
Database System Concepts
7th Edition
ISBN: 9780078022159
Author: Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher: McGraw-Hill Education
expand_more
expand_more
format_list_bulleted
Question
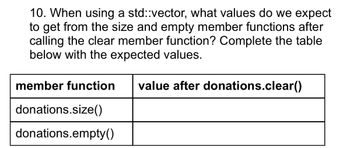
Transcribed Image Text:10. When using a std::vector, what values do we expect
to get from the size and empty member functions after
calling the clear member function? Complete the table
below with the expected values.
member function value after donations.clear()
donations.size()
donations.empty()
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by stepSolved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Similar questions
- Probelm part 1: Define a function called common_divisors that takes two positive integers m and n as its arguments and returns the list of all common divisors (including 1) of the two integers, unless 1 is the only common divisor. If 1 is the only common divisor, the function should print a statement indicating the two numbers are relatively prime. Otherwise, the function prints the number of common divisors and the list of common divisors. Complete each to do with comments to expalin your process. Problem part 2: complete the following todo's and make comments to explain each step # TODO: Define the function 'common_divisors' with two arguments 'm' and 'n'. # TODO: Start with an empty list and append common divisors to the list. # TODO: Create a conditional statement to print the appropriate statement as indicated above. Problem part 3: Call the function common_divisors by passing 5 and 38. Your output should look like this: 5 and 38 are relatively prime. # TODO: Call…arrow_forwardC++arrow_forwardin C code not c++arrow_forward
- Find errors / syntax error. Write line numberarrow_forwardTRUE OR FALSE, C++ When passing an array to a function, you must include & in front of the array name. When passing an array to a function, you must include & in front of the array name. It is possible to have a 2-dimensional array where each row has a different number of columns. The * is called the address of operator.arrow_forwardDeclare a vector of integers in C++ named vec and initialize the vector to 10, 20, 30, 40, and 50. Modify the first element of the vector to be 100 and modify the last element to be 1000. The resulting vector should then be 100, 20, 30, 40, and 1000. Using cout statements, display the resulting vector to the terminal.arrow_forward
- Game of Hunt in C++ language Create the 'Game of Hunt'. The computer ‘hides’ the treasure at a random location in a 10x10 matrix. The user guesses the location by entering a row and column values. The game ends when the user locates the treasure or the treasure value is less than or equal to zero. Guesses in the wrong location will provide clues such as a compass direction or number of squares horizontally or vertically to the treasure. Using the random number generator, display one of the following in the board where the player made their guess: U# Treasure is up ‘#’ on the vertical axis (where # represents an integer number). D# Treasure is down ‘#’ on the vertical axis (where # represents an integer number) || Treasure is in this row, not up or down from the guess location. -> Treasure is to the right. <- Treasure is to the left. -- Treasure is in the same column, not left or right. +$ Adds $50 to treasure and no $50 turn loss. -$ Subtracts…arrow_forwardc++ programming Write a function named maxCols which stores the maximum value in each row of a 3x3 2D array into a 1D array. This function should accept a 3x3 2D array, a 1D array and the size of each dimension as parameters. Example Calling maxCols with this 2D array:3 7 2 9 3 6 8 5 6 Results in the 1D array storing the values 7,9,8.arrow_forwardC++arrow_forward
arrow_back_ios
arrow_forward_ios
Recommended textbooks for you
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education

Database System Concepts
Computer Science
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:9780134444321
Author:Tony Gaddis
Publisher:PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:9780132737968
Author:Thomas L. Floyd
Publisher:PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:9780133976892
Author:Paul J. Deitel, Harvey Deitel
Publisher:PEARSON

Database Systems: Design, Implementation, & Manag...
Computer Science
ISBN:9781337627900
Author:Carlos Coronel, Steven Morris
Publisher:Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:9780073373843
Author:Frank D. Petruzella
Publisher:McGraw-Hill Education