
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
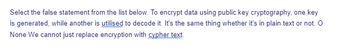
Transcribed Image Text:Select the false statement from the list below. To encrypt data using public key cryptography, one key
is generated, while another is utilised to decode it. It's the same thing whether it's in plain text or not. O
None We cannot just replace encryption with cypher text.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Talk about the benefits as well as the drawbacks of utilizing symmetric encryption. How exactly does one go about picking a cryptographic method that is most suitable?arrow_forward3. Encipher the message 'cryptography’ using a Shift Cipher with k = 10. Show your work.arrow_forwardLet's say you generated RSA keys and you chose p=59, q=43, and the smallest encryption exponent that qualifies for this p and q. (You will have to follow the key generation algorithm to fill in the details.) If someone gives you 99 as the ciphertext they created using your public key, what is the plaintext you get when you use your private key to decrypt? What is e?____ What is d?____ What is the decrypted value?____arrow_forward
- What is the difference between a block cipher and a stream cipher? What is the difference between an unconditionally secure cipher and a computationally secure cipher? What is the difference between a monoalphabetic cipher and a polyalphabetic cipher? Why is it important to study Feistel ciphers?arrow_forwardDescribe the terms “plaintext,” “ciphertext,” and “secret key” as they apply to symmetric encryption Cryptographic systems are characterized along three independent dimensions. What are these three dimensions? The term “strong encryption” refers to encryption schemes that make it impractical for unauthorized persons to gain access to plaintext that has been encrypted. What properties are characteristic of a strong encryption algorithm?arrow_forwardDon't need code.arrow_forward
- Encrypt the message "do not attack" using the affine cipher with key = (17,14). Ignore the space between the words. Decrypt the message to get the original plaintextarrow_forwardLet's pretend a Vigen'ere cipher was used to encrypt a long string of text, and that the encrypted text included many instances of the same string. Describe the methods you'll use to calculate the length of the key based on this information.arrow_forwardPublic key cryptography faced the challenge of distributing keys in the beginning. To easily show how key distribution may be carried out, why not use an example?arrow_forward
- One of the most basic problems that public key cryptography set out to solve was the problem of key distribution.Could you give us an overview in a nutshell?arrow_forwardPerform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".arrow_forwardLet k be the encipherment key for a Caesar cipher. The decipherment key is 26 – k.One of the characteristics of a public key cryptosystem is that the encipherment anddecipherment keys are different. Explain why the Caesar cipher is a secret keycryptosystem, not a public key cryptosystem?arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education