e one or two lines of Matlab code that s
Q: Note: The notation from this problem is from Understanding Cryptography by Paar and Pelzl. Suppose y...
A: Answer seed (S5,S4,S3,S2,S1,S0) = (1,0,0,1,1,0) tap bits (P5,P4,P3,P2,P1,P0) = (0,1,1,1,1,1) Prese...
Q: Write a code in AVR to load values $30, $15 and $40 using register R16 into locations $101, $102 and...
A: LDI R16, $30 ; Initialize the value. Load the value $30 in the registerR16. LDI R17, $15 ; Initiali...
Q: Monitor is a concurrency technique. Is it generally software, hardware, or firmware, or none of the ...
A: An computer monitor is a display device that displays information on a computer. The computer monito...
Q: Develop a class and two subclasses that inherit properties from the super class and demonstrate crea...
A: Superclass: Book Attributes of Book class: title, publisher, yearPublished and priceMethods: getter ...
Q: ber and Acknowledgement nu
A: given - What is the importance of sequence number and Acknowledgement number
Q: Mr Monkey is standing in front of a row of banana trees on Skull Island which actually belong to his...
A: The problem is similar to 0-1 knapsack problem where the total weight resembles the total distance L...
Q: Help with java hw, create a program with external sort. I have an input text of 1million ints. Im su...
A: External sorting refers to a group of sorting algorithms capable of handling large volumes of data. ...
Q: Select an app from any of the industries below and try to find out the answers to the following ques...
A: Industry: Travel OLA App Ola is India's leading ride hailing service, with over 3 million vehicles o...
Q: Note: The notation from this problem is from Understanding Cryptography by Paar and Pelzl. We conduc...
A: Answer it cycles through all possible 2m − 1 states within the shift register except the state whe...
Q: What is a chipset, and how does it work?
A: Introduction: The chipset, also known as a "Data Flow Management System," is a group of electrical c...
Q: Write a program to perform non-preemptive SJF scheduling. Consider four processes. The digits of you...
A: Actually, program is an executable software that runs on a computer.
Q: Assignment 2: COVID-19 Data Wrangling Name: The purpose of this assignment is to hone your data wran...
A: Note: Code run successfully as above problem describe. I have provided source and output screenshot ...
Q: John von Neumann was married for how long?
A: On New Year's Day in 1930, von Neumann married Marietta Kovesi, who had studied economics at Budapes...
Q: FPGA is an integrated circuit which is designed to be configured by the end users after being manufa...
A: Lets understand the meaning of field programmable. Any electronic device whose firmware, such as ROM...
Q: Give one scenario when you prefer to use memory sharing as a means of IPC. Explain why? How can you ...
A: Answer: I have given answered in the handwritten format in brief explanation
Q: Sample Input 1: 12345 Sample Output 1: No
A: Program Explanation: Create a header file. Create a function inside the main and take the input of ...
Q: Consider a two-link network where Host A is connected to the router by a 1 Mbps link with 10 ms prop...
A: Transmission delay depends upon data amount to be transmitted and the rate of transmission. Size of...
Q: Use the substitution method to show that T(n) = 8T(n/2) + n² is N(n³) Use the substitution method to...
A: Here, first we will solve given recurrence relation using substitution method. And then we will show...
Q: A CPC offset printing machine is what it sounds like.
A: Introduction: The counter pressure casting method has been refined into Counter Pressure Casting (CP...
Q: In computing, what exactly is a mobo?
A: Introduction: Computer Components: Different computer parts might have their roles inside a more ex...
Q: 3. The following processes are being scheduled using a pre-emptive SJF scheduling algorithm. Process...
A: Gantt chart, total execution time, average waiting time, and average turnaround time for the given p...
Q: 12. Write a code in AVR to load values $30, $15 and $40 using register R16 into locations $101, $102...
A: The avr is an given below :
Q: Topic: Cryptographic Active Attack Kindly discuss the Modification of Messages in simple terms.
A: Here in this question we have asked to discuss the modification of message attack in cryptography.
Q: how to check first 2 character in string are capital letter? sql
A: how to check first 2 character in string are capital letter? sql
Q: Create a flowchart in which the program gets a number from user and checks if it's a multiple of 3....
A: NOTE: AS per Bartleby guideline, if there are multiple questions available then we are allowed to so...
Q: Given a graph with 14 edges. What is the missing value 'k' in the following degree sequence, 1, 2, 3...
A: Given The answer is given below.
Q: In python, What are function, how do they work, how do you define them and call them. What is tracin...
A: Function and how it works: is a block of code defined under specific name(which can used to call tha...
Q: Create a 7-segment program that will count up from 0-9 and whenever it reaches 9 it will blink for 2...
A: Lets see the solution in the next steps
Q: MIPS
A: Introduction: Computer Processing: If you've ever had to deal with a slow-moving computer, you know ...
Q: You are a manager of a restaurant and have observed that customers in the restaurant. What is the av...
A: given - You are a manager of a restaurant and have observed that on average 36 customers per hour ar...
Q: Design two trading algorithms (agents) that have the ability to monitor the stocks through the obser...
A: Lets see the solution in the next steps
Q: Is a monochrome printer able to produce colour?
A: THE ABOVE QUESTION THAT IS MONO CHROME PRINTER THAT ABLE TO PRODUCE COLOUR IS ANSWERED BELOW
Q: What multicast address does EIGRP used
A: Introduction: Enhanced Interior Gateway Routing Protocol (EIGRP) What multicast address does EIGRP ...
Q: Given a graph with 14 edges. What is the missing value 'k' in the following degree sequence, 1, 2, 3...
A: Dear learner, hope you are doing well , I will try my best to answer this question. Thank You!!
Q: By diagnosing the motherboard problem in terms of battery, if someone has set a supervisor password ...
A: It can be frustrating when a PC doesn’t boot properly. Whether you’re putting a build together or yo...
Q: Use case diagrams can be help the tester start testing activities early. Explain how to apply Graph ...
A: Use case diagrams can be help the tester start testing activities early. Explain how to apply Graph ...
Q: Problem 2 String Generator Write a Python generator that yields all possible strings formed by using...
A: def string_generator(s): a = sorted(s) n = len(a) - 1 while True: yield ''.join(a) ...
Q: Design a 8-bit multiplier using NaiveD&Cmult algorithm with basic building blocks of 1-bit multiplie...
A: Solution The Divide and Conquer algorithm is used in the Karatsuba algorithm for rapid multiplicatio...
Q: The following table lists the freezing and boiling points of several substances. Substance Freezi...
A: Given The answer is given below.
Q: Write menu driven program to find Euler’s Runge kutta 2nd order and Runge Kutta 4th order.
A: The following are the differences between Runge-Kutta 2nd degree and Runge-Kutta 4th order: Heun's s...
Q: public class Tesla //add to signature here { Please use consistent spacing or your answer may be mar...
A: we just add the implements Comparable<T> here.
Q: Write an interface as follows: The interface is named ServiceReminder It has one method named timeF...
A: By default interface contains abstract methods. This means that the body of method is not provided a...
Q: Show that for any CFG in Chomsky Normal Form a derivation for any string (of at least length 1) requ...
A: A context-free grammar is in Chomsky normal form if every rule is of the form A → BCA → a where a is...
Q: What other protocol exchanges do you think might use both symmetric and asymmetric cryptography like...
A: Describe SSL/TLS protocol used in cryptography advantages of cryptography.
Q: onnecting more peripherals to a computer is made possible by the .
A: CPU is the brain of the system.
Q: 13. Write a code in AVR to load the value $15 into location $67 and add it to R19 place the results ...
A: LDS R0, $15 ; Retrieve the value from location 0x15 into R0 STS $67,R0 ; Store the value of R0 ...
Q: In what university did John von Neumann attend?
A: Answer John Neumann attended ETH Zurich and Eotvos Lorand University
Q: What is the purpose of caching?
A: Caching is a method of storing a copy of data so that it may be accessed immediately rather than hav...
Q: menu will show three items and their prices that the user can pick: (a) Carbonara 100php (b) Fries 8...
A: Please find the answer below :
Q: 5. Use the priority list T1, T3, T4, T6, T2, TS, T8, T7 schedule the project below with two processo...
A:
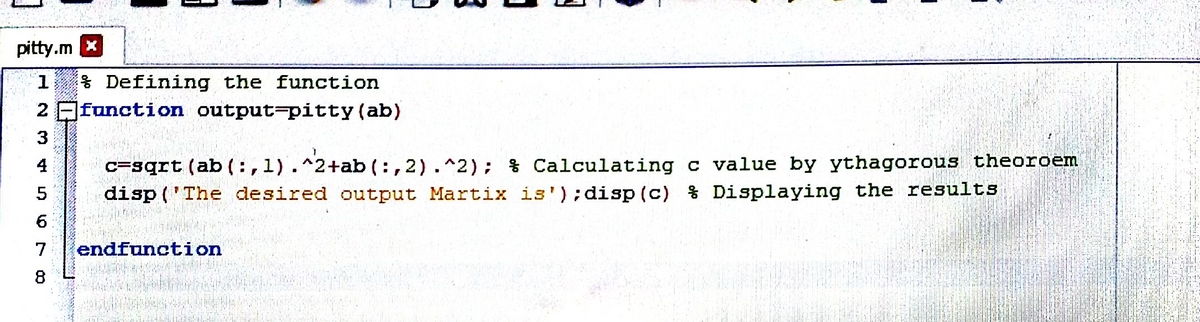
Write one or two lines of Matlab code that sums up all the values in the square-shaped submatrix consisting of rows 3 through 5 and columns 8 through 10 of the matrix A where A = peaks(10). The command window should display 3.7474 when you run it.
Trending now
This is a popular solution!
Step by step
Solved in 8 steps with 8 images

- By entering information into a number array with 8 elements from a student, find the smallest element and He was asked to draw the "viewing flow chart". The student drew the flow chart in Figure-1. This flow Find errors in the chart and show the correct representation by drawing only the relevant part of the flow chart. note: ek=smallest dizi=sequenceCreate a square matrix that has ones in the first row and first column, and whose remaining elements are the sum of two elements: the element above and the element to the left. Your program should be able to make a matrix of any size. Do this exercise using a loop (for or while) with break/continue statements as necessary.The student names and the grades for four tests for Mr. Smith’s class have been placed in parallel arrays. Mr. Smith would like to have one student’s name and test scores printed. Develop a solution that will enter the student’s name, search for the name in the same array, and then print the name and test scores. Use the sequential-search method.
- Write a code which prints out a column vector by using the row vector containing the digits in order of your student number with programming concept/method.Using the new operator, allocate a two dimensional character array. Again the number of rows and columns are going to be provided by the user as input. All of the rows are the same size. Take character strings as input fromthe user and then print the strings. Finally de-allocate the array using the delete operator.The purpose is to write a program with 2D arrays that will display Knight's Tour. Knight's Tour is a fascinating problem that is done on an electronic chessboard with a knight. Starting at any location on the chessboard, a knight proceeds to move on the board in such a manner that all positions on the chessboard are visited, once and once only. The knight may only move according to the rules of chess playing. The matrixes below show a sequence of knight moves that starts from the top-left corner. In most cases, the knight is locked in place and can go no farther. Note: there are only 3 legal knight moves from the 44 locations and they have already been visited. 01 60 39 34 31 18 09 6438 35 32 61 10 63 30 1759 02 37 40 33 28 19 0836 49 42 27 62 11 16 2943 58 03 50 41 24 07 2048 51 46 55 26 21 12 1557 44 53 04 23 14 25 0652 47 56 45 54 05 22 13 01 22 39 20 03 18 09 1600 37 02 23 08 15 04 1335 40 21 38 19 12 17 1000 00 36 41 24 07 14 0500 34 00 32 00 28 11 2600 00 00 00 42 25 06 2900…
- In a C++ program, you need to store the ID's and GPS's for 25 students. 1. Define 2 arrays that may be used in parallel to store the ID's and GPS's. 2. Write a loop to print the ID and GPA arrays in columns, with column headings. Put the information for each student on its own line.Write a program in which the user will create an array of numbers. Take note the user will be the one to decide the number of rows and columns, and will be the onė to input the elemets of the array. Let the program display the matrix. Then, the program must ask the user which one is to display-the minimum or the maximum element of the array.The purpose is to write a program with 2D arrays that will display Knight's Tour. Knight's Tour is a fascinating problem that is done on an electronic chessboard with a knight. Starting at any location on the chessboard, a knight proceeds to move on the board in such a manner that all positions on the chessboard are visited, once and once only. The knight may only move according to the rules of chess playing. The matrixes below show a sequence of knight moves that starts from the top-left corner. In most cases, the knight is locked in place and can go no farther. Note: there are only 3 legal knight moves from the 44 locations and they have already been visited. 01 60 39 34 31 18 09 6438 35 32 61 10 63 30 1759 02 37 40 33 28 19 0836 49 42 27 62 11 16 2943 58 03 50 41 24 07 2048 51 46 55 26 21 12 1557 44 53 04 23 14 25 0652 47 56 45 54 05 22 13 01 22 39 20 03 18 09 1600 37 02 23 08 15 04 1335 40 21 38 19 12 17 1000 00 36 41 24 07 14 0500 34 00 32 00 28 11 2600 00 00 00 42 25 06 2900…
- Write a program to insert an element in the given array (1D) at the beginning. After insertion, identify the largest element from the array, and delete it. After deleting the largest element, display the final array elements on the screen.In C programming language.In C language, take an Infix expression from the user and apply a check if the user has entered two operators together by mistake. If yes, delete the 2nd operator. Try to work with only one array.ou have been provided with the 4-by-4 matrix attached on the picture: Write a Java application using NetBeans that reads the above 4-by-4 matrix and displays the sum of all its elements on the major diagonal. Output is as follows:(see attached output.











