
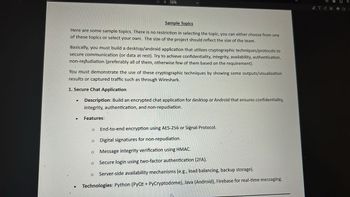
Basically, you must build a desktop/android application that utilizes cryptographic techniques/protocols to secure communication (or data at rest). Try to achieve confidentiality, integrity, availability, authentication, non-repudiation (preferably all of them, otherwise few of them based on the requirement).
You must demonstrate the use of these cryptographic techniques by showing some outputs/visualization results or captured traffic such as through Wireshark.
1. Secure Chat Application
Description: Build an encrypted chat application for desktop or Android that ensures confidentiality, integrity, authentication, and non-repudiation.
Features:
-- End-to-end encryption using AES-256 or Signal Protocol.
--Digital signatures for non-repudiation.
--Message integrity verification using HMAC.
Secure login using two-factor authentication (2FA).
--Server-side availability
Technologies: Python (PyQt + PyCryptodome), Java (Android), Firebase for real-time messaging.
Step by stepSolved in 2 steps

 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY





