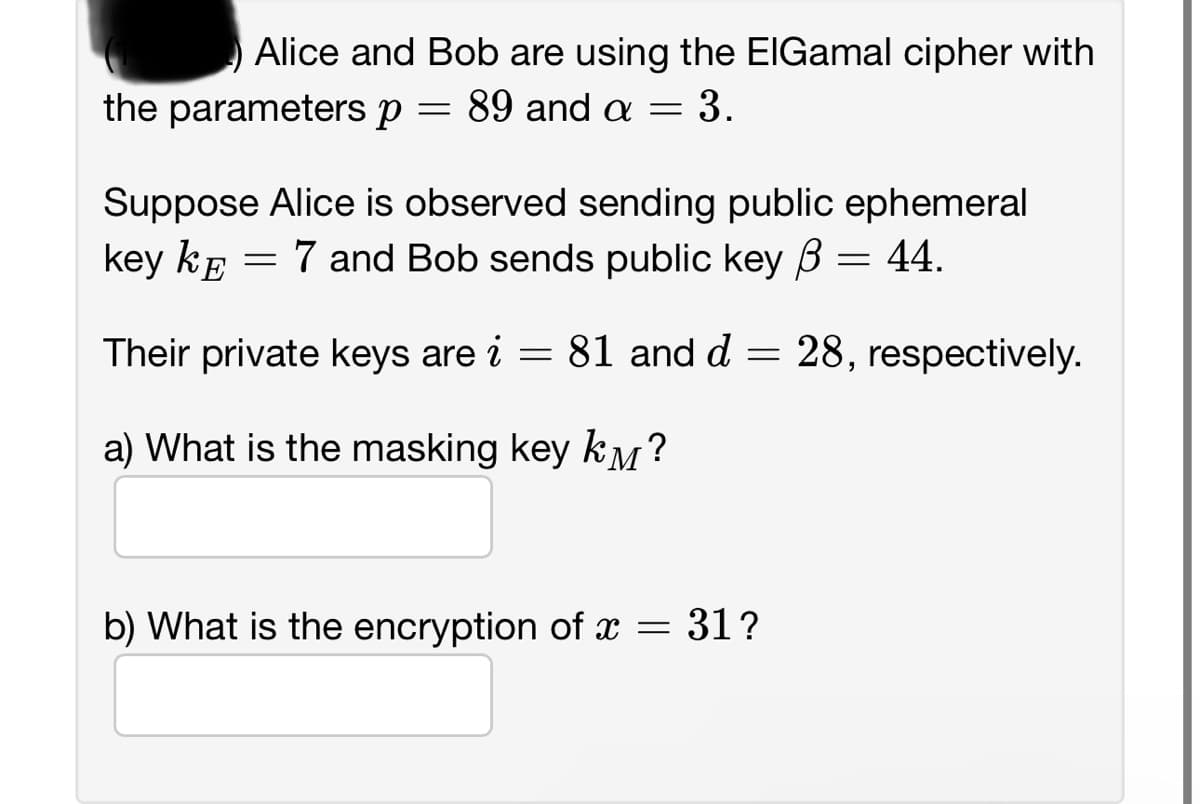
Alice and Bob are using the ElGamal cipher with 89 and a = 3. the parameters p = = Suppose Alice is observed sending public ephemeral key kô = 7 and Bob sends public key ß = 44. = Their private keys are i a) What is the masking key k? 81 and d 28, respectively. =
Q: Scrutinize the efficacy of macOS security mechanisms in safeguarding against malware and cyber…
A: The security of operating systems is of paramount importance in today's digital landscape, where…
Q: What are common encryption protocols used in securing network communications, and how do they work?
A: Securing network communications is paramount in today's digital age, where sensitive data and…
Q: Discuss the security concerns associated with object serialization and methods to mitigate potential…
A: The process of transforming an object's state (its data fields or attributes) into a format that can…
Q: What would be suitable for capstone? Project Purpose and Justification crime heat map cyber…
A: Choosing a suitable capstone project is an essential step towards demonstrating the comprehensive…
Q: Discuss the challenges and strategies involved in ensuring data security and compliance in a…
A: In a multi-cloud environment, data security and compliance refer to the intricate set of measures…
Q: What is the area of this figure? 9 ft 2 ft 2 ft 3 ft 2 ft 3 ft 2 ft 4 ft 2 ft 2 ft 3 ft 4 ft
A: To solve the given question we have to check every shape one by one leading to complete shape Here…
Q: Using ABDULAI as the keyword in the application of Playfair cipher, perform an encryption of the…
A: encryption using the Playfair cipher with the keyword "ABDULAI is given below with explanation
Q: Explore the concept of "threshold cryptography" and its use cases in secure multi-party computation.
A: A cryptographic strategy known as "threshold cryptography" includes sharing private keys and…
Q: Discuss the challenges and best practices in implementing NAC solutions.
A: Network Access Control (NAC) is a method used to enhance network security by restricting the…
Q: Discuss advanced strategies for mitigating complex DDoS attacks that employ techniques like…
A: In today's digital landscape, Distributed Denial of Service (DDoS) attacks have evolved to become…
Q: Discuss the importance of software package updates and maintenance in ensuring system security.
A: The process of releasing and installing new versions or fixes for software programs and operating…
Q: How does a distributed denial of service (DDoS) attack differ from a denial of service (DoS) attack?
A: In the realm of cybersecurity, both Distributed Denial of Service (DDoS) and Denial of Service (DoS)…
Q: Explore the field of microchip security and how hardware-based security features are implemented to…
A: Microchip security is a critical aspect of modern technology, especially in an era where sensitive…
Q: Discuss the importance of web security and the common security vulnerabilities that web applications…
A: Importance of Web SecurityWeb security is a critical concern for both individuals and organizations.…
Q: Learn how the Bottler Company defends its communications systems by using Internet Protocol security…
A: In today's interconnected digital landscape, securing communication systems is of paramount…
Q: Discuss the security implications of virtualization, especially in the context of VM escape…
A: Virtualization technology has revolutionized the way data centers operate, offering numerous…
Q: On last evening’s edition of Frightline, the investigative reporter detailed several nasty IT…
A: The presented scenario involves an investigative report highlighting various malicious IT attacks…
Q: Describe the concept of cryptographic key management and its importance.
A: In this question concept of cryptographic key management needs to be explained along with its…
Q: Investigate the ethical and security implications of quantum computing's potential to disrupt…
A: Quantum computing refers to a revolutionary approach to computation that harnesses the principles of…
Q: Read about the recent Colonial Pipeline ransomware attack and identify what CIA area(s) was…
A: The Colonial Pipeline ransomware attack in May 2021 sent shockwaves through the United States,…
Q: Discuss the security challenges associated with mobile devices, such as data encryption, app…
A: Mobile devices are small, portable electronic devices that are made to be used conveniently while…
Q: How can requirement analysis principles be applied in the context of cybersecurity to identify and…
A: To ensure the confidentiality, integrity, and availability of information and technology assets,…
Q: Discuss the importance of ethical hacking and penetration testing in identifying and mitigating…
A: Ethical hacking and penetration testing play a role in ensuring the security of software…
Q: What security risks are associated with using plaintext connection strings in application…
A: Application configuration files often contain sensitive information such as connection strings, API…
Q: Encrypt the message “ABCDEFGHIJKLMNOPQRST” using the columnar transposition cipher with the key “3 4…
A: To encrypt "ABCDEFGHIJKLMNOPQRST" with the columnar transposition cipher and key "3 4 2 5 1," start…
Q: Suppose you have p = 152 and g = 34 = 81 for the Diffie-Hellman key exchange. Without computing any…
A: Diffie-Hellman key exchange is a form of digital encryption in which two parties safely exchange…
Q: What are the challenges of securing embedded systems in critical applications like automotive and…
A: An embedded system is a microprocessor-based computer hardware that has software embedded in it and…
Q: Describe the objectives supported by the Master Test Plan, e.g., defining tasks and…
A: The Master Test Plan (MTP) in the context of a default letter for a student loan serves several…
Q: How can blockchain technology be used to verify the authenticity and provenance of printed artworks…
A: A blockchain can be defined in such a way that it is a distributed ledger with growing lists of…
Q: How can organizations mitigate the potential security vulnerabilities inherent in SOAP-based web…
A: SOAP (Simple Object Access Protocol) is a widely used protocol for exchanging structured information…
Q: Soto works as a database ad
A: Question 2:Soto works as a database administrator for a bank. He uses a check digit toa. verify that…
Q: What are some of the many ideas that have been proposed on the occurrence of cybercrime? In response…
A: The occurrence of cybercrime has become a pressing concern in the modern digital age. As technology…
Q: How do organizations implement "defense in depth" as a risk management strategy in cybersecurity?
