
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
Transcribed Image Text:2.
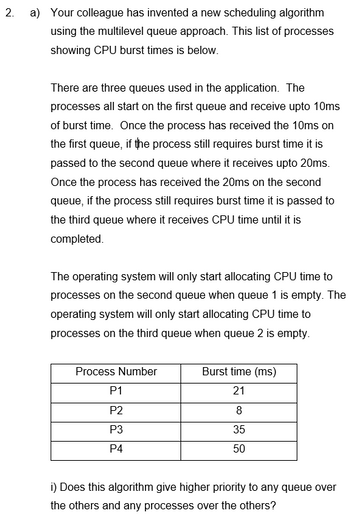
a) Your colleague has invented a new scheduling algorithm
using the multilevel queue approach. This list of processes
showing CPU burst times is below.
There are three queues used in the application. The
processes all start on the first queue and receive upto 10ms
of burst time. Once the process has received the 10ms on
the first queue, if the process still requires burst time it is
passed to the second queue where it receives upto 20ms.
Once the process has received the 20ms on the second
queue, if the process still requires burst time it is passed to
the third queue where it receives CPU time until it is
completed.
The operating system will only start allocating CPU time to
processes on the second queue when queue 1 is empty. The
operating system will only start allocating CPU time to
processes on the third queue when queue 2 is empty.
Process Number
P1
P2
P3
P4
Burst time (ms)
21
8
35
50
i) Does this algorithm give higher priority to any queue over
the others and any processes over the others?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Similar questions
- Consider a computer environment in which there are 4 magnetic drives, 2 printers, 3 scanners, and 1 optical drive. Three processes P1, P2, P3 are using these resources. At any point in time, the allocations and requests for these resources are as follows. Allocations: Magnetic drive Printer Scanner Optical drive P1 1 P2 2 1 P3 1 Requests: Magnetic drive 2 Printer Scanner Optical drive P1 1 P2 1 1 P3 2 1 Is there any way that the processes can complete without deadlock? If yes, explain how. If not, explain why not.arrow_forwardThe following program consists of 3 concurrent processes and 3 binary semaphores. The semaphores are initialized as S0 = 0,S1 = 1 and S2 = 1. Process P0:while (true) { wait (S0); print '1';release(S1);release(S2);} Process P1:wait (S2);release (S0); Process P2:wait(S2);release(S0); How many times will process P0 print '1'?arrow_forwardThe dining philosophers is one of the well-known process scheduling problems in operating systems. Explain the dining philosophers problem and the scheduling problem it represents. Write a simple a semaphore-based algorithm to solve this problem. Can using semaphores solve this problem? Justify. Suggest remedies.arrow_forward
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY