
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
python please
Do not need create the file"summer.txt", just need steps.
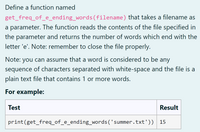
Transcribed Image Text:Define a function named
get_freq_of_e_ending_words(filename) that takes a filename as
a parameter. The function reads the contents of the file specified in
the parameter and returns the number of words which end with the
letter 'e'. Note: remember to close the file properly.
Note: you can assume that a word is considered to be any
sequence of characters separated with white-space and the file is a
plain text file that contains 1 or more words.
For example:
Test
Result
print(get_freq_of_e_ending_words('summer.txt'))
15
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- hello guys, please help me solving this python script Thanks for helping mearrow_forwardpythonarrow_forwardWith multine text, you can do all of the following, except * Insert numbered and bulleted lists insert photos Enter specific drafting and engineering symbols Create fields such as date, time and author. AutoCAD O Other:arrow_forward
- Create a new file cart.html You must get and set the data on the web page by using document.getElementById( ). Each HTML element on the web page already has an id so it is easy. No need for a loop to go through the list of products, there is only 2 products and the info is hard coded on the web page. You must write the code for function cartTotal().arrow_forwardIn Python, utilize the file pylang.txt (information included in the file py.lang.txt below) pylang.txt ————— Python language is incredibly easy to use and learn for new beginners and newcomers. The python language is one of the most accessible programming languages available because it has simplified syntax and not complicated, which gives more emphasis on natural language. Due to its ease of learning and usage, python codes can be easily written and executed much faster than other programming languages. ——————————————- Create a program that replaces every occurrence of a string from the file above with a user-selected word. The program should prompt user to enter the filename, a string to be substituted and a string to substitute it with. The program will open a file to read, then close the file. Replace one string with another, then open the file to write out the new string, then close it. Then finally, open the file to read again so the new context can be printed.…arrow_forwardCreate a new javascript file called cart.js and make a product object for each of your products and store it in a products array when the script loads. Create an empty array to store the items added to the cart. Program the "add to cart button" to take the product id, finds the product object in the products array and adds it to the items added to cart array. Program the "remove from cart button" to take the product id and remove the project object from the items purchased array. Existing code: <!DOCTYPE html><html> <head> <div id="product1" class="card"><img src="img/clorox.jpg"><h1>Clorox</h1><p class="price">$20.00</p><p>Household Cleaner</p><p><button id="product1Btn1">Add to Cart</button></p><p><button id="product1Btn2">Remove from Cart</button></p></div> <div id="product2" class="card"><img src="img/oxiclean.jpg"><h1>Oxiclean</h1><p…arrow_forward
- In PYTHON Write the code that will open and read the data from a file named Numbers.csv and write it to a file named justAsNumbers.csvarrow_forwardCode in C language. Please provide code for 3 different files. One header file and two .C files. I need the code for each file. Please provide photos of the output and source code for each file (3). Please follow All instructions in the photo provided. Use the provided input.txt file provided below. A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 B1, B2 19831 Henshaw St Culver City, CA 94023 C1, C2 5142 Dumont Pl Azusa, CA 91112 D1, D2 20636 De Forest St Woodland Hills, CA 91364 A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 E1, E2 4851 Poe Ave Woodland Hills, CA 91364 F1, F2 20225 Lorenzana Dr Los Angeles, CA 91111 G1, G2 20253 Lorenzana Dr Los Angeles, CA 90005 H1, H2 5241 Del Moreno Dr Los Angeles, CA 91110 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 J1, J2 5135 Quakertown Ave Thousand Oaks, CA 91362 K1, K2 720 Eucalyptus Ave 105 Inglewood, CA 89030 L1, L2 5021 Dumont Pl Woodland Hills, CA 91364 M1, M2 4819 Quedo Pl Westlake Village, CA 91362 I1, I2 5332 Felice Pl…arrow_forward2. Design the form as follow: File Edit View Git Project Build Debug Format Test Analyze Tools Debug Any CPU > Start - Form1.vb* Form1.vb [Design]" X o Sales App Month Enter the sales of each day in the month Read Sales in a month: O Note: - Add the following to the form: a. Three buttons b. Two labels c. One textboxe d. One listBox - Give appropriate names to the form, and controls Server Explorer Toolboxarrow_forward
- What header file must be included *Match* 1. to perform a mathematical function like sqrt 2. to use random numbers 3. to use random numbers 4. to use stream manipulators like setprecision A. iostream B. cmath C. iomanip D.cstdlibarrow_forwardFile Edit View Sign Window Help ECS401U_210571675.pdf ECS401U_210571... x 16 / 29 125% 罗ア白 ,班 a) Compare and contrast in your own words the way reading from a file using a File Reader is done in Java with keyboard input using a scanner illustrating your answer using the following example code fragments. Note you are not being asked to explain line by line what the code does but use it to help explain the points made in your answer. public static void keyboardInput () } new Scanner(System.in); Scanner scanner String s; System.out.println("Please input the data"); s = scanner.nextLine(); System.out.println(s ); return; { public static void fileRead () throws IOException BufferedReader inputStream new BufferedReader (new FileReader("data.csv")); inputStream.readLine(); String s = System.out.println(s); inputStream.close(); return; {arrow_forwardpython coding using pathlib, Separate the following path 'C:\Users\Barney\files\letters.txt' into the drive, the parent, file name, and the suffix (you can assign each to a variable or display on the screen from the .py (not the interactive shell))arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education