Fill the blank with correct number: If A= {1,2,3} and B = {1,2}, then the set ANB has partitions, and the set AUB has partitions while the set A- B has partitions.
Q: Research and find a current network threat or breach. What happened and what could have been done to...
A: Let us see the answer:- Introduction:- A cyber attack is the intentional compromise of your systems ...
Q: Suppose you were implementing a Company---Employee relationship. Which of these classes would be con...
A: Company comprises (made up of) Employees and hence it is the aggregating class. The existence of the...
Q: What part does Moore's law play in supercomputing, grid computing, and cluster computing?
A: According to Moore's Law: Moore's Law is a computing or technology word that refers to the fact that...
Q: Write a C# Sharp program to print the product of two numbers
A: The above question that is pogram to multiply two number in c sharp language is written below
Q: of the following is False? O Dynamic memory consumes less pow ) Access time of SRAM is less than tha...
A: 1- Static memory consume less power. It is expensive than Dynamic memory. Static memory consumes con...
Q: C+キ 1- find the number of the numbers accept division by 3 between 7 and 88.
A: Algorithm: Start Initialize count to 0 Iterate through the loop from i=7 to i=88 If i%3==0, increme...
Q: What does this do in shell? #!/bin/bash for i in “$@“; do if [-d “$i”]; then chmod 755 “$i” f...
A: "$@" Stores all the arguments that were entered on the command line, individually quoted if [-d “$i...
Q: What is the time complexity (in big-O notation) of binary search in a sorted array containing m (m >...
A: SUMMARY: - Hence, we discussed all the points
Q: What is the size in bits of the tag in the cache?
A: Memory blocks are the blocks which are used for storing the address of the variables and the variabl...
Q: Identify the errors in the following code. class A { void sum(int x, int y){ System.out.println("Sum...
A: The method sum is declared with same signature twice But the second method's usage is demonstrated a...
Q: A shared lock and an exclusive lock
A: Q)A shared lock and an exclusive lock may be explained. Answer: SQL Server locking is the essential ...
Q: 12. Write a code in AVR to load values $30, $15 and $40 using register R16 into locations $101, $102...
A: The avr is an given below :
Q: Write a function that will take list containing numbers as input and return list containing square o...
A: the python program is an given below : numbers = [11, 21, 19, 30, 46] squaredValues = [number ** 2 f...
Q: explain this program to me. For example, why this program wrote like this and etc. please give me as...
A: The usage of default function parameters is demonstrated in this example. It features a feature that...
Q: A friend calls you for help with his home office Internet connection. He is using an 802.11n wirel...
A: Answers:- A friend calls you for help with his home office Internet connection. You are using 802.1...
Q: C++ statements that opens the text file named input.txt and read character by character and display ...
A: the c++ program is an given below : // C++ program to demonstrate read/write of class// objects in C...
Q: 4. Define the Circle2D class that contains: > Two double data fields named x and y that specify the ...
A: Program: -------------------------------------------------------------------------------------------...
Q: Consider the following algorithm: ср ALGORITHM Secret(A[0..n â^' 1]) //Input: An array A[0..n â^' 1]...
A: Given :- 1. What does this algorithm compute?2. What is its basic operation?3. How many times is the...
Q: Give a CFL for the language L (over the alphabet {a, b}), where L = {w | w has exactly the same numb...
A:
Q: What does the plural form of computer mouse mean?
A: Introduction: According to most dictionaries, the plural for a computer mouse is "mice" or "mouses,"...
Q: Write a C# program that accepts your name and age as input from the user
A: Start. Ask the user to input their name and age. Print the same. Exit.
Q: What are the many forms of cloud storage available?
A: Cloud storage is a data storage strategy wherein digital information including such documents, image...
Q: Create a script file that will accept the length of the sides of cyclic quadrilateral and will calcu...
A: Given a quadrilateral , we have asked to calculate its area and radius using the given formula on MA...
Q: Write a full class that represents a Phone, described by a name, price, and then whether the phone c...
A: PROGRAM EXPLANATION: Import the java. util package. Create a phone class. Declare the attributes of...
Q: Create a python code that inputs the complete name (first name/middle name/last name), address, cont...
A: In python input("prompt is optional") is used to take input from keyboard and print("any string" or ...
Q: Part A: Pizza Ordering System You are required to create a Virtual Pizza Shop, based on clients’ req...
A: “Since you have asked multiple questions, we will solve the first question for you. If you...
Q: Campground reservations, part 3: Available campsites Excellent job! This next one's a little more ch...
A: Here I have created a function named availableCampsites(). In this function, I have created an array...
Q: Comparison between (Windows Linux Android Mac OS) ؟
A: Given Comparison between (Windows Linux Android Mac OS) ؟
Q: What are Project Management Knowledge areas? Explain the various types of knowledge areas that proje...
A: Introduction: The project management knowledge areas guide the different factors and protect all met...
Q: ed into New York Harbour in 1524
A: given - Verrazzano, an Italian ____ little is known, sailed into New York Harbour in 1524
Q: . x,y are non-negative integers with x O y = 0. Disprove (with a counterexample) or prove (by induct...
A: Truth table for x xor y:x xor y0 0 = 00 1 = 11 0 = 11 1 = 0 Consider x = y, then if x = 1, y = 1, ...
Q: Determine the validity of the ff. argument: If this variable is larger than 3, then its square is la...
A: given: Determine the Validity of the FF.argument.
Q: What is the correct order for converting the source code into an executable file? Answer Choices: a....
A: The correct order is
Q: We are very dependent on technology for ALL security needs. what are some of the common things you s...
A: check further steps for the answer :
Q: Consider a CFL for Java if-statements: G = ({, , }, {if, condition, else, (, ), stmt}, R, ) where R ...
A: Given grammar G = ({<STMT>, <IF-THEN>, <IF-THEN-ELSE>}, {if, condition, else, (, )...
Q: Use the "it-else To design, develop enter three numbers and the product of those three numbers (the ...
A: First program - import java.util.*; public class Main{ public static void main(String[] args) { Sca...
Q: How features provide in android supported by core libraries?
A: The solution for the above given question is given below:
Q: Based on the fleet management process and workflow described in the case study develop a comprehensi...
A: The leadership of the Fleet: Franchise management is an approach that focuses on maximizing the busi...
Q: What is multiprocessing and how does it work?
A: Multiprocessing in computing, is a method of operation in which two or more processors on a co...
Q: - Convert each of the following decimal numbers to excess-5code: a- (76)10 (67)1o then add the two n...
A: In Excess 5 code each decimal digit is added by 5 (0101) and their equivalent excess 5 code is calcu...
Q: Write a paragraph describing the business venture and what kind of algebra or other calculations and...
A: Mathematics is an important part of managing business. Business and mathematics go hand in hand this...
Q: Consider the diagram of Figure 2.16. A robot is set up 1 meter from a table. The tabletop is 1 mete...
A: Step 1 The answer is given in the below step.
Q: In Ruby programming language, write a program to input the radius of a sphere(in cm) and print the v...
A: As given, we need to write a ruby program that takes radius of the sphere as input and print the vol...
Q: The first step in most classification algorithms is to estimate the probability that a case belongs ...
A: posterior probability
Q: tegers read the sum of all the odd integers read a count of the number of even integers read a co...
A: import java.util.Scanner;public class Test { private static Scanner sc; public static void main(Str...
Q: Which of the ff. input string/s is/are accepted by the automaton? S1 S2 SO 1 O 100101011010010111011...
A: Ans:
Q: What is the time complexity considering the number of primitive operations, i.e. additions and multi...
A: O(n)
Q: Please list at least two advantages and drawbacks an IDS has over an IPS, and two advantages and dis...
A: Please list at least two advantages and drawbacks an IDS has over an IPS, and two advantages and di...
Q: Make a list of the many types of use cases.
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Whenever yo...
Q: layer(s) are involved in encrypting the data of a packet? Which address(es) does not change at each ...
