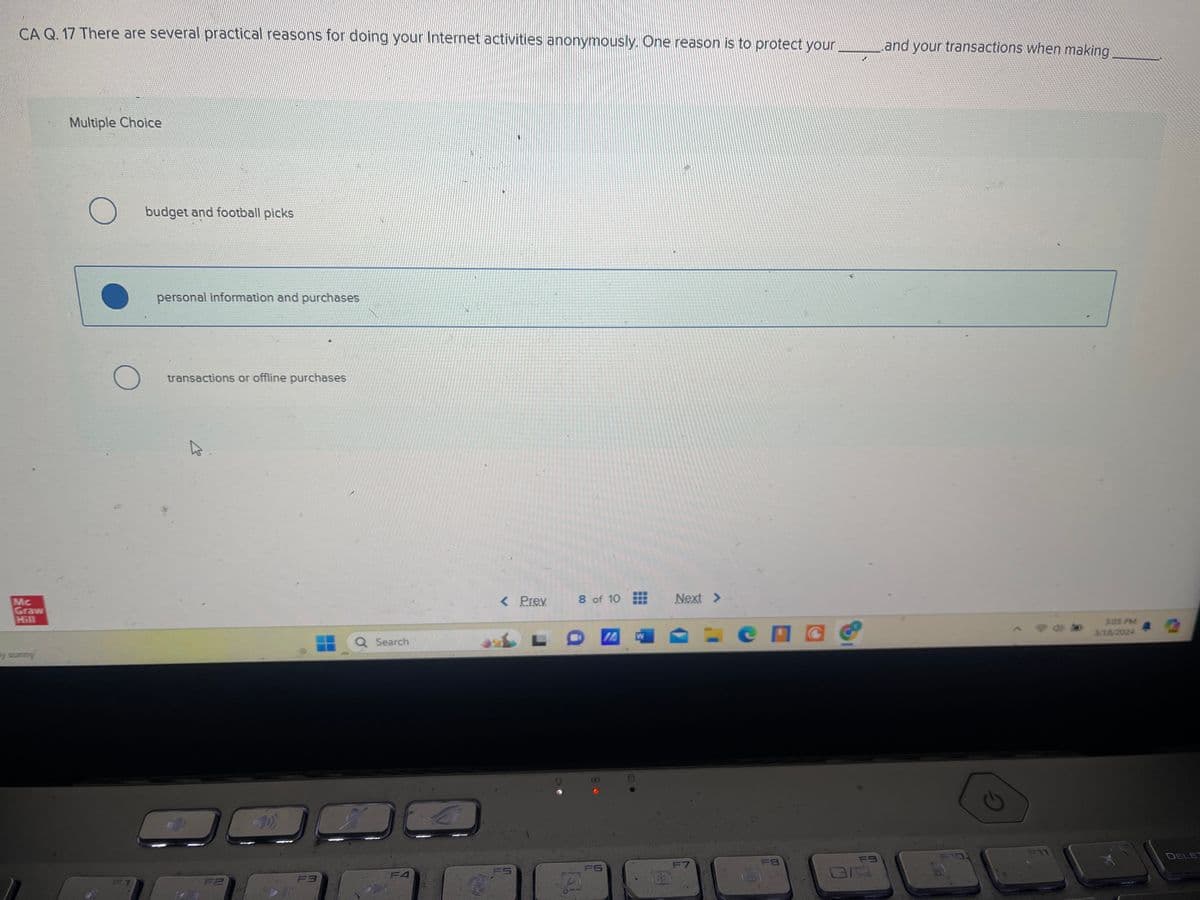
Mc Graw Hill By sunny CA Q. 17 There are several practical reasons for doing your Internet activities anonymously. One reason is to protect your and your transactions when making Multiple Choice О budget and football picks О personal information and purchases transactions or offline purchases 00 F3 Q Search < Prev 8 of 10 Next >> IA Сп FA FS F6 F7 FB F9 G 3:05 PM 3/18/2024 A DELE
Q: Need help in python getting number adding amount of doors/windows, calculating area of each…
A: StartImport the math module.Define a function calculate_paint_needed that takes parameters: length,…
Q: Please help me with these questions. I am having trouble understanding what to do Programming…
A: 1. Start2. Enter a positive integer3. Set number = input4. While number > 0 a. digit = number…
Q: r a vertex v, G[v] = [u such that there is an edge going from v to u]. In the case that G is…
A: In visual depictions of graphs, vertices are typically represented as dots or circles that are…
Q: Write the program by completing the main program that doesthe following:1. Call the push function…
A: #include <stdio.h> #define STACK_EMPTY '0' #define STACK_SIZE 20 void push(char stack[], char…
Q: Hi there, I'm having difficulty with this problem, specifically with part C. I'm unsure about the…
A: To assist with understanding the pushdown automaton (PDA) for the language described in question…
Q: Write an assembly program that checks whether an unsigned number is a prime number or not. Assume…
A: This program checks whether an unsigned number in register R0 is a prime number or not. It sets…
Q: The following details are given for an online store selling books. You are asked to develop the…
A: The objective of the question is to design a database for an online bookstore. The database should…
Q: ssxxvvccfdd
A: Local storage refers to the storing of data on the physical device or the user's computer, as…
Q: Give an O(n^2)-time algorithm to nd the longest monotonically increasing subsequence of a sequence…
A: A Longest Monotonically Increasing Subsequence (LMIS) is the longest sequence of elements within a…
Q: Translate C program to Pep/9 assembly language. /C code for 6.19a #include char myChar;…
A: It takes a basic grasp of both the more detailed, instruction-driven assembly language programming…
Q: Explain the concept of software testing in computer science engineering and discuss its importance…
A: The objective of this question is to understand the concept of software testing in the field of…
Q: lease help me with these question. I am having trouble understanding what to do Programming…
A: A flowchart is a visual representation of a process or algorithm, using various shapes and arrows to…
Q: what are legal issues in line with it professionalisim
A: The question aims to understand the legal issues that are associated with IT professionalism. IT…
Q: I need help with this Java problem to output as it's explained in this image below: import…
A: Binary Search Algorithm:Binary search is a technique used to efficiently search for a target value…
Q: PRACTICE PROBLEM #1 a) Write pseudo code algorithm for a SIGN(X) function. b) Write Using the…
A: The objective of the question is to write a pseudo code for a SIGN(X) function and then use this…
Q: Find the inverse:
A: A−1=⎝⎛−90009000−3⎠⎞Explanation:We find the inverse of matrix A using elementary row operations.…
Q: Q4 You will undertake the role of an IT Support and Network Technician working in a help-desk…
A: The objective of the question is to set up a small wireless network using Cisco Packet Tracer. The…
Q: What is the relationship between a radix or base and the number of symbols in a positional number…
A: The radix, also known as the base, of a positional number system determines the number of unique…
Q: 1. 2. 1 11 12 13 23456 7891) 2 3 4 5 6 7 8 9 10 Formulate the task as a search problem by defining…
A: The puzzle "Nine Little Soldiers" presents a scenario where nine numbered soldiers need to be…
Q: Suppose we have the following pseudocode (i.e. not directly C++ syntax) that executes in the same…
A: In this question we have to execute pseudocode involving operations on a circular queue. The task…
Q: Using ONLY the add, sub and slli instruction to convert the following C statements to the…
A: This RISC-V assembly code is designed to implement a set of arithmetic operations, mirroring the…
Q: Which statement must precede a SHOW TABLES statement to see the tables from the bikeStore database?…
A: Introduction :-The question presented asks which SQL command must be issued prior to a "SHOW TABLES"…
Q: What are the different use cases to use firewall in computer networks?
A: The objective of the question is to understand the different scenarios or use cases where a firewall…
Q: QUESTION 17 Thread-local storage is data that OA) is not associated with any process OB) has been…
A: The realm of concurrent programming is understanding thread-local storage and kernel communication…
Q: Given the logical address 0x 69656, what will be the logical page number issued by a process P? OxD…
A: The objective of the question is to understand the process of translating logical addresses to…
Q: function problem13() { var outputObj = document.getElementById("output"); var inputNumber =…
A: Input:The user inputs a number into the input field.When the button is clicked, the problem13()…
Q: Refer to image and provide correct solution! Computation and automata!
A: The correct statements are:- For a Mealy machine type: A: QA- For a Moore machine type: A:…
Q: The following details are given for an online store selling books. You are asked to develop the…
A: The objective of the question is to design a database for an online bookstore. The database should…
Q: Question No.2: Create the Structured Table for ERP Implementation Lifecycle compiling all Phases →…
A: A complete software program called enterprise resource planning (ERP) unifies disparate business…
Q: Using Intellij IDEA (Using Spring intializer, language: java, type: Maven)
A: To build a web application for Hurricanes Soccer Academy as described, we'll need to follow several…
Q: Make an ER Diagram based on this information below
A: The question requests the creation of an Entity-Relationship (ER) diagram based on the provided…
Q: Select the correct statements about the following sequence diagram: :Specific Flight cancelBooking…
A: The question is asking to identify the correct statements about the given sequence diagram in the…
Q: Make an ER Diagram based on this information below NYU needs a new system to manage reservations of…
A: The objective of the question is to create an Entity-Relationship (ER) Diagram based on the provided…
Q: Σ = {01} (i) Give a DFA, M₁, that accepts a Language L₁ = {all strings that contain 00} (ii) Give a…
A: Deterministic finite automata is a mathematical model used to identify the patterns or strings…
Q: What is the purpose of the network layer in the OSI model? How does network layer handle errors?
