Deposit (CD) - Compound Interest Schedule An interest-at-maturity CD earns interest at a compounding frequency, and pays principal plus all earned interest at maturity. Write a function, called CompoundInterestSchedule, that creates and returns a pandas DataFrame, where each row has: time (in years, an integer starting at 1), starting balance, interest earned, and ending balance, for an investment earning compoundedinterest. Use a for(or while) loop to create this table. The equation for theith year's ending balance is given by: Ei =Bi (1+r/f)f where: Ei is year i's ending balance Bi is year i's beginning balance (note: B1 is the amount of the initial investment (principal) r is the annual rate of interest (in decimal, e.g., 5% is .05) f is the number of times the interest rate compounds (times per year) The interest earned for a given year is Ei - Bi Note the term of the investment (in years) is not in the above equation; it is used…arrow_forward
- Given the following function, answer the two questions that follow CREATE OR REPLACE FUNCTION Cale Age (V ID IN Student Sid ID%TYPE)RETURN NUMBER ISV_Age NUMBER, BÉGINSELECT SYDATE - Std_DOB INTO V AgeFROM StudentWHERE Std_ID = V_ID;RETURN V age;END; (a)Wbat does the word IN in the function parameter list mean? (b)Winte a SOL test statement to call the function. You may make up a fake student ID.arrow_forwardQuestion 5 Write the code for the function printRoster, it should print out the contacts in a format similar to the example. You can use a range-based for-loop and auto to simplify the solution, if you wish. #include #include #include #include #include using namespace std; void printRoster(map>>& roster) { // Fill code here int main() { map>> roster; roster["ELCO"]["CS-30"]. emplace_back("Anthony Davis"); roster["ElCo"]"cS-30"j. emplace_back("Talen Horton-Tucker"); roster["ElCo"Ï"BUS-101"].emplace_back("LeBron James"); roster["SMC"]["CHEM-101"].emplace_back("Russell Westbrook"); printRoster(roster); return 0; Here is the sample output: ElCo BUS-101: LeBron James CS-30: Anthony Davis Talen Horton-Tucker SMC CHEM-101: Russell Westbrookarrow_forwardphytonarrow_forward
- QUESTION 6 Given the code: void a(int n) { if(n<1) { cout << n*2 < " "; return; } cout << n*2 << " "; a(n-1); } 1. Trace the function when n is 4.arrow_forwardImplement the following functions. Each function deals with null terminated C-Style strings. You can assume that any char array passed into the functions will contain null terminated data. Place all of the functions in a single file and then (in the same file) create a main() function that tests the functions thoroughly. You will lose points if you don't show enough examples to convince me that your function works in all cases. Please note the following: You may not use any variables of type string. This means that you should not #include <string>. Also, you may not use any c-string functions other than strlen(). If you use any other c-string functions, you will not get credit. Note, however, that functions such as toupper(), tolower(), isalpha(), isspace(), and swap() are NOT c-string functions, so you can use them. Also note that this prohibition is only for the functions that you are assigned to write. You can use whatever you want in your main() function that tests the…arrow_forwardUsing informal arguments: Write a function polynomial which implements a polynomial function of arbitrary integer order ?: ?(?)=?0+?1?+?2?2+⋯+???? The function should take ? as a formal argument and the constants {??} as informal arguments. You will have to use the *args function argument. The enumerate builtin function will also be convenient in order to get the power ? to go along with each ??. Recall, you can index tuples just like arrays by using [ ]. Test your function by plotting: ?(?)=1+2?2 over the range (-3,3).arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education