
Computer Systems: A Programmer's Perspective (3rd Edition)
3rd Edition
ISBN: 9780134092669
Author: Bryant, Randal E. Bryant, David R. O'Hallaron, David R., Randal E.; O'Hallaron, Bryant/O'hallaron
Publisher: PEARSON
expand_more
expand_more
format_list_bulleted
Concept explainers
Question
Chapter 5, Problem 5.13HW
A.
Program Plan Intro
Cycles per element (CPE):
- The CPE denotes performance of program that helps in improving code.
- It helps to understand detailed level loop performance for an iterative
program. - It is suitable for programs that use a repetitive calculation.
- The processor’s activity sequencing is measured by a clock that provides signal of some frequency.
A.
Expert Solution
Explanation of Solution
Diagram for instruction sequence:
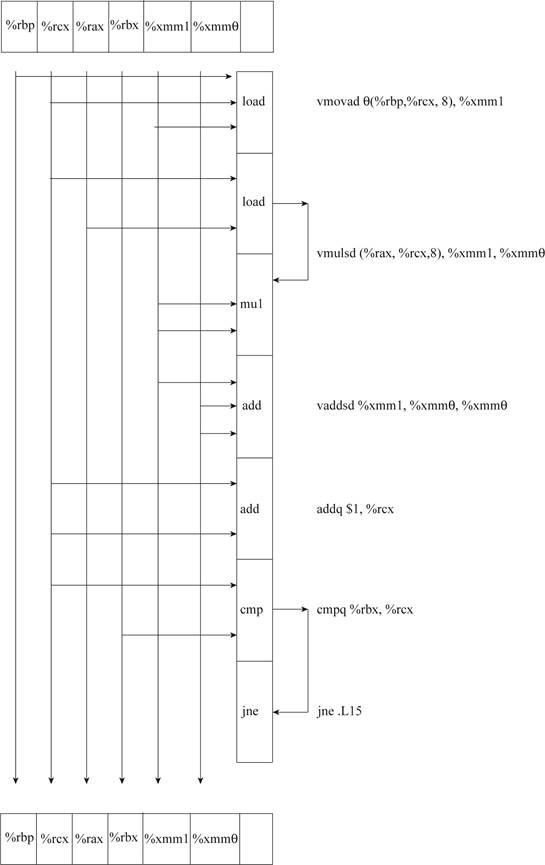
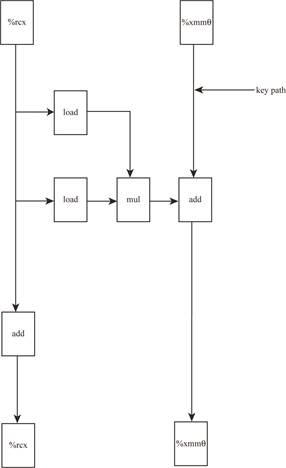
Explanation:
- The data dependencies between instructions are been depicted in diagram.
- The given instruction sequence is been decoded into operations.
- It creates a critical path of operations.
- The data flow between instructions is been shown in diagram.
B.
Program Plan Intro
Cycles per element (CPE):
- The CPE denotes performance of program that helps in improving code.
- It helps to understand detailed level loop performance for an iterative program.
- It is suitable for programs that use a repetitive calculation.
- The processor’s activity sequencing is measured by a clock that provides signal of some frequency.
B.
Expert Solution
Explanation of Solution
Lower bound on CPE:
- The lower bound on CPE is been determined by critical path.
- For data type “double”, it denotes the float add cell.
- The lower bound on CPE is 3.0 based on the architecture.
C.
Program Plan Intro
Cycles per element (CPE):
- The CPE denotes performance of program that helps in improving code.
- It helps to understand detailed level loop performance for an iterative program.
- It is suitable for programs that use a repetitive calculation.
- The processor’s activity sequencing is measured by a clock that provides signal of some frequency.
C.
Expert Solution
Explanation of Solution
Lower bound on CPE:
- The lower bound on CPE is been determined by critical path.
- For data type “integer”, it denotes the long add cell.
- The lower bound on CPE is 1.0 based on the architecture.
D.
Program Plan Intro
Cycles per element (CPE):
- The CPE denotes performance of program that helps in improving code.
- It helps to understand detailed level loop performance for an iterative program.
- It is suitable for programs that use a repetitive calculation.
- The processor’s activity sequencing is measured by a clock that provides signal of some frequency.
D.
Expert Solution
Explanation of Solution
Given C Code:
// Define method inner4
void inner4(vec_ptr u, vec_ptr v, data_t *dest)
{
// Declare variable
long i;
//Compute length of
long length = vec_length(u);
//Get first vector
data_t *udata = get_vec_start(u);
//Get second vector
data_t *vdata = get_vec_start(v);
//Initialize variable
data_t sum = (data_t) 0;
//Loop
for (i = 0; i < length; i++)
{
//Compute product and add
sum = sum + udata[i] * vdata[i];
}
//Store result
*dest = sum;
}
CPE value for floating-point versions:
- The inner product computed is been accumulated in temporary.
- The float add operation is only on key path.
- The multiplication operation takes 5 clock cycles.
- The overall operation takes 3 cycles to complete on average.
- Hence, CPE value for floating-point versions is 3.0.
Want to see more full solutions like this?
Subscribe now to access step-by-step solutions to millions of textbook problems written by subject matter experts!
Students have asked these similar questions
Inner loop of inner4. data_t = double, OP = *
udata in %rbp, vdata in %rax, sum in %xmmo
i in %rcx, limit in %rbx
1
.L15:
loop:
vmovsd 0(%rbp,%rcx,8), %xmm1
vmulsd (%rax,%rcx,8), %xmm1, %xmm1
vaddsd %xmm1, %xmm0, %xmmo
$1, %rcx
%rbx, %rcx
2
Get udata[i]
3
Multiply by vdata[i]
4
Add to sum
addq
Increment i
Compare i:limit
If !=, goto loop
стра
7
jne
.L15
Assume that the functional units have the characteristics listed in Figure 5.12.
A. Diagram how this instruction sequence would be decoded into operations
and show how the data dependencies between them would create a critical
path of operations, in the style of Figures 5.13 and 5.14.
B. For data type double, what lower bound on the CPE is determined by the
critical path?
C. Assuming similar instruction sequences for the integer code as well, what
lower bound on the CPE is determined by the critical path for integer data?
D. Explain how the floating-point versions can have CPES of 3.00, even though
the multiplication operation requires…
Q2: Implement function F (A, B, C) = m (2,4,6,7) using 1:4 deMUX F
(B, C).
Write pseudocode for a function Det-Quicksort(A, p, r) that receives array A[1..n], and indices p and r. The function should sort the subarray A[p..r] recursively (meaning you should call itself). You can also use a function LinearSearch(A, p, r, v) that searches subarray A[p..r] for an element of value v and return its index (in case it exists) in O(r − p) time. (Just to give you something to compare to, the solution has 8 lines.)
Chapter 5 Solutions
Computer Systems: A Programmer's Perspective (3rd Edition)
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Your main task is to write a recursive function sierpinski() that plots a Sierpinski triangle of order n to standard drawing. Think recursively: sierpinski() should draw one filled equilateral triangle (pointed downwards) and then call itself recursively three times (with an appropriate stopping condition). It should draw 1 filled triangle for n = 1; 4 filled triangles for n = 2; and 13 filled triangles for n = 3; and so forth. Sierpinski.java When writing your program, exercise modular design by organizing it into four functions, as specified in the following API: public class Sierpinski { // Height of an equilateral triangle with the specified side length. public static double height(double length) // Draws a filled equilateral triangle with the specified side length // whose bottom vertex is (x, y). public static void filledTriangle(double x, double y, double length) // Draws a Sierpinski triangle of order n, such that the largest filled //…arrow_forwardI need help on how to code this in matlab please. I tried watching tutorials on youtube and they were no help. A vector is given by X = [−3.5 −5 6.2 11 0 8.1 −9 0 3 −1 3 2.5] Using conditional statement and loops, develop a program that creates two vectors from X: Vector P contains all positive elements of X Vector N contains the negative elements of X. The elements in new vectors are in the same order as in X.arrow_forwardImplement a recursive C++ function which takes an array of integers (arr) and the starting(start) and ending (end) indices of a portion (part) of this array, and returns the index of thesecond smallest element present in that portion of array arr. The prototype of your functionshould be:int findSecondSmallest (int* arr, int start, int end)For example, the function call findSecondSmallest(arr,3,8) should determine and return theindex of the second smallest element present in the array arr between the indices 3 and 8(both inclusive)arrow_forward
