
Microsoft Visual C#
7th Edition
ISBN: 9781337102100
Author: Joyce, Farrell.
Publisher: Cengage Learning,
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
How do I write the while loop using a sentinel value to control the loop, and also write the statements that make up the body of the loop? Also including the calculations to compute the average rating.
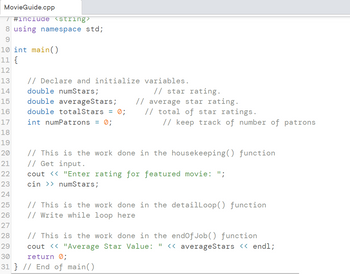
Transcribed Image Text:MovieGuide.cpp
/ #include <string>
8 using namespace std;
9
10 int main()
11 {
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
// Declare and initialize variables.
double numStars;
// star rating.
double averageStars; // average star rating.
double totalStars = 0;
int numPatrons = 0;
// total of star ratings.
// keep track of number of patrons
// This is the work done in the housekeeping() function
// Get input.
cout << "Enter rating for featured movie: ";
cin >> numStars;
// This is the work done in the detailLoop() function
// Write while loop here
28
29
30
31 } // End of main()
// This is the work done in the endOfJob() function
cout << "Average Star Value: " << averageStars << endl;
return 0;
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 5 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- (Numerical) Write and test a function that returns the position of the largest and smallest values in an array of double-precision numbers.arrow_forward(Statistics) Write a program that includes two functions named calcavg() and variance(). The calcavg() function should calculate and return the average of values stored in an array named testvals. The array should be declared in main() and include the values 89, 95, 72, 83, 99, 54, 86, 75, 92, 73, 79, 75, 82, and 73. The variance() function should calculate and return the variance of the data. The variance is obtained by subtracting the average from each value in testvals, squaring the values obtained, adding them, and dividing by the number of elements in testvals. The values returned from calcavg() and variance() should be displayed by using cout statements in main().arrow_forward(Electrical eng.) Write a program that specifies three one-dimensional arrays named current, resistance, and volts. Each array should be capable of holding 10 elements. Using a for loop, input values for the current and resistance arrays. The entries in the volts array should be the product of the corresponding values in the current and resistance arrays (sovolts[i]=current[i]resistance[i]). After all the data has been entered, display the following output, with the appropriate value under each column heading: CurrentResistance Voltsarrow_forward
- (Data processing) Your professor has asked you to write a C++ program that determines grades at the end of the semester. For each student, identified by an integer number between 1 and 60, four exam grades must be kept, and two final grade averages must be computed. The first grade average is simply the average of all four grades. The second grade average is computed by weighting the four grades as follows: The first grade gets a weight of 0.2, the second grade gets a weight of 0.3, the third grade gets a weight of 0.3, and the fourth grade gets a weight of 0.2. That is, the final grade is computed as follows: 0.2grade1+0.3grade2+0.3grade3+0.2grade4 Using this information, construct a 60-by-7 two-dimensional array, in which the first column is used for the student number, the next four columns for the grades, and the last two columns for the computed final grades. The program’s output should be a display of the data in the completed array. For testing purposes, the professor has provided the following data:arrow_forwardA structure that allows repeated execution of a block of statements is a(n) _____________. sequence selection array looparrow_forward(Data processing) A bank’s customer records are to be stored in a file and read into a set of arrays so that a customer’s record can be accessed randomly by account number. Create the file by entering five customer records, with each record consisting of an integer account number (starting with account number 1000), a first name (maximum of 10 characters), a last name (maximum of 15 characters), and a double-precision number for the account balance. After the file is created, write a C++ program that requests a user-input account number and displays the corresponding name and account balance from the file.arrow_forward
- (Conversion) Write a C++ program that converts gallons to liters. The program should display gallons from 10 to 20 in 1-gallon increments and the corresponding liter equivalents. Use the relationship that 1gallon=3.785liters.arrow_forward(Data processing) Construct a three-dimensional weather array for a two-week time period. Include this array in a C++ program that displays the temperatures correctly in response to any of the following user requests: • Any day’s high and low temperatures • Average high and low temperatures for a given month • Month and day with the highest temperature • Month and day with the lowest temperaturearrow_forward(Electrical eng.) a. An engineer has constructed a two-dimensional array of real numbers with three rows and five columns. This array currently contains test voltages of an amplifier. Write a C++ program that interactively inputs 15 array values, and then determines the total number of voltages in these ranges: less than 60, greater than or equal to 60 and less than 70, greater than or equal to 70 and less than 80, greater than or equal to 80 and less than 90, and greater than or equal to 90. b. Entering 15 voltages each time the program written for Exercise 7a runs is cumbersome. What method could be used for initializing the array during the testing phase? c. How might the program you wrote for Exercise 7a be modified to include the case of no voltage being present? That is, what voltage could be used to indicate an invalid voltage, and how would your program have to be modified to exclude counting such a voltage?arrow_forward
- (Civil eng.) Write an assignment statement to determine the maximum bending moment, M, of a beam, given this formula: M=XW(LX)L X is the distance from the end of the beam that a weight, W, is placed. L is the length of the beam.arrow_forward(Civil eng.) Write a C++ program to calculate and display the maximum bending moment, M, of a beam that’s supported on both ends (see Figure 3.8). The formula is M=XW(LX)/L, where X is the distance from the end of the beam that a weight, W, is placed, and L is the beam’s length. You program should produce this display: The maximum bending moment is xxxx.xxxx The xxxx.xxxx denotes placing the calculated value in a field wide enough for four places to the right and left of the decimal point. For your program, assign the values1.2,1.3,and11.2toX,W,andL.arrow_forward(Numerical) Write an assignment statement to calculate the nth term in an arithmetic sequence. This is the formula for calculating the value, v, of the nth term: v=a+(n1)d a is the first number in the sequence. d is the difference between any two numbers in the sequence.arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning,
Microsoft Visual C#Computer ScienceISBN:9781337102100Author:Joyce, Farrell.Publisher:Cengage Learning, C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage
C++ for Engineers and ScientistsComputer ScienceISBN:9781133187844Author:Bronson, Gary J.Publisher:Course Technology PtrProgramming Logic & Design ComprehensiveComputer ScienceISBN:9781337669405Author:FARRELLPublisher:Cengage C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning
C++ Programming: From Problem Analysis to Program...Computer ScienceISBN:9781337102087Author:D. S. MalikPublisher:Cengage Learning EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT
EBK JAVA PROGRAMMINGComputer ScienceISBN:9781337671385Author:FARRELLPublisher:CENGAGE LEARNING - CONSIGNMENT Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning
Systems ArchitectureComputer ScienceISBN:9781305080195Author:Stephen D. BurdPublisher:Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:9781337102100
Author:Joyce, Farrell.
Publisher:Cengage Learning,

C++ for Engineers and Scientists
Computer Science
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Course Technology Ptr

Programming Logic & Design Comprehensive
Computer Science
ISBN:9781337669405
Author:FARRELL
Publisher:Cengage

C++ Programming: From Problem Analysis to Program...
Computer Science
ISBN:9781337102087
Author:D. S. Malik
Publisher:Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:9781337671385
Author:FARRELL
Publisher:CENGAGE LEARNING - CONSIGNMENT

Systems Architecture
Computer Science
ISBN:9781305080195
Author:Stephen D. Burd
Publisher:Cengage Learning