
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
WHICH ANSWER IS IT:
a) All are possibly correct
b )110 100 100 110 101
C) 001 011 011 001 010
D) 110 010 010 111 000
E) 111 101 100 110 111
F) They are all wrong
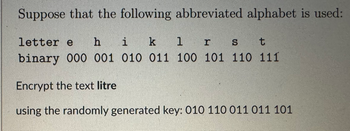
Transcribed Image Text:Suppose that the following abbreviated alphabet is used:
letter e hi k 1 r S
t
binary 000 001 010 011 100 101 110 111
Encrypt the text litre
using the randomly generated key: 010 110 011 011 101
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- e.Given the following contents of Fl, express the contents in both exponent and decimal form: i. 0263795 ii. 1757890 g. How would 374.577 be approximated in FL h. How would zero be represented in FL?arrow_forwardExpress the following decimal numbers in binary, octal, and hexadecimal forms. (498.75) 10 FIND N2 , N8,N16arrow_forwardUsing the SI symbols below, epress the following measurments in engineeing notation rounded to 2 decimal places. a 0,005 A b. 105.000 V c72x 103 v d. 600 x 10-6 A e 7500 0 f0823 x 10-2y Recall Multiplication Factors 1 000 000 000 000 = 10¹2 1 000 000 000 = 10° 1 000 000 10° = = 1 000 10³ 0.00110 3 0.000 001 10 6 10? 0.000 000 001 = 10⁹ 0.000 000 000 001 = 10-12 T T example (370,000,0000) = 370 MO) SI Prefix tera giga mega kilo milli micro nano pico SI Symbol T G M k m 14 13 P A W 8 A 6 Ⓡ 203 Iculator ering ientific tion 10:22 PM Carrow_forward
- Help mearrow_forwardprt d Give (in decimal) the quantity represented by each of the following IEEE 754 single precision floating point values. (a)10111111100000000000000000000000 (b)00000000000000000000000000000000 (c)01111111111111111111111111111111 (d)11000001110110000000000000000000arrow_forwardQuestion 8: Round the following binary numbers to nearest 1/8. Perform round down action in case of "Half way": a) 1011.1111001 b) 11001.101100000arrow_forward
- Given are the following three numbers in their respective bases:a = 1100111012 , b = 4738 , c = 9DA16a) Evaluate i) the sum a + b + cii) the product ac in the octal system. b) Convert each number into its decimal, along with the answer, to verify your result.arrow_forwardTask 1 Sum the following numbers expressed in their respective bases: 11001100112 52014378 93D462C16 Convert your answer to Hexadecimal.arrow_forwardQ7 The following questions refer to the Truth Table below ADWB 0000 001 1 0 10 1 0 1 10 1 000 101 1 1 0 1 1 1 1 1 1arrow_forward
- Solve from question 4 through question 6. Show your workarrow_forwardGenerate the Hamming Codes for the number below and show your work (P0 is started) Original Value: 7310 8CEF = 0111 0011 0001 0000 1000 1100 1110 1111arrow_forward⦁ Compute the checksum for the following data.01101110 11011001 11101101 00101100 11110100 01011010 01111000 11000011 11111000 00001100arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education