A: The seven layers of the OSI model have their own functionalities and concerned properties. A data pa...
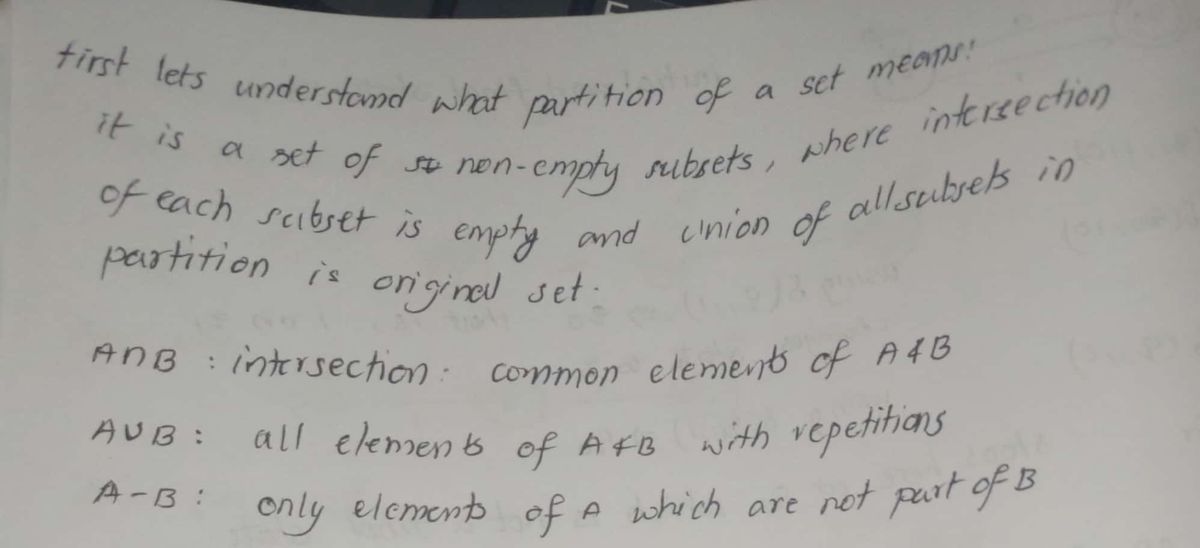
This is an Automata and Computation question on Functions/Sets.

Step by step
Solved in 2 steps with 2 images

- Hef sharks_minnows (minnows, sharks): shark_count = 0 minnow_count = len (minnows) for i in range(minnow_count): curr_shark_height = minnows [i] if curr_shark_height is not None: minnows [i] = None for j in range (i + 1, minnow_count): if minnows [j] == curr_shark_height: minnows [j] = None curr_shark_height -- 1 shark_count += 1 return shark_count <= sharks The provided code is imperfect, in that it sometimes returns True when it should return False, and sometimes returns False when it should return True. (a) Provide an example of a function call where the provided code will correctly return True (i.e. a True Positive) (b) Provide an example of a function call where the provided code will correctly return False (i.e. a True Negative) (c) Provide an example of a function call where the provided code will incorrectly return True (i.e. a False Positive) (d) Provide an example of a function call where the provided code will incorrectly return False (i.e. a False Negative)Regular expression to NFA to DFA conversion: Describes the process of taking a unique regular expression, converting that regular expression to an NFA, then converting the NFA into a DFA. Your regular expression must have at minimum two union, two concatenation, and two Kleene star operations. As followed, concatenations of single charaters can be condensed. Your regular expression cannot be a solved problem from any book. You should describe the regular expression with both processes to convert the regular expression to an NFA and the conversion of that NFA into a DFA.12 - fx =sort(StudentList!A2:F38,2, true) A C 1 Student ID Surname Forename 10009lAkins Lewis 10026 Allen Mary Explain the formula highlighted above and each of the parts in the formular. In other words, briefly describe in your own words what it does and what the result is. For this question, describe the following parameters in the formula above: - StudentList!A2:F38 is the range of cells (A2:F38) pulled from the sheet labeled Studentlist! - ,2 is - ,true is
- Complete the Swap() method in main.c to exchange the values of the num field of two Number struct objects, num1 and num2. Hint: Refer to the given Number struct to see the num data member. Ex: If num1 is 19 and num2 is 178, calling Swap(num1, num2) will swap the values so that num1 becomes 178 and num2 becomes 19.Ex: Let A1 ={x, y}, A2 ={1, 2}, and A3 ={a, b}, Find A1 × A2, (A1 × A2) × A3, A1 × A2 × A3.Consider the set A = {1, 2, 11, {121}, 22, 1212, (111, 212, 112}} Enter the value of Al. (Note: Enter a number).
