
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
No
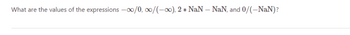
Transcribed Image Text:What are the values of the expressions -∞0/0,00/(-∞), 2* NaN - NaN, and 0/(-NaN)?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps with 2 images

Knowledge Booster
Similar questions
- Discuss the IT-related challenge(s) you have experienced in a University lecture hall during a lecture, giving reasons for the challenge(s) and how the challenge(s) could be resolved. (Please do not use chegg answers)arrow_forwardDifferentiate user interface from user experience, Document the most efficient techniques.arrow_forwardInsects—why? How can bugs enter programs? Example(s).arrow_forward
- Briefly describe architecture of an Expert System.arrow_forwardComputer Science design and analysis of algo course What are the ways to be able to solve all university questions related to P NP ? I need hints, strategies, procedures that I can always follow and lead me to an answer. Much appreciated thank youarrow_forwardExplain design concepts. Describe the design models. What are the phases in the design process?arrow_forward
- Computer science Emerging Practices Characteristicsarrow_forwardComputer science What are some of the pros and cons of privatizing corrections?arrow_forwardProject Analysis, design, and implementation of a Smart City Management Application System features: A smart city has a number of smart buildings and smart streets. The users of the system have different roles and different privileges. The system components in addition to the different users, their roles and responsibilities are presented in the next paragraphs. Smart Buildings: Each building has a number of floors and each floor consists of a number of apartments. A building is characterized by its ID, type (residential, institutional, business, industrial), the smart street where it is located, in addition to the number of residents. Smart buildings integrate renewable energy sources (solar and/or wind) in order to power the building. Apartments in each building have IDs. Each apartment is equipped with a sensor node. These nodes contain the following components: Motion sensor Temperature sensor Humidity sensor Microcontroller Communication module a microcontroller and a…arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education