A: The purpose of the network layer in the Open Systems Interconnection (OSI) model is to manage…
Q: Draw the high level state machine and data path for: an elevator that can move between floors 1 and…
A: An elevator system involves complex coordination of hardware and software components to ensure safe…
Q: What are some real life examples of sequential logic circuits?
A: These are digital circuits composed of logic gates which utilize the feedback to store information…
Q: Write a program in C that has three float variable (place random values in them) and that will call…
A: Here's the algorithm for the given task:1. Start2. Include necessary header files: `<stdio.h>`…
Q: Lagrange interpolation is well-known to be susceptible to Runge's phenomenon. This is the occurrence…
A: In this question we have to implement the function to generate equidistant points in the interval…
Q: Just need the awk program. Tarball is not necessary
A: The required answer is given below:Explanation:For this task, you can use awk to process the output…
Q: this is what my professor said: 1. Memory starts at 32k, but we always have a leading 1k header, so…
A: The memory management system described in the given scenario utilizes a simple approach for…
Q: reate a program using
A: in this question you have given flowchart and asked to write c program .in the following section you…
Q: Now how do I add an input to that to insert any number, and loops the same question? Code: def…
A: The code first defines a function name as print_asterisks.It takes a number as a parameter.It can be…
Q: The following truth table has 4 inputs, w, x, y, z and 1 output F. Using a Kamaugh map, find a…
A: Boolean expressions in digital logic are like secret codes for electronic circuits. They use binary…
Q: Hello, I'm currently encountering significant challenges in problem-solving and would greatly…
A: The objective of the question is to create a pushdown automata (PDA) for the language defined in…
Q: In a recursive solution, the _____ case is easily calculated, provides a stopping criterion, and…
A: 1.) Base2.) RecursiveExplanation:The base case. this is where the parameter is being checked that…
Q: Explain the concept of object-oriented programming (OOP) and discuss its advantages in software…
A: Software development is the procedure of designing, development, testing, and maintaining software…
Q: Write a program in C that has three float variable (place random values in them) and that will call…
A: Step-1: StartStep-2: Define three float variables a, b & c, and assign random values to…
Q: Task 2: Secondary Index & Aggregation Query Processing Assume the relation CITIZEN(ID,…
A: The objective of the question is to understand the cost of retrieving data using a secondary index…
Q: Throughout, a graph is given as input as an adjacency list. That is, G is a dictionary where the…
A: A vertex, or plural vertices, is a basic unit of a graph in the context of graph theory.A vertex is…
Solve this for me
Unlock instant AI solutions
Tap the button
to generate a solution
Click the button to generate
a solution
- 1. Which of the following statements about the Bitcoin network is INCORRECT: A. In the Bitcoin network, nobody is forced to reveal their real‐life identity. B. In the Bitcoin network, the outstanding transaction pools for all the nodes are always the same. C. In the Bitcoin context, the network is highly imperfect, i.e., not all pairs of nodes are connected to each other in P2P.What is Digital Fingerprinting and for what purposes is it used? Discuss. 2How does the fingerprinting algorithm work? Describe itsprinciple of operation. s. Certain steps are followed to reach the desired result- eitherblock, delete or authorize usage of content. 4.Some cybcrsccunty experts say that fingerprinting is abusiveand exposes the privacy issues of users. Certain solutions were done by some browsers for blocking browser fingerprinting. Describe the measures taken by any of the browsers as afingerprint defense mechanism. s. List two common Fingerprinting Algorithms.1. Aditya is a digital forensics specialist. He is investigating the computer of an identity theft victim. Which of the following is an attack vector that cannot be investigated on the victim's machine? Group of answer choices SQL injection Phishing email Dumpster diving Spyware 4. Bill is an accountant for a construction firm. He receives an urgent email at 5:30 p.m. on Friday that appears to be from his company's chief financial officer. The email is approving a request for funds to be moved from a corporate account to a personal account for the construction manager. The request is for the funds to be moved immediately so that the manager can purchase the equipment needed for a project to be completed over the weekend. Bill notices that the sender's actual email account is from a domain that is not affiliated with the company. What type of attack is likely underway? Group of answer choices Spyware A SQL injection attack Phishing A denial of service (DoS)…
- CSC 385 –Assignment 4 –Faster SortingAlgorithms .This problem is taken from a hackerrank programming challenge. The problem is tagged as having medium difficulty in hacker rank:(https://www.hackerrank.com/challenges/fraudulent-activity-notifications) Problem Description—Fraud DetectionHackerLand National Bank has a simple policy for warning clients about possiblefraudulent account activity. If the amount spent by a client on a particular day is greaterthan or equal to 2 ×the client's medianspending for the last d days, they send the client a notification about potential fraud. The bank doesn't send the client any notificationsuntil they have at least d prior days of transaction data.Given the value of d and a client's total daily expenditures for a period of n days (where n>d) write amethod which returns the number of times the client will receive a notification over all days.Note: Your algorithm time efficiency should not exceed O(nd) where n is the total number of daily…Edward Snowden is directly associated with modern day espionage. His action is an example of insider threats to Information Security. View the following clip and discuss whether Snowden's action for general "public good" justifies his direct violation to extract information from a System he was charged to protect and share it with third parties which includes other countries. Support your answers. https://www.youtube.com/watch?v=H6vkEx5fQnc&t=1s https://www.youtube.com/watch?v=lo8Amd3rYUgComputer Science Please do in virtual machine. attache the screenshot. 1. Use openssl commands to obtain SHA256 hash values for the following messages (Case Sensitive). Cybersecurity CyberSecurity Helloworld! Hello world! 2. Use openssl commands to obtain md5 hash value for the following messages (Case Sensitive). Cybersecurity CyberSecurity Helloworld! Hello world! 3. Show the path and file where the hash value of the user password is stored. Retrieve the line that contains the password/hash value.
- 1-Which asymmetric algorithm is used for establishing a shared key? A. Elliptic CurveB. PGPC. Diffie-HellmanD. RSA 2-What is used to create a message digest that will be attached to data at rest or in transit? Asymmetric algorithm Symmetric algorithm Encryption Hashing Non-repudiation Authentication 3- Which is the most secure method of exchanging secret keys?A. TextB. EmailC. PhoneD. Diplomatic BagsE. Asymmetric Algorithm4) Question 2 asked you to compute the number of possible passwords with various numbers of characters. However, it seems more likely that most people will choose actual words for their password. According to the website wordfinder.yourdictionary.com, the English language has approximately 23,000 six-letter words. a) Assume that a password must be at least 8 characters long and include at least 1 digit and at least 1 special character (again, assume there are 30 of these that are allowed). If people form their password by taking an English word of exactly 6 letters (assume that this password is not case-sensitive) and then adding (in either order) a digit and a special character (e.g flames#1), how many passwords would be possible? (Hint: Find the number of passwords with 6 letters followed by a digit and a special character, then exchange the order of the last two characters.) b) How does your answer change if we assume passwords are case-sensitive and the password must…Hi, I need help witht the following HW.. Recent changes in privacy laws have disallowed organizations from usingSocial Security numbers to identify individuals unless certain restrictionsare satisfied. As a result, most U.S. universities cannot use SSNs as primarykeys (except for financial data). In practice, Student_id, a unique identifierassigned to every student, is likely to be used as the primary key rather thanSSN since Student_id can be used throughout the system.a. Some database designers are reluctant to use generated keys (also knownas surrogate keys) for primary keys (such as Student_id) because they areartificial. Can you propose any natural choices of keys that can be used toidentify the student record in a UNIVERSITY database?b. Suppose that you are able to guarantee uniqueness of a natural key thatincludes last name. Are you guaranteed that the last name will not changeduring the lifetime of the database? If last name can change, what solu tions can you propose for…
- A school is upgrading its website and will require students to create a password to access theirmarks online. In order to create secure passwords, students will be required to meet certainconditions.a. Determine the total number of possible 4-character passwords that can be created using eachof the following requirements: the digits 0 to 9, where the first digit must be even and last digit must be odd, and wheredigits can be repeatedBitcoin mining is also known as proof-of-work because in order to create a valid block, the miner has to spent a significant amount of computational work to figure out a nonce. Therefore, that the hash of the nonce and the block to be proposed is adequately small. Which of the following is NOT a reason to include proof-of-work in the designs of permissionless blockchains? 1. To randomly select nodes in proportion to their computing power. 2. To make mining so costly that miners have incentives to not create invalid blocks. 3. To make it impossible for one miner to act like many different miners. 4. To allow nodes to compete for the right to create blocksSolve using C++ TrustedVocabs.txt contains: acacine acad academe academes Academy academia academial academian academias Academic academical academically .... etc UnTrustedVocabs1.txt contains: acacine acad academe academes Academys academia academial academian academias Academic academical academically ... etc UnTrustedVocabs2.txt contains: acacine acad academe academes Academy academia academial academian academias Academic academical academically academicals ... etc