A: => Cybersecurity refers to the practice of protecting computer systems, networks, data,…
Q: Explore the challenges and solutions in managing wireless network security, including encryption and…
A: Wireless network security holds importance in the field of computer science and networking.It is…
Q: Evaluate the ethical considerations and privacy concerns related to web technologies, including data…
A: Web technologies encompass a wide range of tools, protocols, and systems used to facilitate the…
Q: Evaluate the security implications of mouse-based biometric authentication methods, such as mouse…
A: Mouse-based biometric authentication methods, such as mouse dynamics and fingerprint recognition,…
Q: Explain the concept of data encryption and its significance in modern IT security.
A: When cyberattacks and data breaches are normal, safeguarding delicate data has become fundamental.…
Q: What role does data security play in managing sensitive information? Provide best practices for…
A: In this question role of data security in managing sensitive information needs to be explained.…
Q: Discuss the impact of software safety concepts in the development of autonomous vehicles and other…
A: The amalgam of software safety and cybersecurity is quintessential in navigating the modern…
Q: Describe the process of public key infrastructure (PKI) and its role in secure communication
A: A public key infrastructure (PKI) can be defined in such a way that it is a set of hardware,…
Q: Explore the concept of biometric input devices for security and authentication. How can biometrics…
A: Biometric input devices have revolutionized security and authentication by providing a more secure…
Q: How can blockchain technology be applied to network recovery and security, especially in…
A: Blockchain technology can be implemented for community restoration and security in decentralized and…
Q: What are the security considerations when implementing virtualization in an enterprise environment?
A: Virtualization is a creation of virtual rather than the actual version of something such as a…
Q: The Chinese Remainder Theorem is often used as a way to speed up modular exponentiation. In this…
A: Fermat's Little Theorem states that if p is a prime number, then for any integer a not divisible by…
Q: Explain how database security and access control are implemented in modern database systems. Provide…
A: Database security consists of controls organization implement to prevent the unauthorized access or…
Q: What are the security implications and considerations when implementing virtualization technologies?
A: Virtualization technologies have become integral components of modern IT infrastructures, offering…
Q: Explore the concept of "Mobile Threat Intelligence" and its use in proactively identifying and…
A: Mobile threat intelligence (MTI) can be defined in such a way that it is the gathering, evaluation,…
Q: What is a VPN (Virtual Private Network) and how does it enhance cybersecurity in a corporate…
A: A Virtual Private Network (VPN) is a technology that enables users to set up an encrypted connection…
Q: Describe the security implications of VLANs and common strategies for securing VLAN traffic and…
A: VLANs provide valuable network segmentation, they pose security challenges when not properly…
Q: In a globally distributed database system, how do you handle data security and privacy concerns?…
A: Securing data in a globally dispensed database device involves addressing various elements of…
Step by step
Solved in 3 steps
