What is the difference between authentication and authorization?
Q: Is there a particular application for the authentication process? Which authentication techniques…
A: Given: First, Authentication techniques have pros and cons. Authentication protects networks by…
Q: What Is the Definition of Authentication?
A: Intro When assessing if someone or anything is who or what they claim to be, authentication is the…
Q: What is the purpose of authentication? Compare and contrast the benefits and drawbacks of various…
A: Purpose of authentication: Authentication is used by a server to determine who is accessing their…
Q: Why do different methods of authentication each have their own set of benefits and drawbacks when it…
A: Introduction: Because it is outsourced to a monitoring team or a third party, such as a bank, this…
Q: When it comes to the topic of security, what are the positives and negatives associated with the…
A: Authentication : It is the process of determining a person's identity or object, such as a passport.…
Q: The purpose of authentication is to accomplish what, exactly? The merits and disadvantages of…
A: Purpose: Authentication empowers associations to keep their organizations secure by allowing just…
Q: What is the difference between remote and local user authentication? Which of the following…
A: Introduction: Whenever an Opengear user attempts to log in through one of these methods, the remote…
Q: What distinguishes remote user authentication from local user authentication? Which one posed the…
A: Given: What distinguishes remote user authentication from local user authentication? Which one…
Q: When it comes to the topic of security, what are the benefits and downsides of using various…
A: Authentication: The process of ascertaining whether someone or something is who or what they claim…
Q: In what ways does authentication serve a purpose? Examine the advantages and disadvantages of…
A: Authentication enables organizations to keep their networks secure by permitting only authenticated…
Q: What are the similarities and differences between authentication and authorisation. When it comes to…
A: Authentication is the method involved with checking a client's character and their capacity to get…
Q: What do you mean by the objectives of authentication? Contrast and contrast the advantages and…
A: When a server needs to know who is accessing their information or website but does not want to give…
Q: What are the similarities and differences between authentication and authorization?
A: While authentication and authorization are often used interchangeably, they are separate processes…
Q: What are your goals for the authentication process? Distinguish the advantages and disadvantages…
A: Intro Authentication technology provides access control for systems by checking to see if a users…
Q: Multifactor authentication is beyond my grasp. How does it protect passwords?
A: Multifactor authentication: MFA is an authentication mechanism that requires a user to give two or…
Q: Why do certain authentication techniques work better than others in protecting user information
A: Introduction: Information sent across a functional interface between a source user and a…
Q: In terms of security, how can you tell the difference between the numerous authentication options…
A: In this question we have to understand the different authentication methods we can use for the…
Q: Which aspects of security do various methods of authentication strengthen and which do they weaken?
A: Answer:
Q: How do various authentication techniques compare to one another in terms of the safety they afford?
A: Introduction: Verifying the identity of someone or anything is called authentication. they say they…
Q: What are the specific goals of authentication? Compare and contrast the benefits and drawbacks of…
A: Authentication is the process of determining the identity of an individual process or entity seeking…
Q: What is the mechanism behind two-factor authentication? In what ways does it assist to protect…
A: Two factor authentication is a security measure to protect a system from unauthenticated person who…
Q: Multifactor authentication is a mystery to me. When it comes to preventing password theft, what…
A: Introduction: Multi Authentication is an authentication strategy that requires the client to give at…
Q: What are the exact objectives of authentication? Compare and contrast the pros and cons of different…
A: INTRODUCTION: Different certificates may be connected in a certificate chain. When a certificate…
Q: What is the different between authentication and access control?
A: Difference between authentication and access control.
Q: What exactly is multifactor authentication, and how does it function? What function does it play in…
A: Introduction: Multifactor authentication, also known as MFA, is an approach to protecting computer…
Q: What do you want to accomplish with the authentication process? Distinguish between the advantages…
A: What is authentication? Authentication is the process of identifying users that request access to a…
Q: What aims does the authentication procedure serve? Differentiate the benefits and drawbacks of…
A: Authentication: Authentication is the identification of users seeking access to a system, network,…
Q: Describe how authentication and authorization differ.
A: The following is the difference between authentication and authorization Authentication: Verifying…
Q: Authentication serves what purpose? What are the pros and downsides of different authentication…
A: Authentication: The process of identifying users who wish to access a system, network, or device is…
Q: Is it feasible to differentiate between the various kinds of authentication with regard to the level…
A: Distinguished: To be different from someone else means to value them. People who stand out are…
Q: How is multifactor authentication implemented? What function does this gadget serve in preventing…
A: MFA is also known as Multifactor authentication.
Q: When it comes to the topic of security, what are the advantages and disadvantages of the various…
A: Introduction: Because it is outsourced to a monitoring team or a third party, such as a bank, this…
Q: For what does authentication exist? Comparing and contrasting the pros and cons of different forms…
A: INTRODUCTION: The process of identifying users who seek access to a system, network, or device is…
Q: Describe what a challenge–response system for authentication is and how it works. What makes it more…
A: System of challenge–response In a client-server system, password-based authentication is often used.…
Q: What are the benefits and drawbacks of different authentication techniques when it comes to…
A: Authentication is the process of determining whether someone or something is, such as Users are…
Q: What are the two layers of functionality that make up message authentication or digital signatures?…
A: Introduction: A mathematical method for confirming the validity of digital communications or…
Q: What are the goals of authentication? Distinguish the benefits and drawbacks of different…
A: The goals of authentication and the benefits and drawbacks of different authentication techniques…
Q: What exactly are the objectives of authentication? Compare and contrast the advantages and…
A: Lets see the solution.
Q: In terms of safety, what are the advantages and disadvantages of various forms of authentication?
A: Definition: Because it is outsourced to a monitoring team or a third party, such as a bank, this…
Q: What are the advantages and disadvantages of various techniques of authentication in terms of…
A: Authentication is the process of ascertaining if someone or something is who or what they claim to…
Q: What exactly is two-factor authentication? How does it protect against stolen passwords?
A: According to the information given:-We have to define the two factor authentication and how does it…
Q: What are some of the downsides of using symmetric encryption, particularly when it comes to key…
A: Start: Symmetric encryption uses a single key to encrypt and decrypt data. When you encrypt a…
Q: What exactly is meant by the term multifactor authentication? How exactly does it help to prevent…
A: Authorization is contingent on a number of factors, including: To log into an account or do other…
Q: In what ways are authentication and authorisation different from one another? Is it possible for a…
A: Introduction: Authentication is the validation that users claim to be. This is the initial stage in…
Q: What is the basic goal of user authentication?
A: About the basic goal of user authentication?
Q: What is the difference between remote and local user authentication? Which of the two posed the…
A: Authorization of remote users: It is a process by which a distant server confirms a user's…
Q: What are the authentication goals, and how do you define them? "Compare and contrast the advantages…
A: Intro Authentication is the process of identifying an individual process or entity that is…
What is the difference between authentication and authorization?
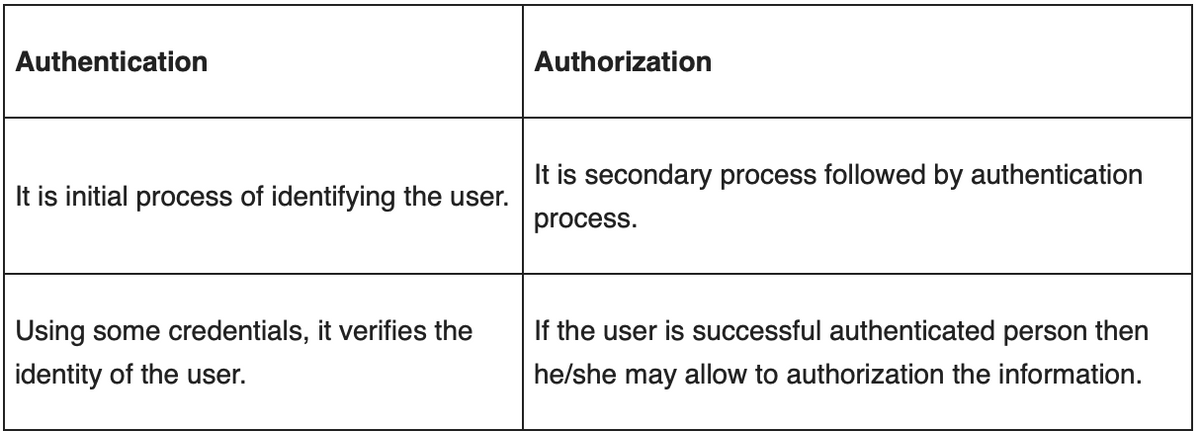
Step by step
Solved in 2 steps with 2 images


