
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
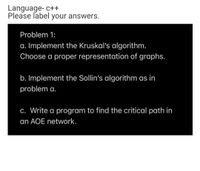
Transcribed Image Text:Language- c++
Please label your answers.
Problem 1:
a. Implement the Kruskal's algorithm.
Choose a proper representation of graphs.
b. Implement the Sollin's algorithm as in
problem a.
C. Write a program to find the critical path in
an AOE network.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps with 4 images

Knowledge Booster
Similar questions
- Pythonarrow_forwardWrite the code in python programming for the below problem. Introduction One useful data point in detecting fraud is the account history of a customer. For an account, we receive notification of purchases and, sometimes, reports of fraud. Typically, a prior report of fraud for an account would increase the perceived risk of fraud on future transactions. Similarly, a history of non-fraudulent purchases for an account would decrease the risk of fraud. A credit card holder has 90 days to report any fraudulent transactions with the card. So if an account has purchases over 90 days old and no reports of fraud, we assume that these older purchases were not-fraudulent. Problem Description The purpose of this programming problem is to determine the status of a customer account history at the time a new purchase is made. The input is a sequence of customer account events, in chronological order. Each event has three fields, all of which are of string type ,, For example:…arrow_forward*PLEASE SOLVE USING PYTHON* You are a nasa engineer who needs to monitor the situation every time a probe uses its thrusters. For a given day you are given the planned times when the thruster will be used. You need to be monitoring the situation at those boost times and for 5 minutes after. You want to figure out if you can take a break for a certain number of minutes. To achieve this you are given the planned boost times in in hours and minutes with an am/pm. And you are given a desired break time in minutes. Output if you can take the break or not given the monitoring you have to do. For example: If you know the thruster is fired at 5:00am and 12:50pm. You need to be monitoring the situation from 5:00am to 5:05am and again from 12:50pm to 12:55pm. Apart from those times you are free to take a break. So a 5 minute break is possible. But a 12 hour break is not possible.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY