
Computer Systems: A Programmer's Perspective (3rd Edition)
3rd Edition
ISBN: 9780134092669
Author: Bryant, Randal E. Bryant, David R. O'Hallaron, David R., Randal E.; O'Hallaron, Bryant/O'hallaron
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Textbook Question
Chapter 10.9, Problem 10.5PP
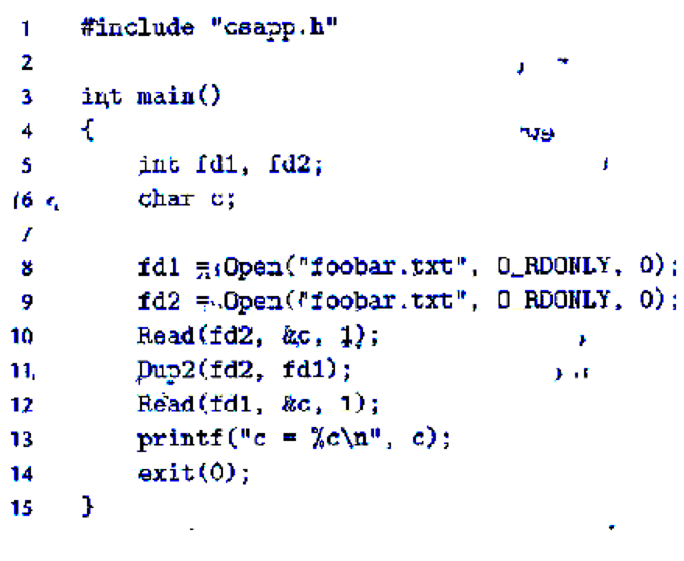
Practice Problem 10.5 (solution page 916)
Assuming that the disk file foobar.txt consists of the six ASCII characters foobar, what is the output of the following
Expert Solution & Answer
Want to see the full answer?
Check out a sample textbook solution
Students have asked these similar questions
(c) Write a Haskell program that:
• Reads two files, called "input1.txt" and "input2.txt".
• Interleaves the lines of the two files.
• Writes the result to a file called "output12.txt" .
You may make use of any functions in the Reference (pp5-7).
Problem 2 (Cipher module)• Create a Python file named cipher_module.py with functions to encode and decodestring inputs using the basic Caesar cipher (see here for more informationhttps://en.wikipedia.org/wiki/Caesar_cipher). This cipher is a basic encryptiontechnique that supports encoding and decoding operations on strings.• The encoding operation replaces each character in a string with another charactersome fixed number (shift) of positions down the ASCII table. The string can beencoded using any characters on the ASCII table and no need to use the circular list(where ‘Z’ is followed by ‘A’) image shown below. Your module must have a functionnamed encode() that takes a string and an integer shift (can be positive or negative)as parameters and returns the encoded string using the shift value. This module must
Page 3 of 4also have a second function name decode() that takes an encoded string and aninteger shift as parameters and returns the decoded string. The decoding…
Huffman Code[Problem Description]For an English article, the frequency of occurrence of 26 lowercase letters is counted, and then they are encoded by Hoffman code.[Basic Requirements]1) Read the original text file from the file and display the text on the screen..2) Output the number of occurrences of 26 English lowercase letters, and the corresponding Hoffman code...
Below is the data to be displayed
At present, most of the dynamic sign language recognition is only for sign language words,the continuous sign language sentence recognition research and the corresponding results are less, because the segmentation of such sentence is very difficult. In this paper, a sign languagesentence recognition algorithm is proposed based on weighted key frames. Key frames can be regardedas the basic unit of sign word, therefore, according to the key frames we can get related vocabularies, and thus we can further organize these vocabularies into meaningful sentence. Such work can avoid the…
Chapter 10 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Ch. 10.3 - Prob. 10.1PPCh. 10.8 - Practice Problem 10.2 (solution page 915) Suppose...Ch. 10.8 - Practice Problem 10.3 (solution page 915) As...Ch. 10.9 - Prob. 10.4PPCh. 10.9 - Practice Problem 10.5 (solution page 916) Assuming...Ch. 10 - Prob. 10.6HWCh. 10 - Prob. 10.7HWCh. 10 - Write a version of the statcheck program in Figure...Ch. 10 - Consider the following invocation of the...Ch. 10 - Prob. 10.10HW
Additional Engineering Textbook Solutions
Find more solutions based on key concepts
Convert the following event handler to use the lambda style.
Java: An Introduction to Problem Solving and Programming (8th Edition)
In most cases, a menu-driven program should be modularized.
Starting Out with Programming Logic and Design (5th Edition) (What's New in Computer Science)
Identify the important constituents of the control mechanism in the routines of the previous problem. In partic...
Computer Science: An Overview (13th Edition) (What's New in Computer Science)
What is an object program?
Absolute Java (6th Edition)
If u = 2, v = 3, w = 5, x = 7, and y = 11, what is the value of each of the following expressions, assuming int...
Java: An Introduction to Problem Solving and Programming (7th Edition)
Why might doctors and nutritionists be interested in a device like DietSensor?
