
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
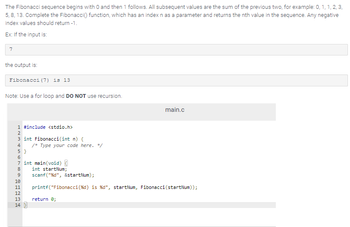
Transcribed Image Text:The Fibonacci sequence begins with O and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3,
5, 8, 13. Complete the Fibonacci() function, which has an index n as a parameter and returns the nth value in the sequence. Any negative
index values should return -1.
Ex: If the input is:
7
the output is:
Fibonacci (7) is 13
Note: Use a for loop and DO NOT use recursion.
1 #include <stdio.h>
NM in N
2
3 int Fibonacci(int n) {
4 /* Type your code here. */
5}
6
7 int main(void) {
8
int startNum;
9
scanf("%d", &startNum);
main.c
10
11 printf("Fibonacci (%d) is %d", startNum, Fibonacci (startNum));
return 0;
12
13
14
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 5 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Write a program that generates random numbers between -25 and 25 by using the randint function. The program will add up the numbers and terminate when the sum of the values becomes zero. The program should contain the following functions: add() : add up the values main(): the function where the program execution should begin and end. randomgen(): a function that returns a number between -25 and 25 A global variable subsetsum that keeps track of the sum The program should output the count of the number of values generated before exiting saying that the subset sum was zero.arrow_forwardC++arrow_forwardDefine function print_popcorn_time() with parameter bag_ounces. If bag_ounces is less than 3, print "Too small". If greater than 10, print "Too large". Otherwise, compute and print 6 * bag_ounces followed by "seconds". End with a newline. Remember that print() automatically adds a newline. Sample output with input: 7 42 secondsarrow_forward
- Code in Python Write a function, print_perfect_cubes(n), that takes an integer parameter n and prints the perfect cubes starting from 03 = 0 and ending with n3. When n is negative, the function prints nothing; but do not check for this condition with an "if" statement, it is unneccesary; use a for loop that will automatically print nothing when n < 0. Hint for choosing the right range for your for loop: In the general case, when n is not negative, your function will need to print n+1 different values. For example: Test Result print_perfect_cubes(2) 0 1 8 print_perfect_cubes(5) 0 1 8 27 64 125 print_perfect_cubes(-10)arrow_forwardC++arrow_forwardCompute and Plot the ROC Curve Write a function from scratch called roc_curve_computer that accepts (in this exact order): a list of true labels a list of prediction probabilities (notice these are probabilities and not predictions - you will need to obtain the predictions from these probabilities) a list of threshold values. The function must compute and return the True Positive Rate (TPR, also called recall) and the False Positive Rate (FPR) for each threshold value in the threshold value list that is passed to the function. Important: Be sure to reuse functions and code segments from your work above! You should reuse two of your above created functions so that you do not duplicate your code. The function you will write behaves identically to Scikit-Learn's roc_curve function, except that it will take the list of thresholds in as input rather than return them as output. Your function must calculate one value of TPR and one value of FPR for each of the threshold values in the list.…arrow_forward
- Up for the count def counting_series (n): The Champernowme word 1234567891011121314151617181920212223., also known as the counting series, is an infinitely long string of digits made up of all positive integers written out in ascending order without any separators. This function should return the digit at position n of the Champernowne word. Position counting again starts from zero for us budding computer scientists. Of course, the automated tester will throw at your function values of n huge enough that those who construct the Champernowne word as an explicit string will run out of both time and space long before receiving the answer. Instead, note how the fractal structure of this infinite sequence starts with 9 single-digit numbers, followed by 90 two-digit numbers, followed by 900 three-digit numbers, and so on. This observation gifts you a pair of seven league boots that allow their wearer skip prefixes of this series in exponential leaps and bounds, instead of having to crawl…arrow_forwardThe following requirments that weren't mentioned for solving the following Python Code below: The provided code for alphabet, test_dups, test_miss, and histogram. Your implementation of the has_duplicates function. A loop that outputs duplicate information for each string in test_dups. Your implementation of the missing_letters function. A loop that outputs missing letters for each string in test_miss. Write a function called missing_letters that takes a string parameter and returns a new string with all the letters of the alphabet that are not in the argument string. The letters in the returned string should be in alphabetical order. Your implementation should use a histogram from the histogram function. It should also use the global variable alphabet. It should use this global variable directly, not through an argument or a local copy. It should loop over the letters in alphabet to determine which are missing from the input parameter. The function missing_letters should…arrow_forwardPlease follow all the steps givenarrow_forward
- Complete the rotate_text() function that takes 2 parameters, a string data and an integer n. If n is positive, then the function will shift all the characters in data forward by n positions, with characters at the end of the string being moved to the start of the string. If n is 0 then the text remains the same. For example: rotate_text('abcde', rotate_text('abcde', rotate_text('abcde', 1) would return the string 'eabcd' 3) would return the string 'cdeab' 5) would return the string 'abcde' rotate_text('abcde', 6) would return the string 'eabcd' ... and so on. If n is negative, then the function will shift the characters in data backward by n positions, with characters at the start of the string being moved to the end of the string. For example: rotate text('abcde', -1) would return the string 'bcdea'arrow_forwardpost in python please and a coding editor too You are asked to help write a program that will help users purchase cookies. A user will input types of cookies and the number of cookies that they want, and your program will suggest how many boxes that they should order. There are 30 cookies per box, so your goal is to make sure that the user will buy enough boxes so that they will get the cookies that they want. Write a function cookie_order that takes a dictionary as a parameter containing cookie names as keys and numbers of those cookies as values. Have this function return a new dictionary that has cookie names and the number of boxes that should be purchased of each type. Hint: This means if someone wants 31 cookies, they need to buy 2 boxes of cookies of that type. You may want to consider using math.ceil for this problem. Examples: >>> cookie_order({'thin mints': 97}) {'thin mints': 4} >>> cookie_order({'thin mints':34, 'shortbread': 60, 'caramel delites': 71,…arrow_forwardIn this problem, you have available to you a working version of the function round_up described in part (a). It is located in a module named foo. Using the given round_up function, write a function round_up_all that takes a list of integers and MODIFIES the list so that each number is replaced by the result of calling round_up_ on that number. For example, if you run the code, 1st = [43, 137, 99, 501, 300, 275] round_up_all(1st) print(1st) the list would contain the values [100, 200, 100, 600, 300, 300] Do not re-implement the round_up function, just import the food module and use it. Here is the code for the round_up function that can be imported using foo: def round_up(num): if num % 100 == 0 : #if number is complete divisible return num #return orginal num else: return num + (100-(num % 100)) #else add 100-remainder to num, if __name__ == '__main__': print(round_up(234)) print(round_up(465)) print(round_up(400)) print(round_up(89))arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education