
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
Help with this java question:
Map<KeyType, ValueType> mapName = new HashMap<>();
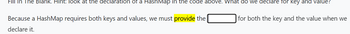
Transcribed Image Text:Fill In The Blank. Hint: look at the declaration of a HashMap in the code above. What do we declare for key and value?
Because a HashMap requires both keys and values, we must provide the
declare it.
for both the key and the value when we
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Java Code: Build the two variable classes that we need: InterpreterDataType and a subclass InterpreterArrayDataType. I will abbreviate these as IDT and IADT. IDT holds a string and has two constructors - one with and one without an initial value supplied. IADT holds a HashMap<String,IDT>. Its constructor should create that hash map. We will use these as our variable storage classes as the interpreter runs. Let's start the interpreter itself. Create a new class (Interpreter). Inside of it, we will have an inner class - LineManager. We will also need a HashMap<String,IDT> that will hold our global variables. We will also have a member HashMap<String, FunctionDefinitionNode> - this will be our source when someone calls a function. The LineManager should take a List<String> as a parameter to the constructor and store it in a member. This will be our read-in input file. It will need a method : SplitAndAssign. This method will get the next line and split it by looking…arrow_forwardEach of the iterators must implement the java.util.Iterator interface by providing the two public methods hasNext () and next(). The Iterator interface also lists two additional methods, remove () and forEachRemaining (). These are marked as default, so the interface itself does not require implementation. Of these methods, this assignment only requires you to implement the remove () method of the linked list iterator. 1 ArrayList iterator This is an external iterator, meaning it is a public class named ICS211ArrayListIterator, and and the code is not part of the ArrayList class. Your ICS211ArrayListIterator class should have a constructor ICS211ArrayListIterator(java.util.ArrayList gives access to all the elements of the array list. This array must be saved as the value of a class variable of the iterator. data). The constructor must call one of the two toArray methods of ArrayList to obtain an array that Other than this single call to java.util.ArrayList.toArray in the constructor,…arrow_forward7- question What keys and values are contained in the following map after execution of the following piece of code? Map map = new HashMap (); map.put (8, "Eight"); map.put (41, "Forty-one"); map.put (8, "Ocho"); map.put (18, "Eighteen"); map.put (50, "Fifty"); map.put (132, "OneThreeTwo"); map.put (28, "Twenty-eight"); map.put (79, "Seventy-nine"); map.remove ( 41); map.remove (28); map.put (28, "18"); map.remove (18); a. {8=Eight, 41=Forty-one, 8=0cho, 18=Eighteen, 50=Fifty, 132=OneThreeTwo, 28=Twenty-eight, 79=Seventy-nine, 28=18} b. {8=Eight, 8=Ocho, 50=Fifty, 132=OneThreeTwo, 79=Seventy-nine, 28=18} c. {50=Fifty, 132=DOneThreeTwo, 8=Ocho, 28=18, 79=Seventy-nine} d. {8=Eight, 50=Fifty, 132=OneThreeTwo, 79=Seventy-nine, 28=18}arrow_forward
- Can someone help me with this code, I not really understanding how to do this? import java.util.ArrayList;import java.util.HashMap;import java.util.Map;/*** @version Spring 2019* @author Kyle*/public class MapProblems {/*** Modify and return the given map as follows: if the key "a" has a value, set the key "b" to* have that value, and set the key "a" to have the value "". Basically "b" is confiscating the* value and replacing it with the empty string.** @param map to be edited* @return map*/public Map<String, String> confiscate(Map<String, String> map) {if (map.containsKey("a") && map.containsValue("a")) {}}/*** Modify and return the given map as follows: if the key "duck" has a value, set the key* "goose" to have that same value. In all cases remove the key "swan", the rest of the map* should not change.** @param map to be edited* @return map*/public Map<String, String> mapBird1(Map<String, String> map) {throw new UnsupportedOperationException("Not…arrow_forwardExplain why the code below does not run when using the test driver shown in screen shot. i also included the LLNode class and collectioninterface interface public class LinkedCollection<T> implements CollectionInterface<T> { protected LLNode<T> head; // head of the linked list protected int numElements = 0; // number of elements in this collection // set by find method protected boolean found; // true if target found, else false protected LLNode<T> location; // node containing target, if found protected LLNode<T> previous; // node preceding location public LinkedCollection() { numElements = 0; head = null; } public boolean add(T element) // Adds element to this collection. { LLNode<T> newNode = new LLNode<>(element); newNode.setLink(head); head = newNode; numElements++; return true; } protected void find(T target) // Searches the collection for an…arrow_forwardWhich of the following data structures cannot have an iterator implemented to iterate through? Group of answer choices 1. Hash Map 2. You can implement an iterator for all of these. 3. Linked List 4. Array 5. Binary Search Treearrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education