
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
DO NOT COPY FROM OTHER WEBSITES
COrrect and detailed answer will be Upvoted else downvoted. Thank you!!!
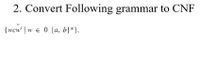
Transcribed Image Text:2. Convert Following grammar to CNF
{wcw | w e 0 {a, b}*},
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps with 1 images

Knowledge Booster
Similar questions
- Explain the basic guidelines that should be followed while making text boxes for users to enter information. Is there ever a time when disobeying these regulations would be acceptable in your opinion?arrow_forwardAs you read in Chapter 11, Facebook is one of many online companies that employ databases. In 2011, Facebook announced that it was adding a new feature—facial recognition. Photos added to a Facebook post or wall are often tagged. When a person is tagged in a photo, the person is identified and a link is created to that user’s Facebook account. To make this job easier, Facebook is using facial recognition software to identify people in the photos. Critics of this say that this is an invasion of privacy. Research the debate online. Write a short paper discussing the implications this could have on a Facebook user’s privacy. Please use these sources: https://www.pcworld.com/article/485206/facebook_on_face_recognition_sorry_we_screwed_up.html https://www.pcworld.com/article/485225/facebook_photo_tagging_a_privacy_guide.html#tk.hp_pop https://abcnews.go.com/Technology/facebook-facial-recognition-feature-raises-eyebrows/story?id=13792666arrow_forwardWhat are some of the ways that you can distinguish between reality and fiction while using the internet, in your opinion?arrow_forward
- Create a presentation containing 14 to 16 slides, including Introduction, Conclusion, and Reference slides. Include detailed speaker notes with each slide. Scenario: You are a newly hired Cyber Security Consultant for a medium-sized law firm. The U.S. based law firm will be offering legal services to the U.S. technology industry and worldwide tech markets. You are asked by the Board of Directors to explain the concept of internet governance and key privacy issues they can expect potential clients to face. They also would like to know how U.S. and EU public policy may impact potential clients in the technology market so they can make a more informed decision on how best to invest into areas of research to improve customer satisfaction and related legal services. Your task is to: Accurately define human rights issues in the "cyber domain". Identify the stances on privacy of key nations (include at a minimum the U.S. and EU). Accurately describe the influence of public policy on…arrow_forwardDO NOT COPY FROM OTHER WEBSITES Upvote guarenteed for a correct and detailed answer. Thank you!!!arrow_forwardWhich of the following information can be classified as a sensitive personal information? * Your name. Your being a fan of BTS. Your Age. Your weight.arrow_forward
- I need to expand this answer in one full page, how will I get that? Thanks.arrow_forwardIs there anything new that StuffDOT has done to improve the usability of their website?arrow_forward4 DO NOT COPY FROM OTHER WEBSITES Upvote guarenteed for a correct and detailed answer. Thank you!!!arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY