
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
![You are evaluating a biometric system for potential use in a security application.
Experimental measurements of False Rejection Rate (FRR) and False Acceptance
Rate (FAR) values have been estimated at different threshold settings and are
presented in two different plots as shown in Figure 2.
(a) Determine the Equal Error Rate (EER) of the system from each of the plots
separately. [You need to annotate how you derived the value(s).]
(b) The security application needs an FAR not greater than 15% and an FRR less
than 25%. Would you recommend procuring this system for the application? Explain
briefly. [You need to carry out this analysis using Figure 2(a) and Figure 2(b)
independently. You need to explain/annotate how the decision is reached.]](https://content.bartleby.com/qna-images/question/453e2dee-5bad-4d2e-a71f-6b8eeb7e8b02/06df63c8-e7e9-4bab-b318-b9c62324af41/by7ijul_thumbnail.png)
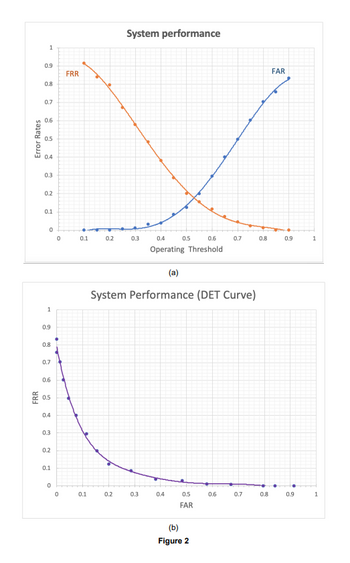
Transcribed Image Text:You are evaluating a biometric system for potential use in a security application.
Experimental measurements of False Rejection Rate (FRR) and False Acceptance
Rate (FAR) values have been estimated at different threshold settings and are
presented in two different plots as shown in Figure 2.
(a) Determine the Equal Error Rate (EER) of the system from each of the plots
separately. [You need to annotate how you derived the value(s).]
(b) The security application needs an FAR not greater than 15% and an FRR less
than 25%. Would you recommend procuring this system for the application? Explain
briefly. [You need to carry out this analysis using Figure 2(a) and Figure 2(b)
independently. You need to explain/annotate how the decision is reached.]
Transcribed Image Text:Error Rates
FRR
1
0.9
0.8
0.7
0.6
0.5
0.4
0.3
0.2
0.1
0
1
0.9
0.8
0.7
0.6
0.5
0.4
0.3
0.2
0.1
0
0
0
FRR
0.1
0.1
0.2
System performance
0.2
0.3
0.4
0.6
Operating Threshold
0.3
0.5
(a)
System Performance (DET Curve)
0.4
0.5
FAR
(b)
Figure 2
0.7
0.6
0.7
0.8
0.8
FAR
0.9
0.9
1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps with 1 images

Knowledge Booster
Similar questions
- Consider the following table that contains the IDs of 12 participants and their crash- avoidance reaction times (in milliseconds) on four tests. Two tests were done during the day in daylight and two tests were done at night with reduced lighting. Crash-avoidance Reaction Time (ms) Night Test 3 Participant Day ID Test 2 Test 1 Test 4 9001 887 838 765 648 9002 680 491 953 767 9003 662 553 985 696 9004 789 526 581 770 9005 508 451 688 714 9006 566 633 856 642 9007 656 747 846 718 9008 776 491 944 604 9009 770 672 814 617 9010 333 432 591 602 9011 730 593 796 700 9012 496 404 846 892 This question has multiple parts. Create output to MATLAB's command window exactly as shown, except replacing xxxx with actual values, as instructed. You may use the disp command, but not the fprintf command If you have difficulty with the alignment or formatting of numeric output, add the command format shortg near the top of your solution. In your solution, put the following MATLAB statements at the…arrow_forwardInvestigate to discover if there is an attempt being made to break into the system. Is there a problem with the data's security?arrow_forwardDemonstrate how native authentication and authorization services are performed on the web server in response to a request from a web client for a secure server resource. Include the particulars of each step of the process. What are some of the reasons why, in your opinion, the implementation of layered protocols is such an appealing strategy? Are there any particular instances that you might use to back up the assertions you've made?arrow_forward
- Consider the following table that contains the IDs of 12 participants and their crash- avoidance reaction times (in milliseconds) on four tests. Two tests were done during the day in daylight and two tests were done at night with reduced lighting. Crash-avoidance Reaction Time (ms) Participant Day Night ID Test 1 Test 2 Test 3 Test 4 9001 887 838 765 648 9002 680 491 953 767 9003 662 553 985 696 9004 789 526 581 770 9005 508 451 688 714 9006 566 633 856 642 9007 656 747 846 718 9008 776 491 944 604 9009 770 672 814 617 9010 333 432 591 602 9011 730 593 796 700 9012 496 404 846 892 rt.xisx in the This question has multiple parts. Create output to MATLAB's command window exactly as shown, except replacing xxxx with actual values, as instructed. You may use the disp command, but not the fprintf command If you have difficulty with the alignment or formatting of numeric output, add the command format shortg near the top of your solution. In your solution, put the following MATLAB statements…arrow_forwardDiscuss the concept of "wait-die" and "wound-wait" schemes in deadlock prevention. Under what circumstances are each of these schemes most effective?arrow_forwardExplain two reasons of why do you think single sign-on is beneficial.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY