
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
thumb_up100%
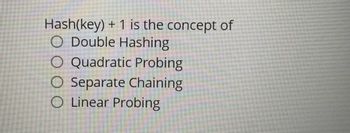
Transcribed Image Text:Hash(key) + 1 is the concept of
O Double Hashing
O Quadratic Probing
O Separate Chaining
O Linear Probing
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Similar questions
- Linear hash index:Consider the Extendible Hashing index shown in figure below.A bucket is split each time an overflow page gets created Show the state of the index after each operation:a) Insertion of entry 2b) Insertion of entry 40c) Insertion of entry 39arrow_forwardHow can hashing be used to determine if all elements in a list are unique? What is the complexity?arrow_forwardA hash-map has been constructed with quadratic-hashing. The hashing function is h(k;) = (3 * k; + 7) mod 17 and the table length is N = 17. How many cells will be probed by the call of insert(2) 1 4 5 6 7 8 10 11 12 13 14 15 16 26 89 11 35 70 59 Note: First row contains the indices and the second row contains the items.arrow_forward
- How can hashing be used to determine if all elements in a list are unique? What is the complexity?arrow_forwardTask - 1: Write a java program to implement the following algorithms for Open Addressing techniques for Hash Table data structure. (Use a simple array of integers to store integer key values only). HASH-SEARCH(T, k) HASH-INSERT (T, k) i = 0 repeat j = h (k, i) if T[j] == NIL T[j] = k return j else i = i + 1 ● i = 0 repeat until i == m error “hash table overflow" For both algorithms, to compute the index j, write the following methods: getLinear ProbIndex (key, i) getQuadraticProbIndex ● get DoubleHash (key, i) (key, i) j = h (k, i) if T[j] == k return j i = i + 1 until T[j] == NIL or i = m return NIL Linear Probing index is computed using following hash function: h(k, i) = (h₁(k) + i) mod m h₁(k)= k mod m Quadratic probing index is computed using following hash function: h(k, i) = (h₁(k) + i²) mod m h₁(k)= k mod m Double hashing index is computed using following hash function: h(k, i) = (h₁(k) + i h₂(k)) mod m h₁(k)= k mod m h₂(k) = 1 + (k mod m - 1)arrow_forwardImplement a commonly used hash table in a program that handles collision using linear probing. Using (K mod 13) as the hash function, store the following elements in the table: {1, 5, 21, 26, 39, 14, 15, 16, 17, 18, 19, 20, 111, 145, 146}.arrow_forward
- Hashing table Sıze 7: SIze 7: 12,5,19,2,23. Use Quadratic Probing if tnere is Answer in form of the order of a collision in ferted elemunts. a) -19.2 23 12-5 b).-19223 125 C) 12 2 23 19--S ) 12--2 2319 5arrow_forwardWhat is the time complexity of delete function in the hash table using a doubly linked list?a) O(1)b) O(n)c) O(log n)d) O(n log n)arrow_forwardThe Big O value of hashing is: O a. O(log N) O b. O(N) Oc O(N*Log N) O d. 0(1)arrow_forward
- 5. Here are keys and their hash values, for hashing using h(k)= k mod m Where m = 13 130 108 K H(K) 9 0 4 Use double hashing to resolve the collision with h2(k)= 10 - (k mod 10) Construct the hash table 100 78 0 35 9arrow_forward2. Consider the Linear Hashing index. Linear Hashing | h1 000 001 010 011 ho ठ 00 01 10 11 Mod 8 (%68) Mod 4 (%4) 16* 21* 40* 37* 14* 18* 6* Primary Page 13* A. Show the resulting index after inserting the entry 9* C. Show the resulting index after inserting entry 7* 31* 19* 11* 23* B. Show the resulting index after inserting the entry 3* 30* D. Show the resulting index after inserting the entry 22* Overflow Pagearrow_forwarddo botharrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY