
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
Proper zone security is critical for SCADA Systems. Given the network diagram below, design a security architecture to protect the different zones of your control system.
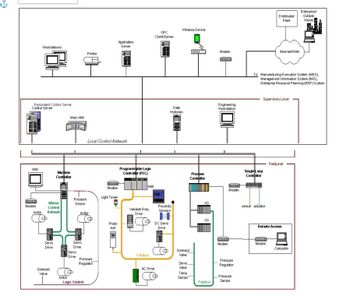
Transcribed Image Text:دم
Redundant Control Server
Control Server
HMI
Workstations
100001
Modem
Motion
Control
motor Network
Servo
Drive
Solenoid
Valve
Machine
Controller
Main HMI
motor
Pressure
Sensor
Servo
Drive
Servo
Drive
Printer
motor
Logic Control
Local Control Network
Pressure
Regulator
Application
Server
TRAVE
Modem
Light Tower
Photo
eye
192
Tha
Programmable Logic
Controller (PLC)
HMI
Variable Freq
Drive
Fieldbus
OPC
Client/Server
AC Drive
DC Servo
Drive
Proximity
Sensors
H
Wireless Device
Data
Historian
Solenoid
Valve
Servo
Valve
Temp
Sensor
Basa
Process
Controller
1/0
1/10
Fieldbus
Modem
Legea
Engineering
Workstation
FOOOD
Modem
COOL
Modern
Pressure
Regulator
Pressure
Sensor
Single Loop
Controller
Distributed
Plant
Supervisory Level
sensor actuator
Internet/WAN
To: Manufacturing Execution System (MES),
Management Information System (MIS),
Enterprise Resource Planning (ERP) System
na
Modem
FieldLevel
Remote Access
Enterprise/
Outside
World
Computer
UPPLET
**
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps

Knowledge Booster
Similar questions
- The difference between an application-based firewall and a network-based firewall must be understood.arrow_forwardAuditing and log gathering are two aspects of cybersecurity that are very important to network security. It is important to illustrate the meaning of the phrases by providing both examples and descriptions of their use in a professional setting.arrow_forwardExplain what a "firewall" is and how it works in the context of protecting a network, then go through some of the ways it may be implemented in different kinds of network architectures.arrow_forward
- Explain the principles of Zero Trust Network Architecture (ZTNA) and how it transforms network security by assuming that threats exist both inside and outside the network.arrow_forwardAxl & 21 Bxl Figure 3 (e) The circuit in figure 3shows a special relationship, state in what other way this logic circuit could be written using Boolean algebra. For each of the following Boolean expressions, state whether they are in sum-of-products (SoP) form. (f) AD(B C) +AD (g) ABC + ABC (h) (A + C)(B + D)(B+ C)(A+ D + E) (i) ABD + BCarrow_forwardMechanisms of a more complex kind for protecting information that are included in the OSI security architecture?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY