
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
I know you guys are using AI . Don't you dare give me AI generated answer or plagiarised answer. If I see these things I'll give you multiple downvotes and will report immediately.
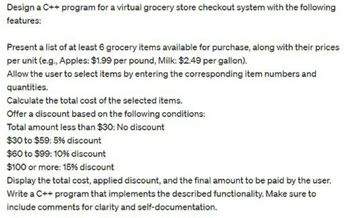
Transcribed Image Text:Design a C++ program for a virtual grocery store checkout system with the following
features:
Present a list of at least 6 grocery items available for purchase, along with their prices
per unit (e.g., Apples: $1.99 per pound, Milk: $2.49 per gallon).
Allow the user to select items by entering the corresponding item numbers and
quantities.
Calculate the total cost of the selected items.
Offer a discount based on the following conditions:
Total amount less than $30: No discount
$30 to $59: 5% discount
$60 to $99: 10% discount
$100 or more: 15% discount
Display the total cost, applied discount, and the final amount to be paid by the user.
Write a C++ program that implements the described functionality. Make sure to
include comments for clarity and self-documentation.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps with 3 images

Knowledge Booster
Similar questions
- Your employer's new security policy requires all employees to use fingerprint readers instead of login and passwords to access their computers. You cut your finger when logging in over the weekend. That's why your computer can't read your fingerprint. This causes your computer unable. What's your dream?arrow_forwardplease answerarrow_forwardThere is a possibility that you may get emails alleging that someone has stolen your identity or compromised the information associated with your account. Consider the repercussions of your actions.arrow_forward
- You are going to get an email from the mail server at work informing you that your password has been changed and that you need to confirm this information. There is a strong likelihood that you haven't changed the password in a while. What caused the password to be different? Malware that was installed on the computers that successfully changed the password may have been utilized by an attacker.arrow_forwardYou are going to get an email from the mail server at work informing you that your password has been changed and that you need to confirm this information. There is a strong likelihood that you haven't changed the password in a while. What caused the password to be different? Malware that was installed on the computers that successfully changed the password may have been utilized by an attacker.arrow_forwardWhat are the undeniable signs that you are putting yourself in danger by passively smelling, and what can you do to protect yourself from being a victim of one of these situations?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY