
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
You guys giving me AI answer. Don't post AI generated answer or plagiarised answer. If I see these things I'll give you multiple downvotes and will report immediately.
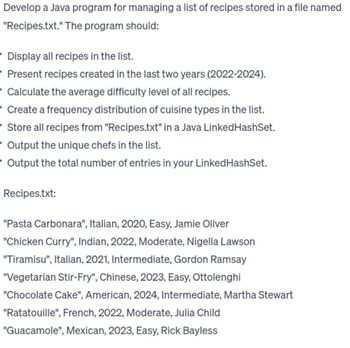
Transcribed Image Text:Develop a Java program for managing a list of recipes stored in a file named
"Recipes.txt." The program should:
• Display all recipes in the list.
Present recipes created in the last two years (2022-2024).
Calculate the average difficulty level of all recipes.
Create a frequency distribution of cuisine types in the list.
• Store all recipes from "Recipes.txt" in a Java Linked HashSet.
Output the unique chefs in the list.
- Output the total number of entries in your Linked HashSet.
Recipes.txt:
"Pasta Carbonara", Italian, 2020, Easy, Jamie Oliver
"Chicken Curry", Indian, 2022, Moderate, Nigella Lawson
"Tiramisu", Italian, 2021, Intermediate, Gordon Ramsay
"Vegetarian Stir-Fry", Chinese, 2023, Easy, Ottolenghi
"Chocolate Cake", American, 2024, Intermediate, Martha Stewart
"Ratatouille", French, 2022, Moderate, Julia Child
"Guacamole", Mexican, 2023, Easy, Rick Bayless
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 6 images

Knowledge Booster
Similar questions
- Do you believe it is feasible for you to explain why authentication is still such an issue in today's information culture? If so, please share your thoughts below.arrow_forwardAlert dont submit AI generated answer.arrow_forwardDo you believe it is feasible for you to explain why authentication is still such an issue in today's information culture? If so, please share your thoughts below.arrow_forward
- Phishing is one type of electronic con, and it can be used in combination with fraud and other methods. There may also be other ways to do it. You can also use phishing on its own. What are the best ways to stop scams like phishing and faking from happening, and how can they be done?arrow_forwardThere is a possibility that you may get emails alleging that someone has stolen your identity or compromised the information associated with your account. Consider the repercussions of your actions.arrow_forwardIs there a reason why Chat GDP would claim to have written my paper when I wrote it myself?arrow_forward
- You are going to get an email from the mail server at work informing you that your password has been changed and that you need to confirm this information. There is a strong likelihood that you haven't changed the password in a while. What caused the password to be different? Malware that was installed on the computers that successfully changed the password may have been utilized by an attacker.arrow_forwardMatch the attack vector with the identified attack (see attched photo) You can only choose one attack for each and once used you cannot re-use the attack.arrow_forwardHow would authenticating benefit our goals? We'll compare some popular authentication techniques below.arrow_forward
- What exactly does it mean when someone says they are going to assault you with a poison package, and what does it imply? Please provide two examples of this kind of violent attack.arrow_forwardDistributed denial of service attacks occur when several users attempt to overload a website at the same time. I can't see how one individual could possibly manage all of this.arrow_forwardIn order to provide an additional degree of protection to the process of making electronic payments, certain credit card companies now supply their customers with credit card numbers that can only be used once. Customers need to go to the website of the entity that issued their credit card in order to get the one-time-use number. Compared to the conventional means of using credit card numbers, what are the benefits of applying this technology instead? What are the benefits and drawbacks of using this method as opposed to authenticating yourself using an electronic payment gateway?arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY