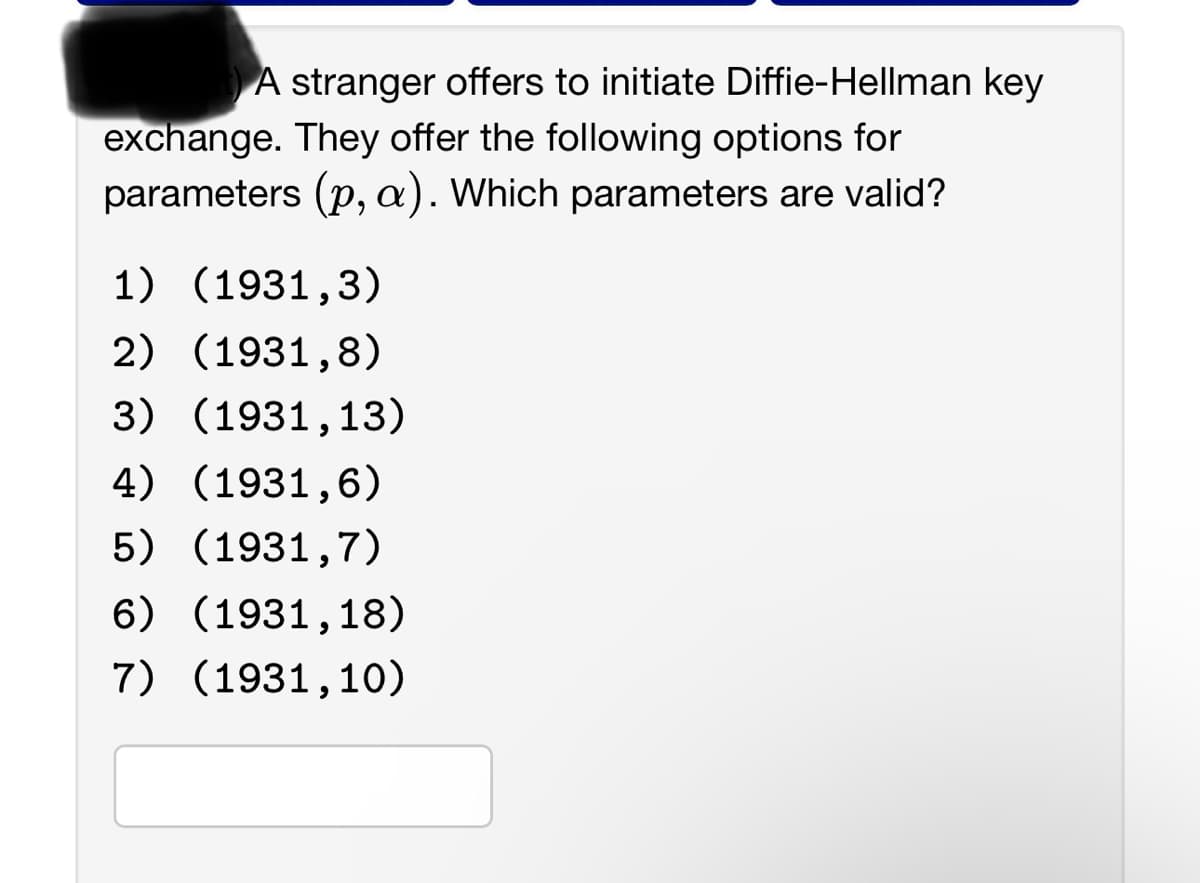
A stranger offers to initiate Diffie-Hellman key exchange. They offer the following options for parameters (p, a). Which parameters are valid? 1) (1931,3) 2) (1931,8) 3) (1931,13) 4) (1931,6) 5) (1931,7) 6) (1931,18) 7) (1931,10)
Q: Explore the field of microchip security and how hardware-based security features are implemented to…
A: Microchip security is a critical aspect of modern technology, especially in an era where sensitive…
Q: What tools and techniques can be used to evaluate the security and stability of software…
A: The word "software" refers to a structured collection of data, algorithms, programs, and…
Q: Explain the limitations and potential vulnerabilities of public key encryption systems.
A: Public key encryption, commonly referred to as asymmetric encryption, is a cryptographic technique…
Q: What you mean by Cryptography in cyber security. Elaborate in detail.
A: Cryptography is a technique which is used to secure the information or code in such a way that the…
Q: Explore the concept of "zero trust network security" and its role in modern network recovery and…
A: Zero Trust Network Security is a cybersecurity framework that aims to boost network security by…
Q: Describe macOS security features, such as Gatekeeper, FileVault, and XProtect, and their roles in…
A: macOS, Apple's operating system, boasts an array of robust security features designed to protect…
Q: Dive into the challenges and solutions related to network security, including intrusion detection…
A: Network security is a critical component in today's digital landscape, as organizations and…
Q: Discuss the role of virtual machine replication for disaster recovery.
A: Virtual machine (VM) replication plays a crucial role in disaster recovery (DR) strategies for…
Q: Question : Write main benefits of being a White Hat Hacker?
A: In this question primary benefits of White Hat Hacker need to be explained.White Hat Hacker: A White…
Q: How does the use of keys affect the encryption and decryption process?
A: The use of keys is a fundamental aspect of encryption and decryption processes, playing a critical…
Q: Describe the importance of "sandboxing" in package execution, especially for security.
A: "Sandboxing" is a critical practice in software and package execution, especially for security…
Q: What are the common types of malware, and how can they be prevented or removed from a computer…
A: Malware, short for malicious software, refers to a broad category of software programs or code…
Q: Discuss the security protocols and mechanisms used to secure data transmission over networks, such…
A: Securing records transmission over networks is crucial to defending touchy facts from unauthorized…
Q: What is the significance of cybersecurity in the field of information technology, and why is it a…
A: The significance of cybersecurity in the field of Information Technology (IT) is immense, and its…
Q: g language in Pseudocode
A: As per the given information we need to write the Pseudocode for the function that computes the…
Q: How do distributed systems handle security concerns, including data breaches and unauthorized…
A: Security is a critical concern in distributed systems due to their decentralized and interconnected…
Q: Discuss the security protocols used in network communication, such as SSL/TLS, IPsec, and their role…
A: Network communication plays a pivotal role in today's interconnected world, enabling the exchange of…
Q: How can requirement analysis principles be applied in the context of cybersecurity to identify and…
A: To ensure the confidentiality, integrity, and availability of information and technology assets,…
Q: Explain the importance of web security, including common threats like Cross-Site Scripting (XSS) and…
A: Web security is of paramount importance because the internet is a global platform that facilitates…
Q: 1. Describe the Diffie-Hellman algorithm b. Consider a Diffie-Hellman scheme with a common prime q…
A: The Diffie-Hellman key exchange algorithm is a cryptographic method that allows two parties to…
Q: When using loT products, companies must manage risks related to the 5Vs of big data. Choose the best…
A: In today's data-driven business environment, companies are increasingly relying on the use of big…
Q: All that is required is a Report on the findings from the query. That is, a sentence or two on th…
A: Queries are used to fetch crypto data. This plays a crucial role in the cryptocurrency ecosystem,…
Q: Using ABDULAI as the keyword in the application of Playfair cipher, perform an encryption of the…
A: encryption using the Playfair cipher with the keyword "ABDULAI is given below with explanation
Q: Explain the role of Mobile Device Management (MDM) systems in mobile device administration and…
A: Mobile Device Management (MDM) systems are critical to the administration and security of mobile…
Q: plain the principles of distributed security and authentication. How can distributed systems ensure…
A: Answer is explained below in detail
Q: Soto works as a database ad
A: Question 2:Soto works as a database administrator for a bank. He uses a check digit toa. verify that…
Q: Read about the recent Colonial Pipeline ransomware attack and identify what CIA area(s) was…
A: The Colonial Pipeline ransomware attack in May 2021 sent shockwaves through the United States,…
Q: What are the key considerations for implementing secure mobile communication channels within an…
A: Mobile Device Management plays a pivotal position in ensuring the security of these channels. in…
Q: How can web development teams effectively manage and mitigate security risks throughout the entire…
A: To safeguard websites and user data, managing and mitigating security risks in web development is…
Q: What are the potential security risks associated with wireless printing in office environments, and…
A: In modern office environments, wireless printing has become a convenient and widely adopted…
Q: Explain the concept of serverless security and the best practices for securing serverless…
A: Serverless architecture is an execution model where cloud providers manage the infrastructure for…
Q: Explore the concept of "threshold cryptography" and its use cases in secure multi-party computation.
A: A cryptographic strategy known as "threshold cryptography" includes sharing private keys and…
Q: Discuss the principles of cybersecurity and the importance of implementing a layered security…
A: Protecting computer systems, networks, data, and digital assets from hacking, damage, unauthorised…
Q: 1. Answer the following: a. What is a firewall? What is a firewall policy? Give an example. b. What…
A: In order to safeguard computer networks and systems from unauthorized access and potential online…
Q: Discuss data privacy and the legal and ethical considerations that organizations must address when…
A: Data privacy pertains to the way in which personal information is obtained, used, and disseminated,…
Q: How do security and privacy concerns influence the design of systems, especially in sensitive…
A: When it comes to designing systems in areas like healthcare and finance, security and privacy…
Q: Describe the security challenges posed by the widespread use of IoT devices.
A: The term "Internet of Things" (IoT) refers to the process of connecting commonplace electronics to…
Q: Why did hacking tactics change?
A: Hacking tactics have evolved significantly over time due to various factors that have shaped the…
Q: What is the significance of cross-site scripting (XSS) vulnerabilities in web applications, and how…
A: Cross-site scripting (XSS) is a customary safety vulnerability in web packages that takes place…
Q: Explain the security risks related to object deserialization and the measures that can be taken to…
A: In this question security risks to object deserialization need to be explained along with measures…
Q: An IDPS or intrusion detection and prevention system, constantly checks source IP addresses on all…
A: An Intrusion Detection and Prevention System (IDPS) is a vital cybersecurity tool designed to…
Q: Explore the role of Windows Update for Business (WUfB) and its advantages in managing Windows…
A: Windows Update for Business (WUfB) in simpler terms and highlight its benefits for managing Windows…
Q: Explore the concept of biometric input devices, such as fingerprint scanners and facial recognition…
A: In this question concept of biometric input devices needs to be explained by emphasizing their…
Q: Suppose you have p = 152 and g = 34 = 81 for the Diffie-Hellman key exchange. Without computing any…
A: Diffie-Hellman key exchange is a form of digital encryption in which two parties safely exchange…
Q: What is SQL injection, and how can it be prevented in database development?
A: SQL injection is a type of cyberattack that occurs in the context of database-driven applications.…
Q: Discuss the security implications and challenges of virtualization, including VM escape attacks.
A: Virtualization is a technology that enables run machines (VMs) on a single physical server.It offers…
Q: The SOAR system from Pillsbury is tailored to
A: The SOAR (State, Operator, And Result) system developed by Allen Newell and the Herbert A. Simon at…
Q: Discuss the security implications of mobile device data encryption, both at rest and in transit.
A: Data encryption is a crucial aspect of mobile device security. It helps protect sensitive…
Q: Internet security systems are becoming increasing important since the threats to internet security…
A: A firewall is a security system that acts as a protective barrier between a trusted network and the…
Q: Assess the challenges and solutions related to securing mobile devices used by remote or mobile…
A: Securing mobile devices used by remote or mobile workers, especially those operating in high-risk…
Step by step
Solved in 3 steps
