
COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
1st Edition
ISBN: 9780357392676
Author: FREUND, Steven
Publisher: CENGAGE L
expand_more
expand_more
format_list_bulleted
Question
Please solve these on MATLAB
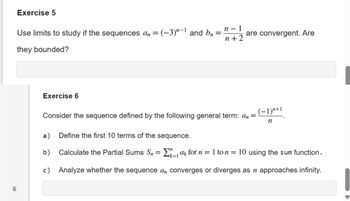
Transcribed Image Text:Exercise 5
Use limits to study if the sequences an = (-3) "-1 and bn
they bounded?
Exercise 6
=
n-1
n+2
are convergent. Are
Consider the sequence defined by the following general term: an =
(−1)"+1
n
6
a) Define the first 10 terms of the sequence.
b)
Calculate the Partial Sums Sn = Σ ak for n = 1 to n = 10 using the sum function.
k=1
c) Analyze whether the sequence a converges or diverges as n approaches infinity.
SAVE
AI-Generated Solution
info
AI-generated content may present inaccurate or offensive content that does not represent bartleby’s views.
Unlock instant AI solutions
Tap the button
to generate a solution
to generate a solution
Click the button to generate
a solution
a solution
Knowledge Booster
Similar questions
- Higher-order functions are the functions that run with higher than O(n) time complexity.Answer: true, falsearrow_forwardAlert dont submit AI generated answer.arrow_forwardALL 18. Recurrence Relation to Runtime Given an algorithm with the recurrence relation of T(n) = T(n-1) + n, what is the Big O runtime? This equation means that there is a function that when called with input size n, it performs n work and then recursively calls the function for the n-1 case. 13 Assume T(0) = 1. 14 Pick ONE option 15 O(nlog(n)) O o(n*(log(n)!) 16 O O(log(n)) 17 18 (n^2) Clear Selection 19 20arrow_forward
- A university assigns student IDs of the form 1, 2, 3, ... such that if n students are currently enrolled, then the next student to enroll will receive and ID of n + 1. Consider the following algorithm that accomplishes this. // Global variable storing number of students currently enrolled current_student_count = 0 // Function that reads the above global variable, calculates new ID, and increments the global count assign_new_id(): count = current_student_count new_id = count + 1 current_student_count = count + 1 return new_id (a) If two different threads run the above code in parallel to enroll two different students, it is possible for the two students to receive the same ID, and for the current_student_count to have a wrong value. Explain how this is possible. (b) Modify the code above so that the problem in (a) does not happen.arrow_forwardBus timetables specify to the second the exact arrival and departure time of each bus on each stop. You need to pay for the full fare of every bus you ride and different bus lines charge different fees , but they are flat fees (independent of distance travelled on the line) A travel plan is a sequence of stop-time pairs where stop is a location of a bus stop and time is when we arrive at that stop. The plan is feasible if for any two consecutive pairs (a, t) and (b, t′) in the plan there exists a bus that departs after t and arrives at b at exactly t′. That is, a travel plan does not allow us to walk between stops. Assuming that no two buses arrive at the same time at the same stop, a feasible plan uniquely identifies the bus lines that we need to take to realize the plan. The cost of the plan is the sum of the fares we need to pay. Your task is to design an efficient algorithm that given a departure time t, an arrival time t′, an origin stop a and a destination stop b, finds the…arrow_forward18arrow_forward
- Use this algorithm to code this pseudocode in Python. Please show all work and show an example matrix in the running of the code.arrow_forwardPython Big-O Coding Exercise Need solving and explanation Pls answer only if u know big-oarrow_forwardd) for (k0; k=0; t = t-1) printf("B"); for-t: TC1iter) = Change of var: Σ/repetitions, Closed form: for-k: TC1iter) =. Change of var: Σ/repetitions Closed form: dependent / independent of loop variable dependent / independent of loop variable e(arrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
- COMPREHENSIVE MICROSOFT OFFICE 365 EXCEComputer ScienceISBN:9780357392676Author:FREUND, StevenPublisher:CENGAGE L

COMPREHENSIVE MICROSOFT OFFICE 365 EXCE
Computer Science
ISBN:9780357392676
Author:FREUND, Steven
Publisher:CENGAGE L