
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
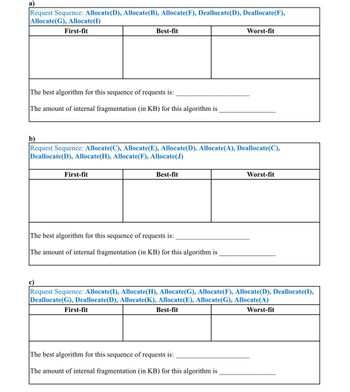
Transcribed Image Text:a)
Request Sequence: Allocate(D), Allocate(B), Allocate(F), Deallocate(D), Deallocate(F),
Allocate(G), Allocate(I)
First-fit
The best algorithm for this sequence of requests is:
The amount of internal fragmentation (in KB) for this algorithm is
Best-fit
First-fit
b)
Request Sequence: Allocate(C), Allocate(E), Allocate(D), Allocate(A), Deallocate(C),
Deallocate(D), Allocate(H), Allocate(F), Allocate(J)
Best-fit
The best algorithm for this sequence of requests is:
The amount of internal fragmentation (in KB) for this algorithm is
First-fit
Worst-fit
c)
Request Sequence: Allocate(I), Allocate(H), Allocate(G), Allocate(F), Allocate(D), Deallocate(I),
Deallocate(G), Deallocate(D), Allocate(K), Allocate(E), Allocate(G), Allocate(A)
Best-fit
Worst-fit
The best algorithm for this sequence of requests is:
The amount of internal fragmentation (in KB) for this algorithm is
Worst-fit
![Process
ABCDEFGHI JK
Size (in KB) 4.27.2 2.5 4.5 3 2.7 1.5|2|3.62.2|1
Allocate(P) represents an allocation request by process P for the size shown in the above table
Deallocate(P) is used to indicate deallocating the memory allocated to process P
To represent memory, in square brackets, we use P to indicate a memory segment allocated to P and
we use an integer to indicate a contiguous free part of memory. For example, after the following
sequence of requests: Allocate(B), Allocate(G), Allocate(H), Deallocate(G) memory will look like
this:
B
8KB
We represent this memory by [B,2,H,4].
free H
2KB 2KB
For each of the following sequence of requests, apply the First-fit, Best-fit, and Worst-fit allocation
schemes. Assume that for each algorithm, you always start at the beginning of the list and if there are
multiple possible equal-size holes that can be selected by an algorithm, the first one is selected. Show
the following:
i. If all the requests can be satisfied, indicate the memory representation at the end of the sequence.
If a request cannot be satisfied by an algorithm, indicate which request is this and the memory
representation at this point. For example, consider adding the request Allocate(X) to the
previous example. The following are answer examples
If X is requesting 6 KB the answer will be:
[B,2,H,4] and Allocate(X) cannot be satisfied
If X is requesting 3 KB, the answer will be
[B,2,H,X,1]
free
4KB
ii. Which method is the best for this particular sequence, and the amount (in KB) of internal
fragmentation at the end of the sequence for this best method.](https://content.bartleby.com/qna-images/question/bbc8a687-c0f0-429c-86f1-046930399c86/eff3eecf-d084-40f0-945a-f4dc0a5e5b8d/k5ieta_thumbnail.jpeg)
Transcribed Image Text:Process
ABCDEFGHI JK
Size (in KB) 4.27.2 2.5 4.5 3 2.7 1.5|2|3.62.2|1
Allocate(P) represents an allocation request by process P for the size shown in the above table
Deallocate(P) is used to indicate deallocating the memory allocated to process P
To represent memory, in square brackets, we use P to indicate a memory segment allocated to P and
we use an integer to indicate a contiguous free part of memory. For example, after the following
sequence of requests: Allocate(B), Allocate(G), Allocate(H), Deallocate(G) memory will look like
this:
B
8KB
We represent this memory by [B,2,H,4].
free H
2KB 2KB
For each of the following sequence of requests, apply the First-fit, Best-fit, and Worst-fit allocation
schemes. Assume that for each algorithm, you always start at the beginning of the list and if there are
multiple possible equal-size holes that can be selected by an algorithm, the first one is selected. Show
the following:
i. If all the requests can be satisfied, indicate the memory representation at the end of the sequence.
If a request cannot be satisfied by an algorithm, indicate which request is this and the memory
representation at this point. For example, consider adding the request Allocate(X) to the
previous example. The following are answer examples
If X is requesting 6 KB the answer will be:
[B,2,H,4] and Allocate(X) cannot be satisfied
If X is requesting 3 KB, the answer will be
[B,2,H,X,1]
free
4KB
ii. Which method is the best for this particular sequence, and the amount (in KB) of internal
fragmentation at the end of the sequence for this best method.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Which of the following algorithms is better to sort a mostly sorted data sequence? A data sequence is mostly sorted if only a handful of integers don't appear in the longest sorted subsequence. For example, the following data sequence is almost sorted since there is only one integer (0) out of place in a sorted sequence of numbers: 1, 2, 3, 4, 0, 5, 6, 7, 8, 9 Question 28 options: merge sort selection sort insertion sort quick sortarrow_forwardQuestion 4 A ) Our List ADT supports: Group of answer choices all the collection operations indices iteration retrieving an element based on its key All of these are correct B )Our Collection ADT supports: Group of answer choices retrieval by priority storage of null first in first out access retrieving an element based on its key All of these are correct Full explain this question and text typing work only thanks All part solution send mearrow_forwardContrast the two advantages of linear search versus binary search.arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education