
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN: 9780133594140
Author: James Kurose, Keith Ross
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Question
e^1/x
______
x^2
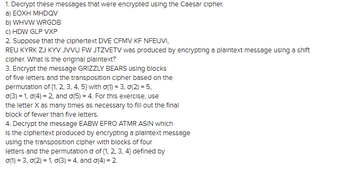
Transcribed Image Text:1. Decrypt these messages that were encrypted using the Caesar cipher.
a) EOXH MHDQV
b) WHVW WRGDB
c) HDW GLP VXP
2. Suppose that the ciphertext DVE CFMV KF NFEUVI,
REU KYRK ZJ KYV JVVU FW JTZVETV was produced by encrypting a plaintext message using a shift
cipher. What is the original plaintext?
3. Encrypt the message GRIZZLY BEARS using blocks
of five letters and the transposition cipher based on the
permutation of (1, 2, 3, 4, 5) with o(1) = 3, 0(2) = 5,
o(3) = 1,0(4) = 2, and o(5) = 4. For this exercise, use
the letter X as many times as necessary to fill out the final
block of fewer than five letters.
4. Decrypt the message EABW EFRO ATMR ASIN which
Is the ciphertext produced by encrypting a plaintext message
using the transposition cipher with blocks of four
letters and the permutation o of (1, 2, 3, 4} defined by
0(1) = 3, 0(2) = 1, o(3) = 4, and o(4) = 2
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 4 steps with 12 images

Knowledge Booster
Similar questions
- Convert the C code below into Pseuedocode ______________________________________________________________ #include <stdio.h>#define max 6 int count = 0, countSpan = 0, cost = 0; struct edge{ int x, y; int value;}; edge list[max];edge spanning[max];int graph[max][max], n; int find(int *belong, int node){ return(belong[node]);} void sort(){ edge temp; for (int i = 1; i < count; i++){ for (int j = 0; j < count - 1; j++){ if (list[j].value > list[j+1].value) { temp = list[j]; list[j] = list[j+1]; list[j + 1] = temp; } } }} void kruskal(){ int belong[max], node1, node2; for(int i = 1; i < max; i++){ for(int j = 0; j < i; j++){ if(graph[i][j] != 0){ list[count].x = i; list[count].y = j; list[count].value = graph[i][j]; count++; } } } sort(); for(int i = 0; i < max; i++){ belong[i] = i; } for(int i = 0; i < max; i++){…arrow_forward427387350304450293426468451389380370387308319335312412308358514444443324508424390426410417 Class Frequency 1. ___ -___ ____ 2. ___ -___ ____ 3. ___ -___ ____ 4. ___ -___ ____ 5. ___ -___ ____ 6. ___ -___ ____ 7.___ -___ ____ 8. ___ -___ ____ Construct a frequency histogram of the data. Descibe any patterns.arrow_forward
Recommended textbooks for you
 Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON
Computer Networking: A Top-Down Approach (7th Edi...Computer EngineeringISBN:9780133594140Author:James Kurose, Keith RossPublisher:PEARSON Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science
Computer Organization and Design MIPS Edition, Fi...Computer EngineeringISBN:9780124077263Author:David A. Patterson, John L. HennessyPublisher:Elsevier Science Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning
Network+ Guide to Networks (MindTap Course List)Computer EngineeringISBN:9781337569330Author:Jill West, Tamara Dean, Jean AndrewsPublisher:Cengage Learning Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning
Concepts of Database ManagementComputer EngineeringISBN:9781337093422Author:Joy L. Starks, Philip J. Pratt, Mary Z. LastPublisher:Cengage Learning Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education
Prelude to ProgrammingComputer EngineeringISBN:9780133750423Author:VENIT, StewartPublisher:Pearson Education Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY
Sc Business Data Communications and Networking, T...Computer EngineeringISBN:9781119368830Author:FITZGERALDPublisher:WILEY

Computer Networking: A Top-Down Approach (7th Edi...
Computer Engineering
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:PEARSON

Computer Organization and Design MIPS Edition, Fi...
Computer Engineering
ISBN:9780124077263
Author:David A. Patterson, John L. Hennessy
Publisher:Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:9781337569330
Author:Jill West, Tamara Dean, Jean Andrews
Publisher:Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:9781337093422
Author:Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:9780133750423
Author:VENIT, Stewart
Publisher:Pearson Education

Sc Business Data Communications and Networking, T...
Computer Engineering
ISBN:9781119368830
Author:FITZGERALD
Publisher:WILEY