
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
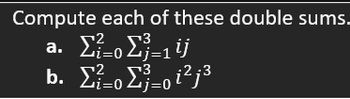
Transcribed Image Text:Compute each of these double sums.
a. Στο Σ=1ij
b. Στο Σ=oi2j3
Zj=0
Expert Solution
arrow_forward
Step 1
Your answer is given below with an explanation.
Note : I use Sigma in the place of summation(Σ).
Step by stepSolved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Given a positive integer 'n', find and return the minimum number of steps that 'n' has to take to get reduced to 1. You can perform any one of the following 3 steps:1.) Subtract 1 from it. (n = n - 1) ,2.) If its divisible by 2, divide by 2.( if n % 2 == 0, then n = n / 2 ) ,3.) If its divisible by 3, divide by 3. (if n % 3 == 0, then n = n / 3 ). Write brute-force recursive solution for this.Input format :The first and the only line of input contains an integer value, 'n'.Output format :Print the minimum number of steps.Constraints :1 <= n <= 200 Time Limit: 1 secSample Input 1 :4Sample Output 1 :2 Explanation of Sample Output 1 :For n = 4Step 1 : n = 4 / 2 = 2Step 2 : n = 2 / 2 = 1 Sample Input 2 :7Sample Output 2 :3Explanation of Sample Output 2 :For n = 7Step 1 : n = 7 - 1 = 6Step 2 : n = 6 / 3 = 2 Step 3 : n = 2 / 2 = 1 SolutionDp///.arrow_forwardGiven a positive integer 'n', find and return the minimum number of steps that 'n' has to take to get reduced to 1. You can perform any one of the following 3 steps:1.) Subtract 1 from it. (n = n - 1) ,2.) If its divisible by 2, divide by 2.( if n % 2 == 0, then n = n / 2 ) ,3.) If its divisible by 3, divide by 3. (if n % 3 == 0, then n = n / 3 ). Write brute-force recursive solution for this.Input format :The first and the only line of input contains an integer value, 'n'.Output format :Print the minimum number of steps.Constraints :1 <= n <= 200 Time Limit: 1 secSample Input 1 :4Sample Output 1 :2 Explanation of Sample Output 1 :For n = 4Step 1 : n = 4 / 2 = 2Step 2 : n = 2 / 2 = 1 Sample Input 2 :7Sample Output 2 :3Explanation of Sample Output 2 :For n = 7Step 1 : n = 7 - 1 = 6Step 2 : n = 6 / 3 = 2 Step 3 : n = 2 / 2 = 1 SolutionDp///.arrow_forwardCorrect answer will be Upvoted else downvoted. Thank you! In base 26, multiplication of YES by NO gives – i) THWOE ii) MPAHT iii) MPJNS iv) THWAEarrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education