
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
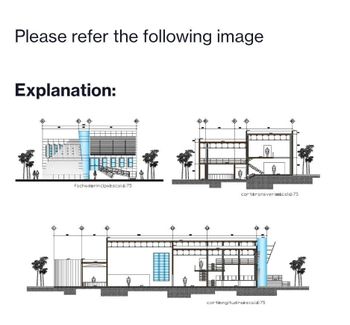
Transcribed Image Text:Please refer the following image
Explanation:
IMA
fachad@rincipalescold 75
Ⓡ
www
corteransversascold 75
corteongitudinaescala:75
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- What does the term 'phishing' signify to you?arrow_forwardI am having issues getting my access code for this book? Is there any way you can help me find it or give me the directions to how to find it on my yuzu account?arrow_forwardA retinal scanner is an example of: biometric authentication single sign-on multi-factor authentication a security tokenarrow_forward
- The first U.S. law to define computer trespass is: Computer Misuse Act O Federal Information Security Management Act O Computer Fraud and Abuse Act of 1984 O Sarbanes-Oxley Actarrow_forwardEncrypt the message using Caesar cipher with alphabetical shift 18 . CORONAVIRUS DISEASEarrow_forwardHow can I protect myself from falling prey to phishing scams?arrow_forward
- Take into account the following: You get a message from the company's email server asking you to verify a password change. The password hasn't been changed, has it? When and why did you decide to switch your password? How did an attacker get access to change the password? Was there a virus, and if so, on which computers?arrow_forwardDo you think it's possible to fake an RSA-based digital signature? If you disagree with the statement, please explain why.arrow_forwardThe term "cybercrime" is notoriously difficult to pin down, but what precisely does it refer to?arrow_forward
- What word is considered "dirty" and why?arrow_forwardDoes the law say anything about what hacking is?arrow_forwardTake into account the following: You get a message from the company's email server asking you to verify a password change. The password hasn't been changed, has it? When and why did you decide to switch your password? How did an attacker get access to change the password? Was there a virus, and if so, on which computers?arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education