
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
Hi,
can i get help with all parts of this question.
thanks
Transcribed Image Text:-nshot
Error Rates
FRR
1
0.9
0.8
0.7
0.6
0.5
0.4
0.3
0.2
0.1
0
1
0.9
0.8
0.7
0.6
0.5
0.4
0.3
0.2
0.1
0
0
0
FRR
0.1
0.1
·
0.2
System performance
0.2
0.3
0.4
0.6
Operating Threshold
0.3
(a)
System Performance (DET Curve)
0.4
0.5
0.5
FAR
(b)
Figure 2
0.7
0.6
0.7
0.8
0.8
FAR
•
0.9
0.9
1
1
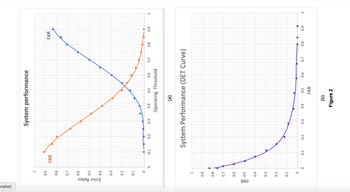
![2. You are evaluating a biometric system for potential use in a security application.
Experimental measurements of False Rejection Rate (FRR) and False Acceptance
Rate (FAR) values have been estimated at different threshold settings and are
presented in two different plots as shown in Figure 2.
(a) Determine the Equal Error Rate (EER) of the system from each of the plots
separately. [You need to annotate how you derived the value(s).]
(b) The security application needs an FAR not greater than 15% and an FRR less
than 25%. Would you recommend procuring this system for the application? Explain
briefly. [You need to carry out this analysis using Figure 2(a) and Figure 2(b)
independently. You need to explain/annotate how the decision is reached.]](https://content.bartleby.com/qna-images/question/78f0ee4d-c883-4e97-b05f-6fd93d8f479a/7dc58289-87cb-4bff-965e-b717c39f1f14/8gtt7nr_thumbnail.png)
Transcribed Image Text:2. You are evaluating a biometric system for potential use in a security application.
Experimental measurements of False Rejection Rate (FRR) and False Acceptance
Rate (FAR) values have been estimated at different threshold settings and are
presented in two different plots as shown in Figure 2.
(a) Determine the Equal Error Rate (EER) of the system from each of the plots
separately. [You need to annotate how you derived the value(s).]
(b) The security application needs an FAR not greater than 15% and an FRR less
than 25%. Would you recommend procuring this system for the application? Explain
briefly. [You need to carry out this analysis using Figure 2(a) and Figure 2(b)
independently. You need to explain/annotate how the decision is reached.]
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Similar questions
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY