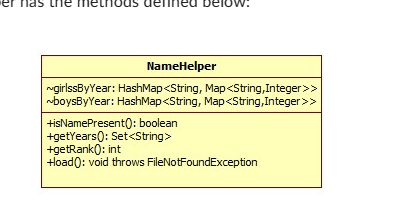
What does the (~) mean in the attached diagram.
Q: Q4: Make a List Create the list with the following box-and-pointer diagram: 1 (define 1st | → 2 3 5…
A: (define (make-adder num) 'YOUR-CODE-HERE)
Q: do this in C++ please read carefully and follow every instructions please do not copy or plagarise.…
A: Start.Define a class TA to represent Teaching Assistants with relevant attributes.Implement a…
Q: Explain the significance of feedback in a dynamic system model.
A: When it comes to system models feedback plays a role in maintaining stability, improving performance…
Q: Discuss the features and benefits of using Field-Programmable Gate Arrays (FPGAs) in comparison to…
A: When it comes to system design both Field Programmable Gate Arrays (FPGAs) and microcontrollers play…
Q: Analyze the role of magnetic storage technologies in modern computing, exploring advancements and…
A: Since magnetic storage systems offer a non-volatile and affordable way to store enormous amounts of…
Q: Discuss the challenges and benefits of developing software for distributed systems.
A: In this question we have to understand about the challenges and benefits of developing software for…
Q: We are given three ropes with lengths 7₁, n2, and n3. Our goal is to find the smallest value k such…
A: The problem at hand involves finding the smallest value of k such that three ropes of lengths n1,…
Q: Q\Draw a flowchart and write a java program which generates first 50 items of the Fibonacci series:…
A: In step 2 , I have provided FLOWCHAR for the given code...In further steps, I have provided JAVA…
Q: In a bit-oriented link-layer protocol, the start and end of a frame are each marked by a flag, which…
A: The bit-oriented link-layer protocol employs a 6-bit consecutive 1s flag at the frame's start and…
Q: Discuss the hybrid kernel approach and its relevance in modern operating systems.
A: The hybrid kernel approach is a design strategy in operating systems that integrates features from…
Q: Explain the process of flashing firmware onto a microcontroller and the tools involved.
A: When it comes to embedded systems flashing firmware onto a microcontroller is a step.This process…
Q: The question is in bold the below information is just extra as a guide Use perf_count to generate…
A: Merge Sort AlgorithmInput: - An array 'arr' of length 'n'Procedure merge_sort(arr): If the…
Q: What is the purpose of ICMP (Internet Control Message Protocol), and how does it assist in…
A: The Internet Control Message Protocol (ICMP) can be defined in such a way that it is a community…
Q: What is the type(s) of user testing that your team plans to run? Associate the types of user testing…
A: In this question we have to understand about type of user testing and feature based released…
Q: In C++ language Magic Decoder Ring. A one-time pad is a coding device that uses each character of a…
A: Start.Create a MagicDecoderRing class with private members for clear text and key text.Implement…
Q: What is the significance of microcontrollers in embedded systems?
A: A microcontroller is a small integrated circuit that has memory, programmable peripherals for input…
Q: How does a real-time operating system differ from a time-sharing operating system?
A: Operating systems play a crucial role in managing computer resources and enabling the execution of…
Q: Describe the role of firmware in the operation of microcontroller-based devices.
A: The role of firmware is incredibly important when it comes to microcontroller-based devices.Unlike…
Q: Discuss the role of design patterns in software development, providing examples of commonly used…
A: Design patterns are solutions that often occur in software design to address problems.They serve as…
Q: Make a relational diagram with the following data: 1. Patient Entity: RUT (Primary Key): Integer…
A: In this question we have to understand about the given relation ships and design a relationship…
Q: python help Q8: Substitute Write a procedure substitute that takes three arguments: a list s, an…
A: Step-1: StartStep-2: Define function substitute(s, old, new) Step-2.1: If isinstance(s, list)…
Q: Discuss the role of optical storage devices in modern computing.
A: Modern computing refers to the current state and practices of using advanced technologies, hardware,…
Q: Jurisdiction -name:String -pop16:int -pop23:int +calculate Change:double
A: The objective of the question is to calculate the change in population from 2016 to 2023 for a given…
Q: Describe the role of interrupts in microcontroller programming and their significance.
A: Interrupts are a mechanism in computing that allows a running program to be…
Q: Discuss the importance of memory management in embedded systems and how it is typically handled in…
A: Memory management in embedded systems involves the strategic allocation, utilization, and…
Q: Explain the principles of Test-Driven Development (TDD) and how it contributes to robust software…
A: Test-driven development (TDD) is a software improvement technique that emphasizes writing…
Q: Elaborate on the concept of real-time operating systems (RTOS) in the context of microcontrollers.
A: Real time operating systems (RTOS) play a role in microcontrollers, where precise and timely task…
Q: Explain the concept of virtualization in system modeling, outlining the benefits and applications of…
A: Virtualization in system modeling is a technique that involves creating a version than an actual…
Q: Write a function triple_riffle_repeat(mylist,n) which takes as input a list (again with length a…
A: triple_riffle_shuffle(mylist) takes a list as input and performs a 3-way riffle shuffle on it. The…
Q: Explain the basic architecture of a microcontroller. Discuss the components and their roles in the…
A: A microcontroller is a tiny, programmable computer chip inside an electrical device that controls…
Q: This message 11001100 needs to be send after applying 4 PARITY EVEN Hamming code. Show the full…
A: In the context of error detection and correction, a user wishes to apply a 4-bit even parity Hamming…
Q: Explain the concept of continuous integration/continuous deployment (CI/CD) and describe its…
A: The objective of this question is to understand the concept of Continuous Integration/Continuous…
Q: Question- What are file attributes? requirements- -please answer the question correctly using the…
A: File attributes encompass various metadata elements associated with files, providing crucial…
Q: Create a "Branflake" program that will accept two integers in the form of a string "x+y", add the…
A: Accept a string input in the form "x+y".Split the string to extract two integer values, x and y.Add…
Q: 4.18 LAB: Output range with increment of 5 Write a program whose input is two integers, and whose…
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT...
Q: Discuss the concept of cloud storage, outlining its advantages and potential concerns in comparison…
A: Using distant servers connected to the internet, cloud storage enables user to store and find their…
Q: Explain the OSI model and its seven layers, detailing the functions and protocols associated with…
A: The OSI (Open Systems Interconnection) model is a framework that standardizes the functions of a…
Q: Explore the concept of subnetting in networking. Provide examples and explain how subnetting…
A: Every device connected to a computer network that employs the Internet Protocol for communication is…
Q: Explain the concept of microkernel architecture in operating systems and discuss its key features.
A: Microkernel architecture is a design approach used in operating systems where the kernel is kept…
Q: Explain the importance of a system model in understanding system behavior.
A: Sensitivity analysis involves systematically varying one or more input parameters while keeping…
Q: Elaborate on the concept of dependency injection and its role in achieving loose coupling in…
A: In this question we have to understand about the concept of dependency injection and its role in…
Q: So right now in my iphone, I have my notifications display set to "list" and have notification…
A: When many notifications from the same app or discussion are arranged into a neat stack or bundle for…
Q: Discuss the challenges and solutions related to network security, focusing on protocols such as…
A: Network protocols can be defined in such a way that they are the essential building blocks of net…
Q: Assume list1 is a list of integers. Write a statement that uses a list comprehension to create a…
A: Initialize list1 with a list of integers.Use a listing comprehension to iterate over each element x…
Q: In computer networking what are the primary differences between the OSI model and the TCP/IP model,…
A: The networking models serve as a basis of the transmission of data through the network. There are…
Q: Describe the microkernel architecture and its potential benefits in operating systems.
A: Microkernel architecture is a design approach used in operating systems.It focuses on keeping the…
Q: Explain the client-server model in the context of system architecture.
A: System architecture alludes to the design and construction of a system, encompassing its components,…
Q: Write a program that The name of the C++ file must be YourlslandID_searching.cpp defines and…
A: In this question we have to write a C++ code for the given instructionDefine and initialize a…
Q: Explore the concept of continuous integration/continuous deployment (CI/CD) and its impact on the…
A: 1) The software development process is a set of systematic activities and steps that are followed to…
Q: Explore the role of DHCP (Dynamic Host Configuration Protocol) in automatically assigning IP…
A: Dynamic Host Configuration Protocol (DHCP) is a network protocol that plays a crucial role in…
It will use a class called NameHelper (which you will write). This class will provide methods to load the data files and to fetch name rankings by year. The JavaFX class will be using NameHelper according to the following UML, so make sure your data helper has the methods defined below: What does the (~) mean in the attached diagram.
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- The compareTo method. First you compare this.ticker which is a String, then if they are the same then you compare by the this.purchasePrice which is a double hashCode public int hashCode() The hashCode method using the Code-> Generate equals and hashCode with no changes Overrides: hashCode in class Object Returns: int Representing the hashCode compareTo public int compareTo(Stock another) The compareTo method not auto generated Compares first by ticker and if the tickers are the same secondarily compares by price Specified by: compareTo" in interface Comparable<stock> Parameters: another - the object to be compared. Returns: int Representing order Throws: IllegalArgumentException"- if another is null.for (String name : likedBy) { String likedUser= name.trim(); Set<String> likes = likesMap.getOrDefault(likedUser, new HashSet<>()); Here you create a new Set for likes. This is in the iteration over the likers though so it results in many missing entries. [ How do i Fix this ] import java.io.BufferedReader; import java.io.FileReader; import java.io.IOException; import java.util.ArrayList; import java.util.HashMap; import java.util.HashSet; import java.util.List; import java.util.Map; import java.util.Set; public class FacebookLikeManager { private Map<String, Set<String>> likesMap; public FacebookLikeManager() { likesMap = new HashMap<>(); } public void buildMap(String filePath) { try (BufferedReader reader = new BufferedReader(new FileReader(filePath))) { String line = reader.readLine(); while (line != null) { String[]…JAVA PROGRAM ASAP There is an extra space in the program down below as shown in the screesshot. Please modify this program even more ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) { System.out.println(); return; } String encodedOutput = encodeText(textForEncoding);…
- JAVA PROGRAM ASAP There is still an extra space in the program after further modification down below as shown in the screesshot. Please modify this program even more please ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static final HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) { System.out.println(); return; } String…JAVA PROGRAM ASAP There is still an extra space in the program after the last modi down below as shown in the screesshot. Also Take out that dam space from the program because the program does not need it. Please modify this program even more please ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static final HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) {…JAVA PROGRAM ASAP There is still an extra space in the program after the last modification down below as shown in the screenhot. Also Take out that dam space from the program because the program does not need it. Please modify this program even more please ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static final HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding))…
- JAVA PROGRAM ASAP Please Modify this program ASAP BECAUSE it does not pass all the test cases when I upload it to hypergrade Please modify so it passes all the test cases because it says 0 out of 2 passed. The program must pass the test case when uploaded to Hypergrade. Thank you import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseCodeConverter { private static HashMap<Character, String> morseMap = new HashMap<>(); public static void main(String[] args) { loadMorseCodes(); Scanner scanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String input = scanner.nextLine().toUpperCase(); String morseCode = convertToMorse(input); System.out.println(morseCode); } private static void loadMorseCodes() { try (BufferedReader reader = new BufferedReader(new…JAVA PROGRAM ASAP Please give me a new program ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. I have provided the failed test cases as a screenshot. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseCodeConverter { private static HashMap<Character, String> morseMap = new HashMap<>(); public static void main(String[] args) { loadMorseCodes(); Scanner scanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code:"); String input = scanner.nextLine().toUpperCase(); String morseCode = convertToMorse(input); System.out.println(morseCode); } private static void loadMorseCodes() { try (BufferedReader reader = new BufferedReader(new FileReader("morse.txt"))) {…JAVA PROGRAM ASAP Please modify this program ASAP BECAUSE the program down below does not pass all the test cases when I upload it to hypergrade. The program must pass the test case when uploaded to Hypergrade. import java.util.HashMap;import java.io.BufferedReader;import java.io.FileReader;import java.io.IOException;import java.util.Scanner;public class MorseEncoder { private static HashMap<Character, String> codeMappings = new HashMap<>(); public static void main(String[] args) { initializeMappings(); Scanner textScanner = new Scanner(System.in); System.out.println("Please enter a string to convert to Morse code::"); String textForEncoding = textScanner.nextLine().toUpperCase(); if ("ENTER".equals(textForEncoding)) { System.out.println(); return; } String encodedOutput = encodeText(textForEncoding); System.out.println(encodedOutput); } private static void initializeMappings() {…
- Bean Scopes Suppose you are working on an application that involves encrypting passwords before storing them in the database. The encryption part is carried out by a PasswordEncryptor class. This class provides you with a method that takes a plaintext password and returns an encrypted one. You need to create a bean of this class. What should be the scope of this bean? Choose the correct option from those given below. (Hint: PasswordEncryptor only contains methods and no fields to maintain state. Hence, we need to create a stateless bean of PasswordEncryptor. Recall which bean scope is used for creating stateless beans.) 1) Prototype 2) Singleton 3) Request 4) SessionProvide right solutionpython: def typehelper(poke_name): """ Question 5 - API Now that you've acquired a new helper, you want to take care of them! Use the provided API to find the type(s) of the Pokemon whose name is given. Then, for each type of the Pokemon, map the name of the type to a list of all types that do double damage to that type. Note: Each type should be considered individually. Base URL: https://pokeapi.co/ Endpoint: api/v2/pokemon/{poke_name} You will also need to use a link provided in the API response. Args: Pokemon name (str) Returns: Dictionary of types Hint: You will have to run requests.get() multiple times! >>> typehelper("bulbasaur") {'grass': ['flying', 'poison', 'bug', 'fire', 'ice'], 'poison': ['ground', 'psychic']} >>> typehelper("corviknight") {'flying': ['rock', 'electric', 'ice'], 'steel': ['fighting', 'ground', 'fire']} """ # pprint(typehelper("bulbasaur"))#…code: public class PasswordGeneratorAndStorage {/*** Adds an application to the applications ArrayList. If index is -1, add application* to the end of applications. Else is index is within the size of applications, add* application at that index in applications. Otherwise, return. However, if applications * or application is null, return.* * @param applications* @param application* @param index*/public static void addApplication(ArrayList<String> applications, String application, int index) {// TODO: FILL IN BODY}/*** Generates a random password of length passwordLength and adds it to the end of* passwords if index is -1, or adds it to the index of passwords if index is within the* size of passwords (similar to how the addApplication adds an application). To generate* the random password, use rand to generate a random int within the size of characters. You* can then use this int to grab the char at that index in characters and concatenate that* to your String password variable.…