Using MIS (10th Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- I need help with this: (Address book) Write a program that stores, retrieves, adds, and updates addresses as shown in Figure 17.20. Use a fixed-length string for storing each attribute in the address. Use random access file for reading and writing an address. Assume that the size of name, street, city, and zip is 32, 32, 20, 2, 5 chars, respectively.arrow_forwardHuffman Code[Problem Description]For an English article, the frequency of occurrence of 26 lowercase letters is counted, and then they are encoded by Hoffman code.[Basic Requirements]1) Read the original text file from the file and display the text on the screen..2) Output the number of occurrences of 26 English lowercase letters, and the corresponding Hoffman code... HERE IS MY original TEXT to be displayed.. At present, most of the dynamic sign language recognition is only for sign language words,the continuous sign language sentence recognition research and the corresponding resultsare less, because the segmentation of such sentence is very difficult. In this paper, a sign languagesentence recognition algorithm is proposed based on weighted key frames. Key frames can be regardedas the basic unit of sign word, therefore, according to the key frames we can get related vocabularies,and thus we can further organize these vocabularies into…arrow_forward4) (6 Points) You wish to write a script that will analyze the following function: 2x cos(x) y = exp(0. Lx) Write the m-file, fun x.m, required to define this as a MATLAB function.arrow_forward
- (python) Write a function sum_file(f) that takes a filename f. Each line in f contains a single number. You should write to the last line in the file the sum of all the numbers written in the file.arrow_forward(python) 10. Create a function based on the following information: Your mission is to encrypt a secret message (text only, without special chars like "!", "&", "?" etc.) using Caesar cipher where each letter of input text is replaced by another that stands at a fixed distance. For example ("a b c", 3) == "d e f" Input: A secret message as a string (lowercase letters only and white spaces) and number to move text Output: The same string, but encrypted Return: The same string, but encryptedarrow_forwardObjectives: practice with math, while-loops, sentinels, input validation, functions Starting with the provided file circles.py, write a program that uses functions to compute the area and circumference of a circle of a user-specified radius. The program consists of a main () function and two other functions, as follows: main (): Asks the user for the radius of a circle (floating point number). If the user enters a radius of zero, the program prints “Goodbye!" and ends. If the user enters a negative radius, the program prints “Invalid radius!", and asks again for a radius, and keeps asking until the user enters zero or a positive number. If the user enters a positive number, the program calls the two other functions and prints: A circle of radius R has circumference C and area A. (where R is the radius number, C is the calculated circumference, and A is the calculated area.) After printing the circumference and area, the program asks again for a new radius. [20 pts] circumference (r) :…arrow_forward
- Question 4 (PROGRAMMING) A classification algorithm is a kind of machine learning algorithm which is used to assign a label to an object, based on the knowledge of similar objects. Write a C program able to implement the classification algorithm 1-NN. The program receives as input two files and , whose names are passed as arguments from the command line: The file contains a set of N objects (one for each line), each one with the corresponding label. This file is used to train the classification algorithm, which learns how to recognize the known objects. Each line of the file contains the name of the object represented as a string at most 5 characters, a set of M real numbers T1 T2 T3 .. TM, followed by an integer L. The space character is used to separate the elements. The M real numbers are the features that represents an object. The integer L is the object label. The file contains a set of objects to be classified. The format is similar to the file, but the number of rows is NOT…arrow_forward(C++ Language) Create a function that writes to a file named Inventy.txt the information of 8 items. Ask the user for the item's name, the item's quantity in storage, and the item's price and write it to the file. Create a function that reads the file and items' quantity and price to two different arrays. Create a function that computes the subtotal of each item. Implement all functions inside the main program and the computed value should be displayed with the item's name.arrow_forward(5.1) In the context of designing a system that offers a file management capability, e.g., OneDrive, there are some constraints on the acceptable file names. The following three characters {*,$, :} in addition to spaces are not allowed in file names. If any of these four characters appears in a file name, it is replaced by a hyphen (-). Examples: "new file" → "new-file" "important$file" → "important-file" "abc$def gh:ij*klm.txt" → "abc-def-gh-ij-klm.txt" "exam.doc" →→ "exam.doc" i. Design an algorithm that takes a file name as a string and returns a modified name replacing the prohibited characters with hyphens. Use pseudocode to describe your algorithm. Define all operations that are used in your algorithm. ii. What is the runtime complexity of your algorithm?arrow_forward
- (3) Create the final cpp file under Source files and name it 2D Imaging. Write a C++ program to replace the star or asterisk (*) character with any other character of your choice. You may choose to use that ascii code of one of the characters. You must write a 2-Dimenional loop to programmably replace the character. To do this you must list on paper the row and column pairs of the 2D array that stores the given character. You may see a pattern of number series. Use this pattern to write the loops. The image pattern draws a V shape on the 12rows-11column 2D Grid or board. { {' }; '}, '}, '}, '},arrow_forward[no. 21] What does the // operator in Python allow you to do? a. Perform floating point division b. Perform operations on exponents c. Find the remainder of a division operation d. Perform integer divisionarrow_forward(JAVA) AVOID USING BREAKS, CATCH, AND CASE!!!! Texting Translator For this assignment, we are going to work with adding and removing data from arrays, linear search, and File I/O. This program will act as a texting to English converter This program will read a file containing a list of abbreviations used in texting and another file with their English translations. The abbreviations and translations need to be stored in two separate but parallel arrays (Links to an external site.). Open up two new text files inside of Eclipse: Name these text files abbreviations.txt and translations.txt Copy and paste the following list of names into your abbreviations.txt file: 4cuikrkl8l8rlmkm8nvmrsmhuurwu Copy and paste the following list of translations into your translations.txt file: forsee youI know right?okaylatelaterlet me knowmatenever mindareshaking my headyouyou arewhat's up? Starter Code /** * @author * @author * CIS 36B */ import java.util.Scanner; import java.io.File; import…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education
Instruction Format (With reference to address); Author: ChiragBhalodia;https://www.youtube.com/watch?v=lNdy8HREvgo;License: Standard YouTube License, CC-BY