
Practice Problem 7.3 (solution page 718)
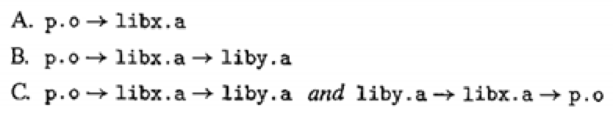
Let a and b denote object modules or static libraries in the current directory, and let a→b denote that a depends on b, in the sense that b defines a symbol that is referenced by a. For each of the following scenarios, show the minimal command line (i.e., one with the least number of object file and library arguments) that will allow the static linker to resolve all symbol references.
Want to see the full answer?
Check out a sample textbook solution
Chapter 7 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Additional Engineering Textbook Solutions
Introduction to Java Programming and Data Structures, Comprehensive Version (11th Edition)
Starting Out with Python (4th Edition)
Web Development and Design Foundations with HTML5 (9th Edition) (What's New in Computer Science)
Problem Solving with C++ (9th Edition)
Problem Solving with C++ (10th Edition)
Digital Fundamentals (11th Edition)
- PLEASE FOR FRIDAY 24 :( DMESG Analyzer Implement a system log analyzer and classifier for GNU/Linux. In this particular case, a sample log output file is provided. It's highly recommended to implement in a Linux-based operating system. This challenge involves a proper struct design choice for the logs classification and storing. Requirements The program must be implemented in the C programming language. You program will classify log entries by the <log_type>: prefix Those log entries that don't follow the <log_type>: convention will go to the General classification. Repeated log classes are not allowed. Use the dmesg-analyzer.c template The solution must use at least 3 of the following system calls: open() read() write() lseek() close() Don't forget to handle errors properly Sample Execution ./dmesg-analizer -input dmesg.txt -output dmesg_report.txt Sample Expected output file dmesg_report.txt General: [ 0.000000] Linux version 4.15.0-45-generic (buildd@lgw01-amd64-031)…arrow_forwardLet a and b denote object modules or static libraries in the currentdirectory, and let a → b denote that a depends on b , in the sensethat b defines a symbol that is referenced by a . For each of thefollowing scenarios, show the minimal command line (i.e., one with theleast number of object file and library arguments) that will allow thestatic linker to resolve all symbol references:A. p.o → libx.a → p.oB. p.o → libx.a → liby.a and liby.a → libx.aC. p.o → libx.a → liby.a → libz.a and liby.a → libx.a →libz.aarrow_forwardI'm having a hard time seeing the problem with this buffer overflow problem can someone please elaborate if its secure or not, and if there are any other issues with the implementation in the problem? Someone tries to fix the stack based buffer overflow problem as follows, is it secure now? why? Are there any other issues within the function's implementation below? Explain your reasoning. int bof(char *str, int size) { char *buffer = (char *) malloc(size); strcpy(buffer, str); return 1; }arrow_forward
- We can solve memory leaks with using a tombstone or lock and keys approach to the dangling pointer problem using a tombstone or mark-sweep approach to the dangling pointer problem some form of garbage collection such as mark-sweep or reference counters some form of garbage collection such as tombstones or lock-and-keysarrow_forwardConstruct a PDA for {a'b'|i # j}. State whether it is “accept by empty stack" or "accept by final state." Please also give a high-level description of your PDA. 7.arrow_forwardQ2: Besides the while-loop in Q1, I want to implement a 2nd while-loop running in parallel with the first while: while(1) { wt(1); XX); } However, on an MCU there is no parallelism. (For ex., on Arduino I can define only one loop() function.) Write a single while that does the job of both whiles. (a) Write it in a procedural style. (b) Write it the super-loop style (state-machine with fixed heartbeat).arrow_forward
- in C++... kth Element Extend the class linkedListType by adding the following operations:a. Write a function that returns the info of the kth element of the linked list. If no such element exists, terminate the program.b. Write a function that deletes the kth element of the linked list. If no such element exists, terminate the program. Provide the definitions of these functions in the class linkedListType. PLEASE DON'T reject this question, this is the whole question that I have... so please do it however u can, Thank you!arrow_forwardExercise 3 Here again is the example used to show the difference between scop- ing with blocks and dynamic scoping: fun g x - let val inc = 1; fun fy = y + inc; fun h z = let in end; hx in val inc = 2; end; in Copy it and then annotate it as follows: a. Draw a circle around every block, and number the blocks. b. Identify each definition of a name. c. For each definition, describe its scope in terms of your block numbers. d. For each occurrence of a name (other than a definition of that name), show which definition is used to bind it. Check that this agrees with your scopes. lint: Please refer to the answer to part (a) in the following diagram. fz fun gx = let val inc = 1; fun f Y = y + inc; 14 fun hz = let end; h x val inc = 2; in f z end; (O 6 5 2 1arrow_forward2.2.14 Sorted queues being combined. Create a static function that receives two queues of sorted items as inputs and returns a queue formed by combining the two queues into a single sorted order queue. 2.2.15 Bottom-up mergesort of a queue. Create an implementation of the bottom-up mergesort using the following strategy: Make N queues, each holding one of the N things, given N items. assemble the N queues into a queue. Apply Exercise 2.2.14's merging process to the first two queues several times, and at the conclusion, reinsert the combined queue.Continue until there is just one queue left in the queue of queues.arrow_forward
- Need help with these assignments, I use C++. Thank you. Lab 4: Declare and implement a BSTNode ADT with a data attribute and two pointer attributes, one for the left child and the other for the right child. Implement the usual getters/setters for these attributes. Declare and implement a BST as a link-based ADT whose data will be Dollar objects - the data will be inserted based on the actual money value of your Dollar objects as a combination of the whole value and fractional value attributes. For the BST, implement the four traversal methods as well as methods for the usual search, insert, delete, print, count, isEmpty, empty operations and any other needed. Your pgm will use the following 20 Dollar objects to be created in the exact order in your main to seed the tree: $57.12 $23.44 $87.43 $68.99 $111.22 $44.55 $77.77 $18.36 $543.21 $20.21 $345.67 $36.18 $48.48 $101.00 $11.00 $21.00 $51.00 $1.00 $251.00 $151.00 Also, create an output file to write program output as specified…arrow_forwardQUESTION 2 : Write C code to simulate the Long term scheduler to admit the processes with the following process mix criterion: a. Every PCB should contain two values : PID and type: (CPU Bound: 1, 10 bound: 0) b. The Ready queue should have 30%-40%, 10 bound process. c. On each Iteration, one PCB can be allowed to enter into the ready queue if the above criterion is being fulfilled, otherwise it is being held in other list. d. The held PCBS are later (after some specific time interval) again tried to push into ready queue. e. After each admission print the current status of Ready queue.arrow_forward12 13 Suppose we have a struct/class that only contains primitive types (short/int/long/bool/float/double/char) or pointers to these types. When passing a parameter of this type by value (as C and C++ let you do), static type checking is always possible the types of the pointer fields must be checked dynamically if they point to an array of values type checking must be done dynamically c the types of the pointer fields must be checked dynamically Clear my selection Which string would match the following regular expression exactly: (ab)* o abba abab abcd ba Clear my selectionarrow_forward
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





