
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
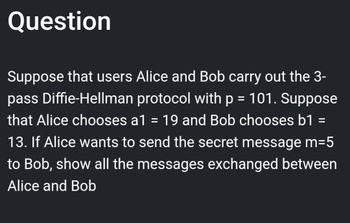
Transcribed Image Text:Question
Suppose that users Alice and Bob carry out the 3-
pass Diffie-Hellman protocol with p = 101. Suppose
that Alice chooses a1 = 19 and Bob chooses b1 =
13. If Alice wants to send the secret message m=5
to Bob, show all the messages exchanged between
Alice and Bob
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Consider an RSA system with n=44916803. Let public exponent e = 6146419. What is the message x if the encrypted word is 1767607? How did you arrive at your answer? Show and explain all your steps.arrow_forwardAssume that Bob & Alice share a secret K. Describe how Alice can authenticate herself to Bob using a message digest?arrow_forwardAssume that Bob and Alice have a secret K that they keep to themselves. Can you explain how Alice can use a message digest to authenticate herself to Bob?arrow_forward
- Encrypt the animal name marmot using the letter to number correspondence abc de f 8hijk 1 mnopar stuvw x y 2 e 1 2 3 4 5 6 7 8 9 18 11 12 13 14 15 16 17 18 19 28 21 22 23 24 25 and the encryption function e :n + (n +1) mod 26 The answer will be a nonsense word (no numbers).arrow_forwardAlice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a=6. Let Bob's public key be Yn=3. A. What is the ciphertext of M-9 if Alice chooses the random integer k=4? B. If Alice uses the same k to encrypt two messages M₁ and M₂ as (12, 65) and (12, 64), what is the relation between M₁ and M₂?arrow_forwardMany forms of cryptography are based on the following discrete log problem. Choose a cyclic group G (produced by one generator g) with finitely many elements. Alice and Bob want to set up a secret communication and need a secret key for that, which becomes a group element from G. They set up the following exchange (the so-called Diffie-Hellman protocol): 1. Alice chooses a secret group element a and sends unsecured g^a to Bob 2.Bob chooses a secret group element b and sends unsecured g^b to Alice 3. Alice calculates (g^b )^a and keeps this group element secret 4.Bob calculates (g^a )^b and keeps this group element secret Since a cyclic group is abelian, Alice and Bob now share the secret key (g^b )^a=(g^a )^b. The blue group elements are publicly known, the red elements are secret. The discrete log problem presented to an eavesdropper is computing say a from the publicly known data G,g,g^a. The naming of the problem comes from the solution a= glog(ga ) which is generally difficult to…arrow_forward
- Design a cryptographic solution for implementing the dinning cryptographers protocol. You should consider the following: The secret messages shared between any two agents in the protocol are communicated over public channels only. The announcements made by each agent must be traceable in a trustworthy way to that agent. Your solution should be a new protocol that addresses the above two requirements.arrow_forwarddont post copied or existing one skip skip if dont knowarrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education