
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
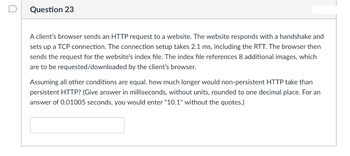
Transcribed Image Text:Question 23
A client's browser sends an HTTP request to a website. The website responds with a handshake and
sets up a TCP connection. The connection setup takes 2.1 ms, including the RTT. The browser then
sends the request for the website's index file. The index file references 8 additional images, which
are to be requested/downloaded by the client's browser.
Assuming all other conditions are equal, how much longer would non-persistent HTTP take than
persistent HTTP? (Give answer in milliseconds, without units, rounded to one decimal place. For an
answer of 0.01005 seconds, you would enter "10.1" without the quotes.)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- The system architecture as used in the above design is ? client/server, peer-to-peer, layered architecture. None of the above Describe the sequence of events captured in the diagram step-by-step. For each step, explicitly describe “Which object sends what message to which object” [the first step is provided as an example]. A user triggers the clickOnLink(v) operation on the webbrowser; [continue from here]arrow_forwardIn which of the following applications, UDP is a suitable transport layerprotocol? (a)In SMTP, a user can send a long e-mail message, which may includemultimedia. When a user sends a message, the recipient does not expectto receive a response quickly. (b)A user needs to download a very large text file from the internet. Theuser doesn’t want part of the file to be missing or corrupted when he/sheopens the file. The delay created between the delivery of the parts arenot an overriding concern for him. (c)In DNS, a client needs to send a short request to a server and to receive a quick response from it. The request and response can each fit in one userdatagram.arrow_forwardComputer Network LAN Network Topology Image. the image below Use the image as a reference, if the values are A, B, C and D (3rd octet) with the following conditions: Value A = 29 Value B = A + 1 Value C = A + 2 Value D = A + 3 x1, y1, z1 are the interfaces for the router gateway, while x2, x3, y2, y3, z2, z3 are for the router interface a. Find the Routing Table R1, R2, and R3 using the following table! Destination Next hop Interface b. With the Routing Table that you have specified in point a, which path will PC1B take when communicating with PC2B and PC3B c. In theory there is a routing table for Network Address 0.0.0.0 with a Subnet Mask of 0.0.0.0, explain the function of this routing table?arrow_forward
- 1. Johnny is a web application designer who is currently debating whether to use persistent or non-persistent HTTP requests for his application. Assuming a web page requires the transfer of 8 objects from the server to the client, please assist Johnny in making this decision by computing how long it would take to receive 8 objects at the client when Johnny is: A. Using persistent HTTP requests B. Using non-persistent HTTP requests Please assume the following: The transfer of an object from the server to the client including the TCP Acknowledgement (ACK) by the client to the server takes 0.01 seconds. 0 The TCP handshake process takes 0.02 seconds. The TCP teardown process takes negligible time and may be ignored. Hint: HTTP messages at the Application Layer are transmitted over the TCP protocol at the Transport Layer.arrow_forwardWhat is the purpose and functionality of the HTTP method?arrow_forwardAccomplish the following tasks involving SNORT rules: Add an appropriate rule options part to the following rule headeralert udp any any any 53 Add an appropriate rule header to the following rule options part(msg:”possible HTTP GET request”; sid:xxxxx; rev:y;) Write a complete rule header and rule options to detect an FTP connection attempt. Explain what the following rule does.alert tcp $HOME_NET 21 any any (msg:"FTP failed login";content:"Login or password incorrect"; sid:xxxxx; rev:y;)arrow_forward
- Primitives of transport service assume asymmetry between the two end points during connection establishment, one end (server) executes LISTEN while the other end (client) executes CONNECT. However, in peer to peer applications such file sharing systems, e.g. BitTorrent, all end points are peers. There is no server or client functionality. How can transport service primitives may be used to build such peer to peer applications?arrow_forwardSMTP (Simple Mail Transfer Protocol) is the standard protocol for transferring mail between hosts. A TCP connection is set up between a user agent and a server program. The server listens on TCP port 25 for incoming connection requests. The user end of the connection is on a TCP port number above 1023. You have defined the packet filter rule set shown in the table below. These rules permit and/or deny inbound and outbound traffic between the user agent and the mail server. Describe the purpose of each packet filter rule in the table. Rule Direction Source Address Destination Address Protocol Destination Port Action A2 In External Internal TCP 25 Permit B2 Out Internal External TCP > 1023 Permit C2 Out Internal External TCP 25 Permit D2 In External Internal TCP > 1023 Permit E2 Either Any Any Any Any Denyarrow_forwardA single link between two hosts can be used to send more than one file. Please tell me when shipments can be cleared. Is there a set amount of time for one wait and some flexibility with the other?arrow_forward
- Can you recommend the best HTTP version for my use case? Explain the function of each status code used in HTTP 2.0 response messages.arrow_forwardwrite a Node/Express web server that supports routing via endpoint /cookie. Declare a variable named a and initialize it to 10 seconds.In the callback of route /cookie:Check to see if the browser sends a cookie named startIf cookie start received by the server, increment value in variable a by 2 seconds.Creates and sends a cookie that expires after the number of seconds specified in the variable a.The cookie is to be named startwith assigned value of 450.Import package cookie-parser for cookie handlingarrow_forwardSuppose an HTTP client makes a first GET request to the gaia.cs.umass.edu web server for a base page that it has never before requested, which contains an embedded object, which causes the client to make a second GET request. A very short time later, the client then makes a third GET request - for the same base page, with that third GET request having an If-Modified-Since field (as does the 4th GET request that the client makes for the embedded object). Neither the base object nor the jpeg object has changed. How many round trip times (RTTs) are needed from when the client first makes the third GET request (i.e., when it requests the base object for the second time) to when the base page and the jpeg file are displayed a second time, assuming that: any time needed by the server to transmit the base file, or the jpeg file into the server's link is (each) equal to 1/2 RTT the time needed to transmit an HTTP GET into the client's link is zero? the time needed by the server to transmit…arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education