Question
PROBLEM 1
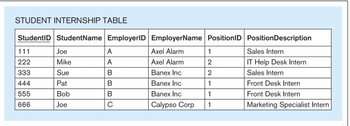
a. Depict full key functional dependencies, partial functional dependencies (if any), and transitive functional dependencies (if any) in the Student Internship Table
b. Show the result of normalizing the Student Internship Table to 2NF.
Transcribed Image Text:STUDENT INTERNSHIP TABLE
StudentID StudentName EmployerID EmployerName PositionID
Axel Alarm
Axel Alarm
Banex Inc
Banex Inc
Banex Inc
Calypso Corp
111
222
333
444
555
666
Joe
Mike
Sue
Pat
Bob
Joe
A
A
B
B
B
с
1
2
2
1
1
1
Position Description
Sales Intern
IT Help Desk Intern
Sales Intern
Front Desk Intern
Front Desk Intern
Marketing Specialist Intern
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps

Knowledge Booster
Similar questions
- What is best way to represent specialization/generalization hierachy if the participation and disjoint constraints are MANDATORY AND NONDISJOINT? A)Student(ssn,name,phone,program), Staff(ssn,name,phone,department) B)Person(ssn,name,phone), PersonDetails(ssn,studentFlag,program,staffFlag,department) C)Person(ssn,name,phone), Student(ssn,program),Staff(ssn,department) D)Person(ssn,name,phone,studentflag,program,staffflag,department)arrow_forwardDecompose the above relation using the Boyce-code normal form decomposition. What is the key relation for the relation Rarrow_forwardGiven the relation R(A, B, C, D, E, F), the following functional dependencies exist: B --> C, DD --> F a) What normal form is the relation R in? b) Normalize relation R to 3NF. You only need to show the final relation schemasarrow_forward
- What is best way to represent specialization/generalization hierachy if the participation and disjoint constraints are MANDATORY AND NONDISJOINT? A)Student(ssn,name,phone,program), Staff(ssn,name,phone,department) B)Person(ssn,name,phone), PersonDetails(ssn,studentFlag,program,staffFlag,department) C)Person(ssn,name,phone), Student(ssn,program),Staff(ssn,department) D)Person(ssn,name,phone,studentflag,program,stafflag,department)arrow_forwardAssume that there is a one-to-one match in the advisor relationship set. What further restrictions are required on the relation advisor to ensure that the one-to-one cardinality criterion is upheld?arrow_forwardSuppose you are given a relation R = (A,B,C,D,E) with the following functional dependencies: {CE -> D,D -> B,C -> A}. Identify the best normal form that R satisfies (1NF, 2NF, 3NF). Explain Whyarrow_forward
- Question 1: Normalization PLEASE WRITE ELIGIBLE AND SHOW FULL STEPS FOR DIAGRAM TO DECOMPOSE Consider a relation X with six attributes WYSMFE where WS is a composite primary key for X. Assume X has the following functional dependencies (X is one table with the attributes W, Y, S, M, F, E): WS è YMFE S è YME E è M Is it possible to decompose X into a number of relations in order to achieve a higher normal form? Explain how (this means using English sentences and a diagram showing the final relation(s)).arrow_forwardNormalization Show all the steps as you perform normalization for each problem up to 3NF. State your final relation to schemas in 3NF.arrow_forwardNormalise the following relation to remove modification anomalies showing all steps for 1NF, 2NF and 3NF . State any necessary assumptions to support your answer. Important : Provide appropriate justification for each normalisation step. STUDENTCOURSE(StudentNumber, StudentName, TotalCredits, GPA, AdvisorNumber, AdvisorName, Office, CourseNumber, CreditHours, Grade) Primary Key: StudentNumber, CourseNumber Functional DependenciesStudentNumber -> StudentName, TotalCredits, GPA, AdvisorNumber, AdvisorName, OfficeAdvisorNumber -> AdvisorName, OfficeCourseNumber -> CreditHoursStudentNumber, CourseNumber -> Gradearrow_forward
- Consider the department relation's foreign-key restriction from the instructor's dept name property. Give instances of inserts and deletes that might violate the foreign-key limitation.arrow_forwardFaculty (facultyNum, deptNum, officeNum, rank, dateHired, salary) ● Where: officeNum deptNum rank, dateHired → salary What is the highest normal form that the above relation satisfies? Decomposition into BCNF:arrow_forwardMake a hybrid merge-join variant that works in scenarios where neither relation is physically sorted but has a sorted secondary index on the joined attributes.arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios