Advanced Engineering Mathematics
10th Edition
ISBN: 9780470458365
Author: Erwin Kreyszig
Publisher: Wiley, John & Sons, Incorporated
expand_more
expand_more
format_list_bulleted
Question
LET A=0 -> Z=25
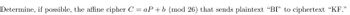
Transcribed Image Text:Determine, if possible, the affine cipher C = aP + b (mod 26) that sends plaintext "BI" to ciphertext "KF."
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution
Trending nowThis is a popular solution!
Step by stepSolved in 3 steps

Knowledge Booster
Similar questions
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Advanced Engineering MathematicsAdvanced MathISBN:9780470458365Author:Erwin KreyszigPublisher:Wiley, John & Sons, Incorporated
Advanced Engineering MathematicsAdvanced MathISBN:9780470458365Author:Erwin KreyszigPublisher:Wiley, John & Sons, Incorporated Numerical Methods for EngineersAdvanced MathISBN:9780073397924Author:Steven C. Chapra Dr., Raymond P. CanalePublisher:McGraw-Hill Education
Numerical Methods for EngineersAdvanced MathISBN:9780073397924Author:Steven C. Chapra Dr., Raymond P. CanalePublisher:McGraw-Hill Education Introductory Mathematics for Engineering Applicat...Advanced MathISBN:9781118141809Author:Nathan KlingbeilPublisher:WILEY
Introductory Mathematics for Engineering Applicat...Advanced MathISBN:9781118141809Author:Nathan KlingbeilPublisher:WILEY Mathematics For Machine TechnologyAdvanced MathISBN:9781337798310Author:Peterson, John.Publisher:Cengage Learning,
Mathematics For Machine TechnologyAdvanced MathISBN:9781337798310Author:Peterson, John.Publisher:Cengage Learning,

Advanced Engineering Mathematics
Advanced Math
ISBN:9780470458365
Author:Erwin Kreyszig
Publisher:Wiley, John & Sons, Incorporated
Numerical Methods for Engineers
Advanced Math
ISBN:9780073397924
Author:Steven C. Chapra Dr., Raymond P. Canale
Publisher:McGraw-Hill Education

Introductory Mathematics for Engineering Applicat...
Advanced Math
ISBN:9781118141809
Author:Nathan Klingbeil
Publisher:WILEY

Mathematics For Machine Technology
Advanced Math
ISBN:9781337798310
Author:Peterson, John.
Publisher:Cengage Learning,