
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
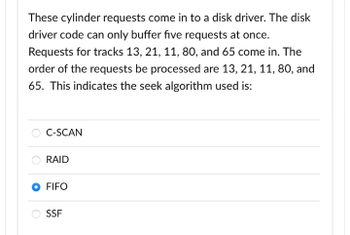
Transcribed Image Text:These cylinder requests come in to a disk driver. The disk
driver code can only buffer five requests at once.
Requests for tracks 13, 21, 11, 80, and 65 come in. The
order of the requests be processed are 13, 21, 11, 80, and
65. This indicates the seek algorithm used is:
C-SCAN
RAID
FIFO
SSF
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- What are the benefits of caching write operations on a disk, and what are the potential drawbacks?arrow_forwardOn succeeding drives, attempts are made to store concurrent sections of a file. Is there a justification for why this is so important for magnetic disks? If SSDs are accessible, is it still essential to use them, or is it a waste of time? What causes this?arrow_forwardHello I am trying to perform the instruction shown in the picture. May someone please help me on getting this function to work?arrow_forward
- Please solvearrow_forwardOperating systems make an effort to save individual pieces of a file in a sequential fashion on disk. So what if we use magnetic disks for it?SSDs: necessary even if you don't use them? Is this anything that we can figure out?arrow_forwardCPU with interrupt-driven I/O is busy servicing a disk request. While the CPU is midway through the disk service routine, another I/O interrupt occurs. Q.) Is it a problem?arrow_forward
- In MIPS assembly how do I clear a file after it is opened?arrow_forwardThere is a maximum number of main partitions that may be established on a hard disc because of this limitation.arrow_forwardWhen a disk has been soft-sectored, an index is written to the disk to show where the first sector is located. Explain?arrow_forward
- When a file is opened for the first time, it is the responsibility of the operating system to ensure that the file's blocks are written to the disc in the right sequence. Is there anything special about magnetic discs that makes this topic deserving of such a great lot of attention? Would it make a difference or not if, rather than traditional hard drives, solid-state drives (SSDs) were used? - What might possibly be causing this?arrow_forwardCan you explain the pros and cons of caching disc write operations?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education