- Describe an efficient way of putting a VECTOR representing a deck of n cards into random order in C++. You may use the function randomlnt(n), which returns a random number between 0 and n-1, inclusive. Your method should guarantee that every possible ordering is equally likely. What is the running time of your function?arrow_forwardProgram in python There is function F. Give an integer n (n ≥ 2), consider the prime factorization n=PI¹1 P2¹2 Prr Let g=gcd(k₁, k2.... kr) and m, = k₁/g The function F is defined as: F(n) = P11 P22- Pr Now, we have to summing up the value of this function for the first N natural numbers, we have w to evaluate the following expression for a given value of N. F(2) + F(3)+...+F(N). As the above sum can be extremely large Example if F(125)=5, thus the answer for this is by five more than for the previous one.arrow_forwardWrite a program which will read the elements of a sparse matrix from the keyboard and stores in a two-dimensional array in the form of triplet which saves lots of space. Do the above program in reverse that is triplet is given and your program need to print the corresponding sparse matrix in C language.arrow_forward
- Initialize a vector v1 with the following values: 0 23 -7 8 -22 3 14 Write a MATLAB program from the values in v1. The vector v2 should contain the values in v1 transformed as follows: that uses a for-loop and if-statements to make a new vector v2 multiply each positive even element in v1 by 3, multiply each positive odd element of v1 by -2, and change the sign of the negative elements in v1. Then, output the new vector to the command window as follows: The new vector is: -46 7 24 22 -6 42 Also, compute and output the mean of the values in the new vector: The mean of the new vector is: xxxx Above, xxxx is the mean of the values in the new vector with 1 decimal place.arrow_forwardImplement matrix-vector multiplication in Python using MapReduce programming style. The inputs to your program are a matrix and a vector (and user can change the matrix and the vector), and the output is multiplication result. Note that Print the results of map step and the reduce step along the way.arrow_forwardWrite a Python function that takes in three parameters - an adjacency matrix of a simple directed graph, a start node, and an end node; and returns "True" if there is a way to get from the start node to the end node using the provided edges. You can use this file as a starter code: path.py ↓ For example: Using the same graph given above. Consider your function with the same adjacency matrix given above as input and: If the start node is 1 and the end node is 4 then your function should return True. If the start node is 2 and the end node is 4 then your function should return False. Input: This function will have three parameters. First is an adjacency matrix in the form of a list of lists (as given above). Then the start_node and the end_node will be integers. Note that python indexing starts from 0 and not from 1, so the naming of the nodes will also follow the python convention and start from 0 instead of 1. Output: Boolean value: True or False.arrow_forward
- In C program A set of integers 0..MAX may be implemented using an array of boolean values. This particular implementation is called a bit-vector implementation of a Set. Since C doesn’t have the Boolean data type, then substitute TRUE with 1 and FALSE with 0, or define 1 and 0 as TRUE and FALSE, respectively. For example, if the integer 3 is an element of the set, then the array element indexed by 3 is TRUE. On the other hand, if 3 is not an element, then the array element indexed by 3 is FALSE. Implement a programmer-defined data type called BitSet to represent a set as follows: typedef int BitSet[MAX]; Implement the following functions: void initialize(BitSet s); - set all array elements to FALSE void add(int elem,BitSet s); - set the item indexed by elem to TRUE void display(BitSet s); - display the set on the screen using set notation, e.g. {3,4,5,6} - this means that you will print the index value if the content of that cell is TRUE void getUnion(BitSet result,BitSet s1,BitSet…arrow_forwardThe GMP library, using C or C++ The prefered solution is to use the Sage library. 2 Fermat test 1. Implement the Fermat test of primality with small integers. 2. Write a function to generate random k-bit prime numbers. 3 RSA 1. Write the key-generation function function of RSA. The function should generate two random primes p and q of size k/2 bits. 2. Implement the RSA encryption function 3. Implement the RSA decryption function 4. Check that decryption worksarrow_forwardWrite a function REVCOL (in PI [5), int int int M) in C++ to display the content of a two dimensional array, with each column content in reverse order. Note : Array may contain any number of rows. For example, if the content of array is as follows : 15 12 56 45 51 13 91 92 87 63 11 23 61 46 81 The function should display output as: 11 23 61 46 81 13 91 92 87 63 15 12 56 45 51arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education