
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
a. Draw a circuit which produces Sum and CarryOut from inputs A and B (this circuit is known as a half adder). You should use exactly one AND gate and one XOR (exclusive or) gate.
b. Give the truth table for a full adder (which incorporates a carry-in bit to the sum of A and B):
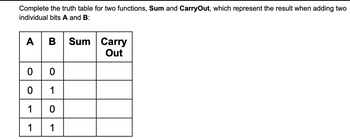
Transcribed Image Text:Complete the truth table for two functions, Sum and CarryOut, which represent the result when adding two
individual bits A and B:
A | B Sum Carry
Out
00
0
1
1
0
1
1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Explain.........arrow_forwardDetermine the final output states over time for the following circuit, built from D-type gated latches: D Q A Output E E B A Gad B Gad Output Gadarrow_forwardConsider the following gates. Please provide the truth table for each gate. Recall that a small bubble on an input or output is an inverter. True (1) becomes False (0) and False(0) becomes (1). B Do-Output A A B A A B A B Do B D B Output Output Output Output Outputarrow_forward
- Design a code converter that converts an unsigned number a into its negative 2's complement representation -a. Specifically, the circuit has two inputs: a1 and ao, and three outputs: b1 and bo (the equivalent to -a) and valid, which is 1 when -a can be represented in 2's complement and O otherwise. 1. Write the truth table for the code converter. 2. Give the simplest SOP expressions for the functions b1, bo, and valid.arrow_forwardPROBLEM 2 4-bit decrement In class we considered an increment circuit that adds 1 to its input value. Now we want a circuit that subtracts 1 (i.e., z = x − 1). Draw a 4-bit decrement circuit that does not use not gates. -arrow_forwardDesign a 16 bit adder/subtractor with 2 data inputs (B15 to B0 and A15 to A0), a SEL input (1 if add and 0 if subtract), and a result output (R15 to R0).You can design the circuit in MultiSim, VHDL, or LabVIEW. PLEAE USE MULTISIMarrow_forward
- 0 0 0 0 (a) Complete the following truth tables by simulating the 3-input circuits implemented in the previous steps. Input1 Input2 Input3 0 0 0 0 1 1 1 1 0 0 1 1 0 0 1 1 0 1 0 1 0 1 0 1 Output of 3-input built-in XOR gate Output of 3-input XOR gate in Step4(c)arrow_forwardDraw a circuit that uses only one AND gate and one OR gate to realize each of the following functions: (a) ABCF + ACEF + ACDFarrow_forwardWrite a Boolean expression for a NOR gate. F(A, B) = Write the Boolean expression for a four-input NOR gate. F(A, B, C, D) = To implement a 1-bit adder, write a Boolean expression for the Carry function. CarryOut(A, B, C;) = Input: A, B Carry in: C 2 pts 2 pts 2 ptsarrow_forward
- Give the symbol and truth table for the following gates: AND, OR, XOR, NAND and NOR. Do not forget to include the inputs and outputs wires.arrow_forward4. A combinational circuit is defined by the following two Boolean functions: F₁ = B'C + AB F₂ = BC + AB Design the circuit with a decoder and two external OR gates.arrow_forwardplease solve asaparrow_forward
arrow_back_ios
SEE MORE QUESTIONS
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education