- Q3: Superheroes Supervillains are tired of Toronto condo rental prices, so they are leaving Toronto for Mississauga. Luckily, we have valiant superheroes that can deal with them. The superhero () has a name , an intelligence score , and a strength score .ni-th0 = gin[x] + s[x] Detective Zingaro has asked for your help. For each of the supervillains, tell him the name of the superhero that should deal with that supervillain. Note: A superhero can be assigned to multiple supervillains (or none at all). Note: whenever there are multiple superheroes that satisfy the given requirements for a supervillain, report the one whose name is lexicographically smallest (i.e. the one that’s the smallest according to Python’s ordering of strings). It’s guaranteed that superheroes have distinct names. Hint: Tuples of multiple elements may be helpful here. In python, you can compare two tuples and . If and are different, the result is the same as comparing and . If and are equal, the result is the same…For this incorrect code dislike please attach code with proof.Given: a variable current_members that refers to a list, and a variable member_id that has been assigned a value. Write some code that assigns True to the variable is_a_member if the value assigned to member_id can be found in the current_members list. Otherwise, assign False to is_a_member. In your code, use only the variables current_members, member_id, and is_a_member.
- Recamán's sequence def recaman_item(n):Compute and return the n:th term of the Recamán's sequence. See the linked definition for this sequence on Wolfram Mathworld. Note how the definition for the current element in this sequence depends on whether some particular number can be found in the previously generated prefix of the sequence. To allow your function to execute in a sure and speedy fashion even for millions of elements, you should use a set to keep track of which elements are already part of the prefix of the sequence generated so far. This way you can generate each element in constant time, instead of having to iterate through the entire previously generated list the way some "Shlemiel" might approach this problem. n Expected result 1 1 8 12 13 23 57 87 395743 258330 The previous version of this problem, simply called recaman in the very first versions of this problem collection,…Ways of writing a set For numbers(1-4), write using roster method while rule method for numbers ( 5-6) and set-builder notation for number ( 7-8) 1.A is the set of even numbers greater than 2 but less than 10. ans: 2.B ={ x/ 2x = 6} ans: 3.C is the set of primary colors. ans: 4.D is the set of odd numbers less than 10. ans: 5.(Rule Method) E = { January, February, March,...} ans: 6.(Rule Method) F = { 1,2,3 , ...,100} ans: 7.(Set Builder Notation)G = { a,b,c,d,e,f,g,h,...,z} ans: 8.(Set Builder Notation)H = { 10,20,30,40,50,...} ans: I am very thankful to the expert that can help me :)ISBNThis problem is slightly more difficult than the above problem. This one requires a data type that stores 10 digits. BackgroundPublishers and bookstores use a number system called the International Standard Book Number (ISBN) system to identify books. At the start of publication, each book is assigned a unique ISBN. An ISBN, once assigned, can never be re-used. Click here for detailed information on this numbering system.An ISBN consists of exactly 10 digits. The rightmost digit is the check digit. The check digit is validated modulo 11.• multiply each digit from the first to the ninth by a weight from 10 to 2 respectively (the first digit by 10, the second by 9,.., the ninth by 2).• the sum of the products plus the check digit should be divisible without remainder by 11.• if there is a remainder, the whole number is not a valid ISBN SpecificationsDesign a program that validates an ISBN. Your program keeps accepting a whole number and determining if that whole number is a valid…











